TJ Maxx Payment LEAK EXPOSED: Your Credit Card Details Are Being Sold On The Dark Web!
Have you ever wondered if the incredible deals you score at T.J.Maxx come with a hidden, terrifying cost? What if the moment you entered your zip code to find a local store or created an account for free shipping, your personal data began a journey into the digital underworld? The shocking reality is that major retailers, including those we trust for our wardrobes, have been targets of colossal data breaches. A recent wave of incidents highlights a persistent threat: your payment card details, email addresses, and home information could be circulating on the dark web right now, sold to the highest bidder. This isn't just a hypothetical scare; it's an epidemic. In one of the largest claims ever, hackers alleged the theft of 2.9 billion personal records from a national data broker. For millions of shoppers who have swiped a card or entered an email at a favorite store, the question isn't if their data was breached, but when and what's being done with it now.
This article dives deep into the intersection of retail therapy and digital risk. We'll expose the history of data compromises at retailers like T.J.Maxx, unpack exactly what personal information is harvested during a simple shopping trip, and translate the complex world of dark web marketplaces into plain English. More importantly, we provide a critical, actionable guide: how to discover if your email has been hacked for free, the precise steps to take if your information is found on the dark web, and how to shop smartly in an era of relentless cyber threats. Your security is not an optional add-on; it's the most important purchase you'll make today.
The Allure and the Data Trail: What You Share When You Shop at T.J.Maxx
Before we confront the breach, we must understand the treasure trove of data collected every time you engage with a major retailer's ecosystem. T.J.Maxx, with its promise of incredible savings on women's fashion and top brands in clothing, shoes, handbags, and more, has built a loyal following. But this convenience and these deals are powered by your personal information.
- This Viral Hack For Tj Maxx Directions Will Change Your Life
- This Traxxas Slash 2wd Is So Sexy Its Banned In Every Country The Truth Behind The Legend
- Exclusive Tj Maxx Logos Sexy Hidden Message Leaked Youll Be Speechless
Consider the typical journey. You're lured by the promise of free shipping on $89+ orders. To claim it, you provide your email address, shipping address, and payment details. You create an account to track orders, which requires your first and last name, birth date, gender, email address, and zip code. You use the 'my stores' feature, entering your zip code to find local T.J.Maxx locations, sharing your precise geographic data. You browse new arrivals in clothing, shoes, beauty, handbags, jewelry, accessories, petite, plus size, juniors, and clearance sections, with every click and search logged to build a detailed profile of your style, size preferences, and spending habits.
This data is invaluable—to marketers and to criminals. Your name and address enable identity theft. Your email is a key to resetting passwords across all your accounts. Your payment card details—names, street addresses, email addresses, and card numbers—are the golden ticket for fraudsters. As independent researchers have noted, they've discovered mountains of data on the dark web that map out the statistical scope of payment card detail hacking. Every field you fill out, from your zip code to your birthday, is a potential vulnerability if the retailer's defenses are compromised.
The Checkout Conundrum: Convenience vs. Risk
The process is designed to be seamless. Shop now for amazing deals! the banners urge. But that seamless experience requires you to hand over the keys to your digital kingdom. When you click 'edit my information' to update your profile or use the store locator, you are actively feeding a database. If that database is breached, as has happened historically, that information is packaged and sold. The free returns in store and free returns at your local store policies are fantastic for customer service, but they also mean your return data—items, receipts, potentially linked to your original payment method—is also stored.
- You Wont Believe What Aryana Stars Full Leak Contains
- Viral Alert Xxl Mag Xxls Massive Leak What Theyre Hiding From You
- Super Bowl Xxx1x Exposed Biggest Leak In History That Will Blow Your Mind
The critical takeaway is that maxximizing your savings by shopping at off-price giants involves a trade-off: you receive deep discounts in exchange for a comprehensive personal data profile. The risk lies in what happens to that profile when a cyberdefense fails.
A History of Compromise: T.J.Maxx's Own Breach Legacy
The current anxiety is not without precedent. T.J.Maxx's parent company, TJX Companies, suffered one of the most infamous data breaches in retail history. Discovered in 2007 but dating back to 2005, hackers penetrated the company's systems, stealing an estimated 45.7 million credit and debit card numbers. This breach, which involved payment transactions going back to 2008, was a watershed moment that exposed the vulnerability of even massive corporations.
The stolen data, which included names, street address, email address, and card details, was allegedly used for fraudulent purchases across the globe. The financial and reputational cost was staggering, totaling hundreds of millions in settlements and security overhauls. This historical event is a stark reminder that no retailer, regardless of size or security budget, is immune. It set a precedent for the scale of damage possible and the longevity of the threat, as stolen data from 2008 can still be relevant today for crafting sophisticated phishing attacks.
The Dark Web Economy: How Your Data is Monetized
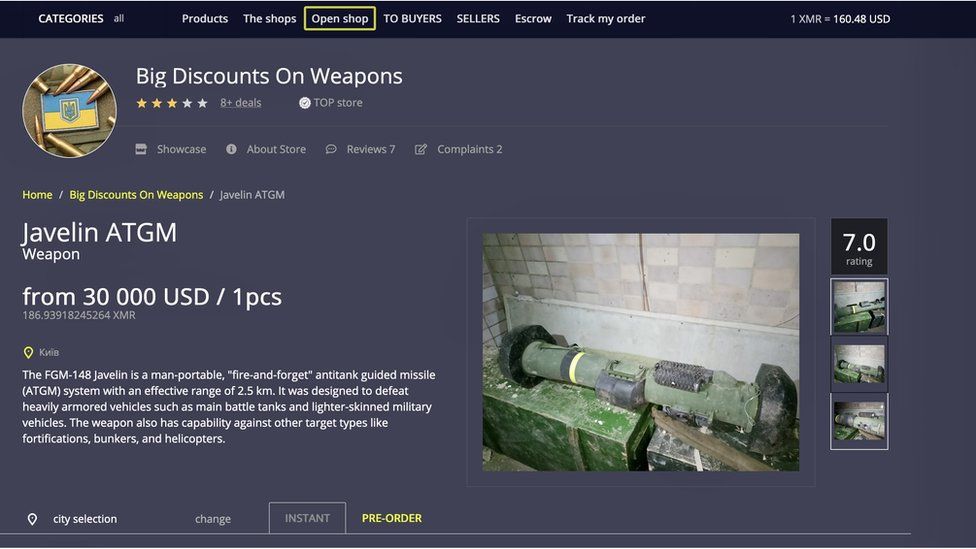
So, what happens to your data after a breach? It doesn't just disappear. It enters a sprawling, illicit online marketplace known as the dark web. Here, threat actors acquire data from breaches, including usernames, passwords, credit card details, or even personal IDs, and trade it like commodities.
The Data for Sale
The information harvested from a retail breach is particularly valuable because it's "fullz"—a complete package. A typical listing might include:
- Cardholder Name & Billing Address: For identity theft and creating fake accounts.
- Card Number, Expiration, and CVV: For making fraudulent online purchases.
- Email Address & Phone Number: For phishing campaigns and account takeover attempts.
- Purchase History: To craft highly targeted, believable scams (e.g., "We see you recently bought a leather handbag; here's a special offer on matching wallets").
The 2.9 billion personal records claimed in a recent mega-breach represent a scale so vast it's almost incomprehensible. This data is often sold in bulk for a few thousand dollars, then used by smaller criminals to commit individual fraud. The banking passwords belonging to 31,000 Australian customers stolen via malware and traded is a smaller-scale but equally damaging example of this pipeline.
The "Most of the data are leaked" Problem
A pervasive issue is that once data is on the dark web, it's nearly impossible to retrieve. It gets copied, repackaged, and sold repeatedly across different forums. Your personal data could be on the dark web right now, accessible to anyone willing to pay. This creates a permanent, low-level risk. Even if you cancel a compromised card, your name, address, and email remain valuable for other forms of fraud.
Is Your Email Compromised? The Free Check That Could Save You
Given the relentless pace of breaches, the first crucial step is discovery. Have you ever wondered how much of your personal information is available online? Here's your chance to find out. You don't need to be a tech expert.
Norton's data breach checker is a prominent, user-friendly tool that allows you to check if your email is compromised for free. By simply entering your email address, it scans multiple breach databases and tells you if your account appears in any known public data dumps. This is not a speculative scan; it's a query against documented breach collections.
How to Use a Breach Checker Effectively
- Use a Trusted Service: Stick to reputable cybersecurity companies (Norton, Have I Been Pwned, etc.).
- Check All Emails: Don't just check your primary email. Check old, unused accounts, as they are often less monitored and perfect for undetected fraud.
- Interpret the Results: If your email is found, the service will often list which breach(es) it appeared in (e.g., "TJX Companies 2007," "Adobe 2013"). This tells you what type of data might be out there.
- Don't Panic, Act: A hit means your email is in a hacker's hands, not necessarily that you're a current victim. It's a warning to secure your accounts and safeguard against future data breaches.
Our updated list for 2025 ranks the 83 biggest data breaches of all time, ranked by impact. Consulting such a list provides perspective. You'll see that retail, financial services, and social media are consistently top targets. Learn from their mistakes to avoid costly damages. The TJX breach is a case study in delayed detection and the cascading financial impact.
The Immediate Aftermath: What to Do If Your Information is Found on the Dark Web
Finding your email in a breach is a moment for decisive action, not despair. Learn what to do if your information is found on the dark web, like how to secure your accounts and safeguard against future data breaches. Here is your step-by-step protocol.
1. Change Passwords Immediately and Uniquely
- For the Compromised Email: Change the password to a strong, unique password you've never used anywhere else. Enable two-factor authentication (2FA)—this is non-negotiable.
- For All Critical Accounts: Banking, primary email, social media, and any account sharing a password with the compromised email must get new, unique passwords. Use a password manager to generate and store them.
2. Scrutinize Financial Statements and Credit Reports
- Monitor Daily: Check bank and credit card statements daily for any unauthorized transactions. Report fraud instantly.
- Get Free Credit Reports: In the U.S., use AnnualCreditReport.com to get reports from all three bureaus. Look for unfamiliar accounts or inquiries.
- Consider a Fraud Alert or Credit Freeze: A fraud alert makes creditors verify your identity before opening new accounts. A credit freeze locks your credit file entirely, preventing new account creation. Both are free.
3. Beware of the Phishing Tsunami
Your email address is now a target for highly targeted phishing. Expect emails or texts (smishing) that seem legitimate:
- "Your T.J.Maxx order is delayed..." (using your real name and a recent store).
- "Unusual login attempt on your account..." (using a service you use).
- Never click links or open attachments in unsolicited messages. Go directly to the website by typing the URL yourself.
4. Contact the Breached Entity (If Applicable)
If the breach is recent and from a specific company like T.J.Maxx, they should offer free credit monitoring or identity theft protection for affected individuals. Sign up. Also, report the breach to the Federal Trade Commission (FTC) at IdentityTheft.gov.
5. Secure Your Digital Footprint
- Review App Permissions: On social media and Google accounts, revoke access to apps you don't recognize or use.
- Update Security Questions: Use fake answers stored in your password manager for questions like "mother's maiden name."
- Check for Data Broker Listings: Services like DeleteMe or Kanary can help remove your personal data from data broker sites that aggregate and sell it.
The Path Forward: Shopping Smarter in a Breached World
You shouldn't have to abandon the thrill of the hunt for deals. Whatever your reason for shopping at t.j.maxx for women’s clothing, you’ll find all the best brands at even better prices. But you must shop with your eyes wide open.
Proactive Habits for the Modern Shopper
- Use a Dedicated Credit Card: Use a single credit card with a low limit for all online shopping. This isolates risk. Never use a debit card, as it provides direct access to your cash.
- Virtual Card Numbers: Many banks and services (like Apple Pay, Google Pay, Privacy.com) offer virtual, disposable card numbers for online purchases. The number is tied to your real account but can be turned off after one use.
- Minimize Account Creation: Only create an account if absolutely necessary (for order tracking, large purchases). Use guest checkout whenever possible.
- Review Privacy Settings: Regularly check the privacy settings on any retail accounts you hold. Limit data sharing for marketing.
- Stay Informed:Check if you’ve been exposed in a breach periodically, not just once. New breaches happen constantly.
The Role of Retailers and Your Rights
Retailers have a legal and ethical obligation to protect your data. All clearance free returns in store and other customer-friendly policies should extend to data security. They must:
- Employ robust, up-to-date encryption.
- Regularly audit and test their systems.
- Have a clear, prompt breach notification protocol.
- Offer meaningful support to affected customers.
As a consumer, you have rights under laws like state breach notification statutes and the GDPR (for EU citizens). Hold companies accountable.
Conclusion: Knowledge is Your Best Defense
The narrative of TJ Maxx Payment LEAK EXPOSED is more than a headline; it's a case study in the modern digital landscape. It illustrates the uncomfortable truth that the data we freely exchange for convenience and savings is a permanent asset in a shadowy global economy. The incredible savings on women's fashion and the wide range of fashionable clothing, accessories, and more for every style and occasion come with an invisible price tag: your personal security.
The history of breaches at major retailers, the mountains of data on the dark web, and the recent mega-breaches stealing billions of records are not isolated incidents. They are symptoms of a systemic vulnerability. Your personal data could be on the dark web right now. But you are not powerless.
Your power lies in vigilance and action. Use free checkers to discover if your email has been hacked. Implement strong, unique passwords and two-factor authentication. Monitor your financial life obsessively. Adopt shopping habits that minimize data exposure, like using virtual cards and guest checkout. Learn from the mistakes of breached companies to avoid becoming a victim.
Shopping at T.J.Maxx or any retailer should be about maximizing your style and your budget, not maximizing your risk. By understanding the data trail you leave, knowing how to check for compromises, and taking swift, decisive action if exposed, you reclaim control. You can still stock up on sports bras, yoga pants, and leggings in activewear and enjoy those amazing deals—but now you do so with the armor of knowledge and a proactive security strategy. In the battle for your personal data, the most effective weapon is an informed, alert, and prepared mind. Start your defense today.