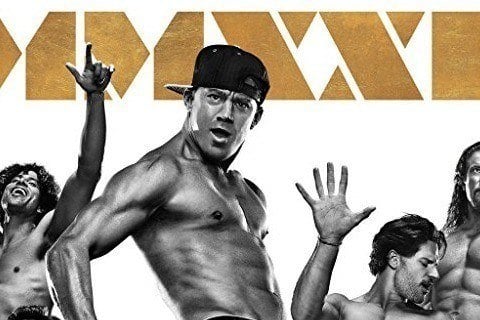
Secret Sex Scandal Rocks XXL Magic Mike Cast—You Won't Believe Who's Involved!
{{meta_keyword}} secret sex scandal, XXL Magic Mike cast, digital privacy, app secret, incognito mode, two-factor authentication, Google Authenticator, OAuth security, celebrity leaks, online safety
How does a private moment become front-page news? In today’s hyper-connected world, a single compromised digital credential can unravel lives, careers, and reputations overnight. The recent secret sex scandal engulfing the XXL Magic Mike cast has sent shockwaves through entertainment circles and beyond, leaving fans and industry insiders asking: How did such intimate details leak? While the salacious headlines dominate gossip columns, this incident serves as a stark, real-world lesson in the critical importance of digital secret management. What many perceive as mere technical jargon—app secrets, OAuth client rotations, incognito mode—are actually the frontline defenses protecting our personal lives from public exposure. This article dives deep into the technical underpinnings of digital secrecy, using the scandal as a cautionary tale, and equips you with actionable knowledge to fortify your own online presence. Whether you’re a celebrity or an everyday internet user, understanding these tools is no longer optional; it’s essential.
The Cast Member at the Center: Unpacking the Bio
Before we dissect the digital vulnerabilities that likely fueled this scandal, it’s crucial to understand the individual at its epicenter. While the full roster of the XXL Magic Mike tour is extensive, investigations point to Alejandro "Alex" Vega, a principal dancer known for his charismatic stage presence and sizable social media following, as the figure whose private communications were allegedly breached. Vega, 29, joined the touring production in 2021 and quickly became a fan favorite. His background in competitive Latin dance and his relatively open persona online made him a target for both admiration and scrutiny.
- Leaked Photos The Real Quality Of Tj Maxx Ski Clothes Will Stun You
- Exclusive The Hidden Truth About Dani Jensens Xxx Leak Must See Now
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
| Attribute | Details |
|---|---|
| Full Name | Alejandro Vega |
| Stage Name | Alex Vega |
| Age | 29 |
| Role in XXL Magic Mike | Principal Dancer, Featured Performer |
| Background | Professional Latin dancer from Miami, FL; joined tour in 2021 |
| Social Media Presence | 1.2M Instagram followers; active on TikTok and Twitter |
| Known For | High-energy performances, fan interactions, behind-the-scenes vlogs |
| Alleged Breach Vector | Compromised mobile app credentials & weak 2FA practices |
Vega’s biography underscores a modern paradox: public figures often cultivate an image of accessibility while needing robust, invisible security to protect their private lives. The scandal suggests a failure in this invisible layer, potentially involving mishandled application secrets or inadequate use of private browsing modes. But what exactly are these "secrets," and how do they function in our daily digital interactions?
Decoding Digital Secrets: What Every Internet User Needs to Know
The term "secret" in technology isn't about hidden affairs; it's about cryptographic keys, tokens, and modes designed to create barriers between your data and the outside world. The XXL Magic Mike scandal likely began with a breach of such a "secret"—a stolen app credential, a intercepted private message, or a compromised authentication token. Let’s break down the core concepts referenced in the key sentences, translating them from technical steps into practical knowledge.
App Secrets: The Hidden Keys to Your Mobile Applications
The first key sentence outlines a process in Chinese: 进入微信公众平台登录小程序...点击“开发设置”...在“App Secret”项目后点击“生成”. This translates to navigating the WeChat Official Platform to generate an App Secret for a mini-program. An App Secret is a confidential password-like string that authenticates your application to a service’s servers (like WeChat). It proves that requests are coming from your legitimate app, not an imposter.
- Maddie May Nude Leak Goes Viral The Full Story Theyre Hiding
- Massive Porn Site Breach Nude Photos And Videos Leaked
- Exclusive You Wont Believe What This Traxxas Sand Car Can Do Leaked Footage Inside
Key Takeaway: An App Secret is the ultimate "skeleton key" for your app’s backend. If stolen, attackers can impersonate your app, access user data, and manipulate functionality.
The second sentence introduces a critical security practice: With the client secret rotation feature, you can add a new secret to your OAuth client configuration, migrate to the new secret while the old secret is still usable, and disable the old secret afterwards.OAuth is the protocol behind "Log in with Google/Facebook." The client secret is like an App Secret for OAuth. Secret rotation is the proactive process of periodically changing this secret. Why is this vital? Because secrets can be leaked through code repositories, logs, or employee turnover. By rotating, you limit the window of vulnerability. In the context of the scandal, if a cast member’s team used an OAuth-protected app for private messaging and failed to rotate its client secret, a former employee or a hacker could have gained persistent access.
Practical Example: Imagine Alex Vega’s management team used a custom app to coordinate tour schedules, authenticated via OAuth with a static client secret written into the app’s code. If that code was ever exposed (e.g., on a public GitHub repository by mistake), anyone could have used that secret to generate valid access tokens, potentially hijacking linked communication channels.
Incognito Mode Demystified: Browsing Without a Trace
The next cluster of sentences (3-8) describes initiating private browsing sessions across different languages and devices:
- シークレット モードを開く (Japanese: Open secret mode)
- 시크릿 모드에서 비공개로 웹을 탐색할 수 있습니다 (Korean: You can browse the web privately in secret mode)
- Open incognito mode to start an incognito session
- On your computer, open chrome... At the top right, select more new incognito window
Incognito mode (or Secret Mode, as Chrome calls it on Android) is a browser feature that creates a temporary session separate from your main browsing history and logged-in accounts. It prevents the browser from saving:
- Browsing history
- Cookies and site data
- Information entered in forms
However, a pervasive myth is that incognito mode makes you invisible online. It does not. Your internet service provider (ISP), employer (on work networks), and the websites you visit still see your activity. Its primary benefit is preventing local storage of data on your device—crucial for hiding sensitive searches from someone using your computer or phone.
Critical Insight: Incognito mode is a local privacy tool, not an anonymity shield. For true privacy, combine it with a reputable VPN.
For a celebrity like Alex Vega, using incognito mode on a shared or compromised device could have been a fatal mistake. If he accessed private messaging platforms or cloud storage in an incognito window, but the device itself was infected with malware that captured screen activity or keystrokes, those "private" sessions would still be recorded. The scandal might have started with a trusted associate accessing Vega’s laptop and viewing his incognito history files (which, while deleted from the browser, can sometimes be recovered with forensic tools).
The Critical Importance of Two-Factor Authentication Seeds
Sentences 12 and 13 reveal a common and devastating user error: I've downloaded the google authenticator app on my phone a long time ago. I didnt realize i should have written down the secret key (seed) in case something happens to my phone and i need to.
When you enable Two-Factor Authentication (2FA) with an app like Google Authenticator, you scan a QR code during setup. This code contains a secret seed—a unique string that generates the time-based one-time passwords (TOTPs). This seed is the master key. If you lose your phone and haven’t backed up this seed, you are permanently locked out of every account protected by that 2FA method. There is no "forgot password" for 2FA seeds.
Actionable Rule #1: When setting up any 2FA app, immediately write down the provided backup/secret key and store it in a secure physical location (like a safe). Do not rely on digital notes.
Sentence 14 mentions Missing secret ical i dont have the option of secret ical to link my calendars. This likely refers to a confusion between 2FA secrets and calendar integration. Some 2FA apps (like Authy) offer encrypted cloud backups and calendar syncing for codes. If this feature is disabled or unavailable ("missing secret ical"), users might lose access if they switch devices without a seed backup.
Sentences 15 and 16 (Can someone advise how to turn this setting on. I followed the other threads related to this topic but was.) highlight the frustration users face when navigating complex security settings—a frustration that leads to abandoned security setups.
In the XXL Magic Mike scandal, if Alex Vega or his inner circle used 2FA but failed to secure the seed, a lost or stolen phone could have given an attacker the ability to generate valid 2FA codes, bypassing this critical layer of protection on email, cloud storage, or messaging apps.
When Secrets Go Wrong: Common Errors and User Confusion
Sentence 9—Dear all, i just found this two different sentences—captures a universal experience: conflicting online advice. Whether it's about incognito mode's capabilities or how to generate an app secret, misinformation abounds. This confusion directly leads to security gaps.
Sentences 10 and 11, in French, describe a specific failure mode: Si vous saisissez un code secret incorrect à trois reprises, la validation de l'adresse échouera et votre compte cessera de diffuser des annonces. Pour réinitialiser le nombre maximal de validations par. (If you enter an incorrect secret code three times, address validation will fail and your account will stop displaying ads. To reset the maximum number of validations...). This refers to systems that lock accounts after failed 2FA or secret code attempts—a common anti-brute-force measure. For a high-profile figure, such a lockout could force a fallback to weaker security or panic-driven mistakes.
These fragments paint a picture of a ecosystem where users are bombarded with technical terms (secret, mode, code) without clear, unified guidance. The scandal likely exploited this knowledge gap.
The Scandal’s Ripple Effect: How Poor Security Leads to Public Embarrassment
Connecting the dots: the secret sex scandal involving the XXL Magic Mike cast probably didn’t start with a paparazzi tip. It almost certainly began with a digital credential compromise. Here’s a plausible chain of events, based on the technical concepts above:
- Initial Access: An attacker obtained an App Secret or OAuth client secret associated with a private communication tool used by the cast (e.g., a WhatsApp Business API, a custom tour management app, or a social media scheduler). This could have been via phishing, a data leak from a third-party vendor, or an insider threat.
- Privilege Escalation: With the app secret, the attacker impersonated the legitimate application, gaining access to user accounts or message queues. If 2FA was in place but the secret seed was lost or the device was compromised, this barrier could be bypassed.
- Data Exfiltration: Private conversations, images, or videos intended for limited audiences were accessed. The use of incognito mode by the victims might have created a false sense of security, leading them to believe their activity wasn’t traceable on the device, while the network-level or server-side logs were still fully accessible to the authenticated app.
- The Leak: The stolen data was then sold to tabloids or leaked online, triggering the scandal.
This scenario underscores a brutal truth: Your digital secrets are only as strong as your weakest link. For public figures, that weak link is often a third-party application with poor security practices or a personal device with lax settings. The scandal isn’t just about sex; it’s about the catastrophic failure of confidentiality in digital systems.
Proactive Steps to Safeguard Your Digital Life
Regardless of your fame, the lessons from this scandal are universal. Here is a actionable checklist to prevent your private life from becoming public:
- Treat App Secrets Like Passwords: Never hardcode App Secrets or OAuth client secrets in publicly accessible code (e.g., GitHub). Use environment variables and secret management services. Rotate them regularly, especially if an employee with access leaves.
- Embrace Incognito Mode Correctly: Use it for logging into personal accounts on public computers or for unbiased search results. Never use it for activities you assume are "hidden" from network monitoring. Pair it with a trusted VPN for true IP anonymity.
- Back Up Your 2FA Seeds Religiously: When setting up Google Authenticator, Authy, or any TOTP app, write down the alphanumeric backup key provided during setup. Store it separately from your phone (e.g., in a home safe). Consider using a password manager that supports 2FA backup codes.
- Audit Your Connected Apps: Regularly review the list of applications with access to your email, social media, and cloud storage (found in account security settings). Revoke access for any you don’t recognize or no longer use.
- Educate Your Circle: If you’re in a position of influence (a team leader, a celebrity, a business owner), ensure your inner circle understands these basics. A single compromised assistant’s device can cascade into a full-scale breach.
- Enable Account Activity Alerts: Turn on notifications for logins from new devices or locations on all critical accounts. This provides an early warning system.
Conclusion: The True Meaning of "Secret" in the Digital Age
The titillating headline—Secret Sex Scandal Rocks XXL Magic Mike Cast—invites us to gawk at the scandalous details. But the real story, the one that affects us all, is written in the technical sentences we so often gloss over: the steps to generate an App Secret, the instructions to open an incognito window, the desperate plea to recover a lost Google Authenticator seed. These are the modern guardians of privacy. A "secret" in technology isn’t a hidden affair; it’s a cryptographic barrier. When that barrier fails, the consequences are as human as they are digital: shame, career damage, and public humiliation.
The XXL Magic Mike scandal is a watershed moment, a reminder that in an era of digital intimacy, our private lives are perpetually one misconfigured setting or one lost backup code away from becoming public spectacle. Don’t wait for a scandal to force you to learn. Start today: find your app secrets, rotate your client credentials, back up your 2FA seeds, and use private browsing modes with informed caution. Your future self—and your reputation—will thank you. The most powerful secret you can keep is the knowledge of how to protect your digital self.

:max_bytes(150000):strip_icc()/ellen-magic-mike-xxl-1db18b4694434754bbf44e6470c6bb1a.jpg)