Yandex Xnxx Leak: Explicit Content Exposed In Massive Data Breach?
Could your private online activity, your most sensitive searches, be exposed to the world? In late January 2023, a digital bombshell dropped on the cybersecurity world that made this terrifying question feel urgently real. A former employee of Yandex, Russia's largest technology company and a global search giant, leaked nearly 45 gigabytes of the company's proprietary source code on the notorious hacking forum BreachForums. While the initial reports focused on the theft of intellectual property, the true magnitude and chilling implications of this breach extend far beyond stolen algorithms. This incident serves as a stark gateway into a much larger, more pervasive crisis of global data security, where the very systems designed to index our digital lives can become vectors for exposing our deepest secrets, including the potential for non-consensual explicit content. This article dives deep into the Yandex leak, its connections to broader data breach epidemics, and, most importantly, what you can do to protect yourself.
The Yandex Source Code Heist: What Happened?
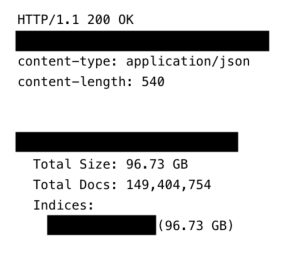
The breach, first reported in late January 2023, was not a hack in the traditional sense of external attackers breaching a firewall. Instead, it was an insider threat—a disgruntled or financially motivated former employee with legitimate access. This individual exfiltrated a staggering 45 GB of Yandex's core source code and dumped it on BreachForums, a marketplace for stolen data and cybercrime services. The leak included code for critical Yandex services like Yandex Search, Yandex Maps, Yandex Mail, and the Yandex AI assistant Alice.
What Does Stolen Source Code Really Mean?
Source code is the blueprint of a software application. For a company like Yandex, which processes billions of searches and handles vast amounts of user data, this code reveals:
- Traxxas Slash Body Sex Tape Found The Truth Will Blow Your Mind
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
- Exclusive Princess Nikki Xxxs Sex Tape Leaked You Wont Believe Whats Inside
- Proprietary algorithms: The secret sauce behind how Yandex ranks websites, personalizes results, and powers its AI.
- Internal infrastructure: How data flows between servers, databases, and user-facing apps.
- Potential security weaknesses: Code can contain hidden backdoors, hardcoded passwords, or architectural flaws that provide a roadmap for future, more devastating attacks.
- Data handling practices: How user queries, location data, and personal information are collected, processed, and stored.
While the initial leak did not contain direct user databases or personal information (a point emphasized in several key sentences), the exposed code could allow attackers to reverse-engineer vulnerabilities. This means hackers could study the code to find new ways to infiltrate Yandex's systems and potentially access the search analytics and ranking data the company collects on virtually every website and user. This is the critical link to the fear of exposed personal activity.
The Chilling Connection: Search Data as a Proxy for Private Life
Yandex has access to a broad international reach of data, and it has been evasive about what it can do with that data. This evasiveness is a common theme among tech giants. Search queries are arguably one of the most intimate data sources available. People search for health information, financial advice, relationship guidance, and yes, explicit content. A leak of how this data is aggregated and analyzed—even without the raw queries themselves—can be devastating.
Imagine the source code revealing a specific API endpoint used to fetch user search history for "personalized advertising." Attackers could then target that endpoint, potentially accessing the underlying databases. The massive data breach that exposed the search analytics and ranking data they collect on websites becomes a real possibility. This isn't just about losing anonymity; it's about the potential for blackmail, harassment, and the creation of non-consensual explicit deepfakes using information gleaned from private searches. The key sentence referencing "Yandex xnxx Leak" taps into this specific nightmare scenario—the exposure of adult content viewing habits, which can be weaponized for shame and extortion.
- Leaked Xxxl Luxury Shirt Catalog Whats Hidden Will Blow Your Mind
- Unseen Nudity In Maxxxine End Credits Full Leak Revealed
- Shocking Leak Nikki Sixxs Secret Quotes On Nude Encounters And Wild Sex Must Read
A Pattern of Global Negligence: Yandex is Not Alone
The Yandex leak is a single, high-profile thread in a vast, rotting tapestry of global data insecurity. To understand the risk, we must look at the ecosystem of breaches that have come before and continue to happen.
The Catalog of Catastrophes
The key sentences provide a grim roll call of major incidents:
- Massive Credential Leaks: In a single event, 184 million+ logins from top platforms were exposed. Another leak saw personal data for 700 million LinkedIn users—nearly 93% of the company’s members—put up for sale online.
- The Deepfake Epidemic: This massive leak is the latest case of people using generative AI tools to turn innocent photos into nonconsensual explicit deepfakes. The availability of personal photos from breaches fuels this abusive technology.
- Facebook's Repeated Failures: The social giant's history is marred by breaches. The Cambridge Analytica scandal saw 50 million Facebook profiles harvested for political profiling. Shockingly, Facebook decided not to notify over 530 million users whose data was lifted in a pre-2019 breach.
- Unprecedented Scale: A staggering almost 2.7 billion records of personal information for people in the United States were leaked on a hacking forum, including names, social security numbers, and addresses. A separate breach exposed 1,279,437 records from law enforcement agencies.
- Corporate and Healthcare Negligence:Retail giant Target paid an $18.5 million multistate settlement for its 2013 breach. More recently, UnitedHealth’s massive healthcare data breach exposed 100 million Americans’ personal info, including sensitive medical data.
These are not isolated "hacks." They are symptoms of a systemic failure where companies amass unprecedented amounts of data with insufficient security and, in many cases, a culture of hiding breaches from the public.
Legal and Global Ramifications: Who is Accountable?
The global and legal ramifications of these breaches are profound and still evolving. The Yandex leak may violate privacy laws like the GDPR, which requires explicit user consent for data collection and processing. As a company with users in Europe, Yandex is subject to GDPR. The leak of source code that details data processing mechanisms could be seen as a failure of the "security by design" principle mandated by the regulation.
However, enforcement is patchy. The Facebook case demonstrates how companies can sometimes avoid immediate notification requirements, depending on jurisdiction and the nature of the exposed data. The Target settlement, while large, is a fraction of the company's value and does little for the 41 million affected individuals. The legal system struggles to keep pace with the scale of digital harm, often treating data breaches as a cost of doing business rather than a fundamental violation of privacy rights. This creates a permissive environment where breaches become inevitable.
The Aftermath: How to Protect Yourself in a Breached World
Given that Have I Been Pwned allows you to check whether your email address has been exposed in a data breach, the first step is awareness. But what do you do next? Learn how to protect your accounts and stay safe after a major leak.
Actionable Steps for Immediate Defense
- Search Your Email: Go to HaveIBeenPwned.com (or similar reputable services) and enter every email address you use. This tells you which breaches your account appeared in.
- Change Passwords Immediately: For any account listed in a breach, change the password to a unique, strong password you have never used before. Do not just change it on the breached site; change it everywhere if you reused it.
- Enable Two-Factor Authentication (2FA): This is your single most important defense. Use an authenticator app (like Google Authenticator or Authy) or a hardware security key. SMS-based 2FA is better than nothing but can be intercepted.
- Use a Password Manager: Tools like Bitwarden, 1Password, or Dashlane generate and store complex, unique passwords for every site. You only need to remember one master password.
- Monitor for Suspicious Activity: Regularly check your accounts (email, banking, social media) for unrecognized logins, password change emails, or new devices. Set up login alerts where possible.
- Assume You're a Target: With breaches like the 2.7 billion US record leak, assume your personal information (name, address, SSN) is already on the dark web. Be extra vigilant for phishing emails and phone scams attempting to use this data.
- Consider a Credit Freeze: In the U.S., you can freeze your credit with the three major bureaus (Equifax, Experian, TransUnion) for free. This prevents new accounts from being opened in your name without your explicit PIN.
Long-Term Vigilance
- Review App Permissions: Regularly audit what third-party apps have access to your social media and Google/Facebook accounts. Revoke anything unnecessary.
- Minimize Data Sharing: Provide only the minimum personal information required for services. Use alternative email addresses for sign-ups.
- Stay Informed: Follow reputable cybersecurity news sources. Breaches are often disclosed months or years after they occur.
Conclusion: The Inevitability of Exposure and The Power of Preparedness
The Yandex source code leak is a watershed moment. It wasn't just about stolen code; it was a stark reminder that the search analytics and ranking data held by tech giants represent a profound privacy vulnerability. Coupled with the relentless parade of other breaches—from LinkedIn's 700 million to UnitedHealth's 100 million—a clear picture emerges: your personal information is almost certainly already exposed.
The legal system reacts slowly, and corporate accountability often feels like a distant concept. Therefore, the burden of protection falls increasingly on the individual. Search your email on HaveIBeenPwned. Understand that your data is a commodity traded in shadowy forums. The goal is no longer to be "unhackable"—that's impossible—but to be resilient. By implementing strong, unique passwords, mandatory two-factor authentication, and vigilant monitoring, you build digital moats around your most critical accounts. You make yourself a difficult, unrewarding target in a landscape where attackers seek low-hanging fruit.
The "Yandex xnxx Leak" scenario, while specific, symbolizes a universal truth: in the digital age, privacy is not a default state. It is a continuous practice of defense. Start your practice today. Check your exposures, secure your accounts, and take back control. Your future self will thank you when the next inevitable breach makes headlines.