SHOCKING NUDE PHOTOS: Young Jamie Foxx's Private Moments Just Leaked Online!
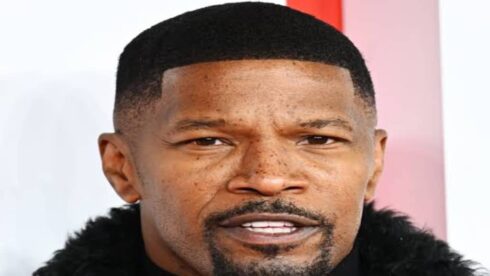
Is no one safe from the digital intruder? When the first blurry, grainy image began circulating on obscure forums and social media accounts, the question on everyone's mind was a chilling one: could this be real? The claim was as audacious as it was invasive—private, explicit photographs of a young Jamie Foxx, the acclaimed Oscar-winning actor and multi-hyphenate entertainer, had been stolen and unleashed upon the internet. This isn't just another celebrity scandal; it's a stark reminder of the persistent, predatory threat of celebrity nude leaks that has haunted Hollywood for over a decade. The alleged photo, described in salacious posts as showing the star in a compromising position with a "brunette beauty," immediately ignited a firestorm of speculation, concern, and the familiar, ugly machinery of online exploitation. But behind this specific allegation lies a much larger, more devastating story about privacy, cybersecurity failures, and the human cost of digital voyeurism.
The alleged leak involving Jamie Foxx, if authenticated, would place him on a notorious and growing list. It taps into a deep vein of public fascination and horror that began in earnest with the 2014 "Celebgate" or "The Fappening" scandal, where hundreds of private images of female celebrities were systematically stolen from iCloud accounts and disseminated globally. From that watershed moment, the pattern has repeated with grim regularity: high-profile individuals—from Kim Kardashian and Vanessa Hudgens to Gabrielle Union—have had their most intimate moments exposed, often through sophisticated phishing or brute-force hacking attacks. Each incident reignites fierce privacy debates, exposes the often-lacking security of personal cloud storage, and forces a conversation about the societal complicity in consuming such stolen material. This article delves into the shocking history of these leaks, the unexpected consequences for the victims, the legal and ethical quagmire they create, and what, if anything, can be done to protect personal digital sovereignty in an era of pervasive surveillance and hacking.
Jamie Foxx: The Latest Target in a Long Line of Digital Intrusions
The Allegation and Immediate Fallout
The specific claim, amplified by accounts like the now-controversial @thebestpaddle (associated with @foxxholeproductions, a production company linked to Foxx), sent shockwaves through fan communities and media outlets. Posts with captions like "Owner of @thebestpaddle founder of @foxxholeproductions somebody out now" seemed to directly tie the leak to Foxx's inner circle or business ventures, adding a layer of insider betrayal to the hacking narrative. TMZ, known for breaking the biggest stories in celebrity and entertainment news and offering exclusive access to the latest stories, photos, and video, was quick to report on the circulating images, framing it as a major breach. Their coverage, typical of their style, focused on the salacious details: "The Oscar winner, 49, left all inhibitions behind as he got steamy with a completely naked brunette beauty in the graphic session."
- Taylor Hilton Xxx Leak Shocking Video Exposed
- The Shocking Secret Hidden In Maxx Crosbys White Jersey Exposed
- Shocking Tim Team Xxx Sex Tape Leaked The Full Story Inside
However, it's crucial to approach such allegations with extreme caution. The digital landscape is rife with deepfakes, AI-generated pornography, and manipulated images that are indistinguishable from reality to the casual observer. The description itself—a "graphic session"—could easily be referencing a scene from a film or a private, consensual video that was never meant for public eyes, or it could be a complete fabrication designed to generate clicks and destroy reputations. This ambiguity is precisely what makes these leaks so toxic. Whether real or fake, the mere allegation causes reputational harm, forces a public response, and subjects the individual to relentless scrutiny and victim-blaming. Jamie Foxx's own recent public outburst, where he "went off this weekend after GloRilla allegedly had something chucked at her by a fan," demonstrates the volatile emotional state that such public invasions can foster, blending personal frustration with a broader sense of violated safety.
Biography Spotlight: Jamie Foxx
Before diving deeper into the leak's context, understanding the man at the center is key. Jamie Foxx is not a reality star or a musician primarily known for scandal; he is a serious, decorated actor with a career spanning decades.
| Attribute | Detail |
|---|---|
| Full Name | Eric Marlon Bishop |
| Date of Birth | December 13, 1967 |
| Profession | Actor, Singer, Comedian, Producer |
| Major Awards | Academy Award (Best Actor, Ray, 2004), BAFTA, Golden Globe, SAG Award |
| Notable Films | Ray, Django Unchained, Collateral, Dreamgirls, Baby Driver, Just Mercy |
| Music Career | Grammy-winning R&B singer & pianist; hit single "Blame It" |
| Production Company | Foxxhole Productions |
| Recent Work | They Cloned Tyrone (2023), The Burial (2023) |
This biography underscores the profound violation: this is an artist who has earned the highest honors in his craft, a father and public figure whose private life is being bartered for clicks. The alleged leak targets a "young Jamie Foxx," potentially from an earlier, less guarded era of his life, making the temporal violation even more acute.
- Shocking Desperate Amateurs Leak Their Xxx Secrets Today
- Nude Tj Maxx Evening Dresses Exposed The Viral Secret Thats Breaking The Internet
- Exclusive The Leaked Dog Video Xnxx Thats Causing Outrage
The Historical Epidemic: From "Celebgate" to the Present Day
The 2014 "Celebgate" Watershed Moment
To understand the current climate, one must go back to August 2014. A massive breach resulted in the online publication of private nude photographs of over 100 celebrities, primarily women including Jennifer Lawrence, Kate Upton, Kirsten Dunst, and Ariana Grande. The hack was traced to vulnerabilities in Apple's iCloud system, though Apple initially denied any "system breach," instead blaming targeted phishing attacks on user accounts. The Marie Antoinette actress—Kirsten Dunst—was among the most vocal victims. She famously slammed Apple’s security measures, tweeting, "Thank you @Apple for fixing this bug and for all the messages. So much better to be safe than sorry. xoxo" in a tone dripping with sarcasm and frustration. Her public shaming of a tech giant highlighted a critical truth: the burden of security was falling on the user, not the platform storing their data.
The consequences of Celebgate were far-reaching:
- Criminal Prosecutions: Several individuals were convicted under the Computer Fraud and Abuse Act (CFAA) and faced prison sentences. One key hacker, Ryan Collins, admitted to a phishing scheme that tricked victims into entering their iCloud credentials.
- Civil Lawsuits: Multiple celebrities filed lawsuits against Apple and other entities, alleging negligence in safeguarding user data. These lawsuits pushed for greater corporate accountability.
- The "Victim-Blaming" Culture: The public and media response was horrifyingly mixed. While many expressed outrage at the hackers, a significant undercurrent of victim-blaming emerged, questioning why the celebrities took the photos in the first place. This toxic narrative shifted focus from the criminal act to the victim's behavior.
- A Blueprint for Future Attacks: The success of the iCloud phishing method became a playbook. It demonstrated that targeting high-value individuals with simple social engineering could yield massive, globally disseminated results.
The Expanding List of Victims: From Franchise Leads to TV Stars
As the key sentence notes, "From big box office franchise leads to former teen TV stars, these actors and actresses were victims of nude photo leaks through the years." The list is a cross-section of fame:
- Kim Kardashian: Her 2016 leak was part of a larger hack that also targeted models and reality stars. She publicly addressed the violation, linking it to a broader issue of women's privacy.
- Vanessa Hudgens: The High School Musical star's private photos were leaked multiple times over the years, each incident a brutal reminder of her transition from teen idol to adult actress under a relentless public microscope.
- Gabrielle Union: The Being Mary Jane actress has been a vocal advocate for digital privacy after her images were compromised. She has spoken powerfully about the intersection of race, gender, and digital exploitation.
- Other Notable Cases: Jennifer Lawrence, who called the leak a "sex crime"; Emma Watson; Milla Jovovich; and countless others have endured similar violations. The pattern is clear: female celebrities are disproportionately targeted, though male stars like Chris Pratt (whose photos were part of the 2014 leak) and now allegedly Jamie Foxx, prove no one is immune.
The Unforeseen Consequences: Beyond the Initial Shock
Psychological and Professional Trauma
The immediate consequence is a profound sense of violation and trauma. Victims describe feelings of being "raped in cyberspace," with the images existing forever in the digital ether, accessible to employers, family members, and strangers. The psychological toll includes anxiety, depression, and a lasting sense of being unsafe in one's own home. Professionally, it can lead to:
- Typecasting or Stigma: Studios and brands may become hesitant to associate with a "controversial" figure, regardless of their victim status.
- Distraction from Work: The media frenzy forces the victim to address the leak instead of focusing on their craft or projects.
- Erosion of Trust: Relationships with partners, friends, and colleagues can be strained by the public exposure of private intimacy.
Legal and Platform Accountability Shifts
Each major leak has spurred incremental, often frustratingly slow, change:
- Two-Factor Authentication (2FA): Tech companies like Apple, Google, and Microsoft have aggressively pushed 2FA as a mandatory or strongly recommended security measure. While not foolproof, it raises the barrier for attackers.
- Improved Security Headers and Encryption: Cloud services have bolstered backend security and encryption protocols.
- Legal Precedents: The convictions from the 2014 hack set a precedent that such acts are serious federal crimes. However, the global nature of the internet means perpetrators often operate from jurisdictions with lax extradition treaties.
- "Revenge Porn" Laws: Many U.S. states and countries have enacted specific laws criminalizing the non-consensual distribution of intimate images. These laws are a critical tool, but enforcement remains a challenge.
The Societal Mirror: What Our Consumption Reveals
Perhaps the most unexpected consequence is the mirror it holds up to society. The "shocking live TV moments" like the Will Smith/Chris Rock Oscars slap or Janet Jackson's 2004 wardrobe malfunction become cultural touchstones debated for weeks. Yet, the non-consensual, permanent distribution of nude images is often consumed with a quieter, more insidious complicity. The traffic to websites hosting such material generates significant ad revenue. This creates a perverse economic incentive to host and share stolen content. The question becomes: are we, as an audience, passive consumers or active participants in a cycle of exploitation by clicking, sharing, or even just seeking out the material?
Protecting Your Digital Intimacy: Practical Steps in a Dangerous Landscape
While no one can be 100% secure, especially against determined state-level actors or persistent stalkers, individuals can dramatically reduce their risk profile. These steps are crucial for everyone, not just celebrities.
- Embrace Two-Factor Authentication (2FA) Everywhere: Do not just enable it; use an authenticator app (like Google Authenticator or Authy) instead of SMS-based 2FA, which is vulnerable to SIM-swapping attacks.
- Use Unique, Complex Passwords: A password manager (e.g., Bitwarden, 1Password) is non-negotiable. It generates and stores strong, unique passwords for every account.
- Audit Your Cloud and App Permissions: Regularly review which apps have access to your photo libraries, contacts, and location. Revoke permissions for apps that don't absolutely need them. On iOS: Settings > Privacy & Security > Photos. On Android: Settings > Apps & notifications > Permission manager.
- Encrypt Your Backups: Ensure any local backups (to an external hard drive) and cloud backups are encrypted. For iCloud, Apple states data is encrypted in transit and at rest, but the keys are held by them. For maximum security, use a zero-knowledge encrypted cloud service like Tresorit or Sync.com for your most sensitive files.
- Be Phishing-Aware: The primary vector for these leaks is social engineering. Be suspicious of emails or texts asking you to "verify your account" or "reset your password," even if they look legitimate. Always navigate to the official website or app directly, never through a link.
- Consider Air-Gapping for Ultra-Sensitive Content: For the most private images or videos, the only truly secure method is to never store them on an internet-connected device. Keep them on an encrypted, offline hard drive stored in a secure location.
Conclusion: The Battle for Digital Bodily Autonomy
The alleged leak of young Jamie Foxx's private moments is not an isolated incident. It is the latest salvo in a long, ongoing war against digital privacy and bodily autonomy. From the systemic hack of Celebgate that exposed Apple's vulnerabilities and society's misogyny, to the repeated victimization of stars like Kim Kardashian and Vanessa Hudgens, the pattern is devastatingly clear. The unexpected consequences—the psychological scars, the professional setbacks, the corrosive culture of consumption—often inflict more lasting damage than the initial leak.
The privacy debates this issue sparks are fundamental to our digital age. They force us to ask: Do we have a right to digital intimacy? Can a corporation be held liable for failing to protect user data with state-of-the-art security? Is viewing or sharing non-consensual pornography a victimless crime, or an act of complicity in theft and violation?
While TMZ and outlets like it break the biggest stories, and while social media accounts amplify the allegations, the real story is one of power imbalance. It's the power of hackers, the power of platforms that prioritize convenience over ironclad security, and the power of a public that often fails to see the human being behind the celebrity avatar. Jamie Foxx, the Oscar winner, the musician, the family man, is the latest to potentially face this ordeal. His experience, like those before him, must transcend tabloid fodder. It must be a catalyst for stricter laws, more ethical tech design, and a cultural shift that unequivocally sides with the victim and criminalizes the act of consumption. The fight for digital privacy is, at its core, a fight for human dignity in the 21st century. The question remains: are we ready to defend it?
Meta Keywords: celebrity nude leaks, iCloud hacking, privacy debates, Jamie Foxx leak, Celebgate, The Fappening, digital privacy, cybersecurity tips, non-consensual pornography, revenge porn laws, Kirsten Dunst Apple, Kim Kardashian leak, Vanessa Hudgens, Gabrielle Union, victim-blaming, two-factor authentication, phishing, TMZ, deepfakes, digital consent, Hollywood hacks.