The Secret Sex Tape Scandal Involving Amber Lynn XXX Exposed!
What happens when a private moment, captured in the heat of passion, becomes a permanent, public spectacle? For many, the mere thought is a nightmare. Yet, for celebrities like former adult film icon Amber Lynn, this isn't just hypothetical—it's a stark reality that has played out in the unforgiving court of public opinion. The alleged leak of a private sex tape is more than just salacious gossip; it's a profound breach of digital privacy that exposes the vulnerabilities we all face in an era where our most intimate secrets are stored as ones and zeros. This scandal serves as a chilling case study, forcing us to confront a critical question: How secure are the digital secrets we entrust to our devices and apps every single day?
From the App Secret that protects your mini-program to the seed key for your two-factor authentication, we navigate a complex web of digital keys and passwords. We use Incognito Mode to browse without a trace and enable Developer Options to unlock our phone's full potential. But do we truly understand what these "secrets" are, how to manage them, and the catastrophic consequences if they fall into the wrong hands? This article dives deep into the anatomy of digital secrecy, using the fragmented clues from technical guides to personal confessions to build a comprehensive guide on protecting your private life online. We'll move from the scandal that made headlines to the practical steps you can take today to ensure your secrets remain just that—yours.
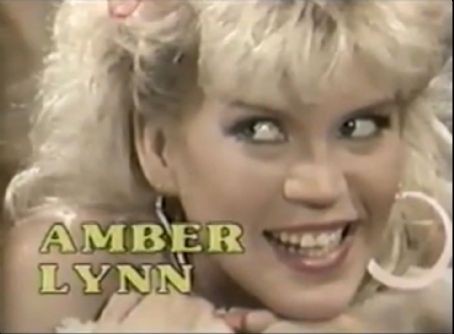
Amber Lynn: A Brief Biography
Before dissecting the digital mechanisms of scandal, it's crucial to understand the person at the center of this storm. Amber Lynn, born Amber Lynn Johnson on September 3, 1964, is a retired American pornographic actress and radio host who rose to prominence during the "Golden Age of Porn" in the 1980s and 1990s. Her career, spanning over a decade, made her one of the most recognizable figures in the industry, earning her a place in the AVN and XRCO Halls of Fame. Post-retirement, she successfully transitioned into mainstream media, hosting radio shows and advocating for sex workers' rights.
- Exclusive The Hidden Truth About Dani Jensens Xxx Leak Must See Now
- Kerry Gaa Nude Leak The Shocking Truth Exposed
- Shocking Tim Team Xxx Sex Tape Leaked The Full Story Inside
The alleged "secret sex tape" scandal refers to the non-consensual distribution of private, intimate footage involving her, a scenario tragically common in the age of smartphones and cloud storage. Such leaks are not merely violations of privacy but often constitute revenge porn, a crime with devastating personal and professional repercussions. Her experience underscores a universal truth: no one is immune to the risks of digital exposure.
| Attribute | Details |
|---|---|
| Full Name | Amber Lynn Johnson |
| Professional Name | Amber Lynn |
| Date of Birth | September 3, 1964 |
| Primary Career | Adult Film Actress (1980s-1990s) |
| Post-Retirement | Radio Host, Advocate |
| Hall of Fame | AVN Hall of Fame, XRCO Hall of Fame |
| Scandal Context | Subject of alleged non-consensual tape leaks, highlighting digital privacy risks for all. |
The Digital Secrets We Keep: From App Secrets to Seed Keys
Our digital lives are built on a foundation of secrets. These aren't just passwords; they are cryptographic keys, tokens, and configuration data that act as the ultimate gatekeepers to our online identities, finances, and private communications. Understanding these different types of "secrets" is the first step toward mastering digital security.
- Application Secrets (App Secrets): These are confidential strings, like the App Secret for a WeChat mini-program, that authenticate an application to a service's backend. They prove the app is who it claims to be. If compromised, a malicious actor can impersonate your app, access user data, or manipulate its functions.
- OAuth Client Secrets: Used in protocols like OAuth 2.0, these secrets authenticate an application when it requests access to a user's data on another service (e.g., "Sign in with Google"). The process of client secret rotation—adding a new secret, migrating to it while the old one works, then disabling the old one—is a critical security best practice to limit exposure if a secret is leaked.
- Browsing Data & History: What you do in Incognito Mode (or Chrome's Secret Mode) is designed to leave minimal traces on your device. As the system messages state, this mode "limits the information saved on your device." However, it's a common misconception that this makes you invisible to your internet provider, employer, or the websites you visit. It simply means local history, cookies, and form data aren't stored after the session.
- Two-Factor Authentication (2FA) Seeds: The secret key or seed for an app like Google Authenticator is the foundational code from which all your time-based one-time passwords (TOTPs) are generated. I didn't realize I should have written down the secret key (seed) in case something happens to my phone. This confession is a monumental security oversight. If you lose or reset your phone without backing up this seed, you are permanently locked out of every account protected by that 2FA method. This seed is arguably the most important secret for account recovery.
Case Study: Managing Your WeChat Mini-Program App Secret
The first key sentence provides a technical walkthrough: "1. Enter the WeChat public platform to log in to the mini-program 2. Enter the mini-program homepage 3. Click 'Development' 4. Click 'Development Settings' 5. Click 'Generate' next to the 'App Secret' item 6. Scan and verify with the administrator's phone to view your mini-program App Secret."
- Shocking Truth Xnxxs Most Viral Video Exposes Pakistans Secret Sex Ring
- Taylor Hilton Xxx Leak Shocking Video Exposed
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
This process highlights a fundamental security tension: accessibility versus protection. The App Secret is the master key to your mini-program's backend. The requirement for administrator phone verification is a strong form of two-factor authentication, ensuring that only a verified human with physical access to a trusted device can reveal this critical credential. This is a good practice. However, the act of generating and viewing the secret is a moment of high vulnerability.
Practical Implications:
- Never Share This Secret: It should be treated like the root password to your server. Do not email it, store it in plain text on a shared drive, or hardcode it in client-side code (like a web frontend).
- Use Environment Variables: In your server-side code, store the App Secret in secure environment variables or a dedicated secrets management service (like AWS Secrets Manager, HashiCorp Vault).
- Rotate Regularly: If you suspect any compromise, follow the same steps to generate a new App Secret. You must then update this new secret in all your server configurations. The old secret will typically remain valid for a transition period, allowing for a seamless switch.
- Audit Access: Only a minimal number of trusted developers or systems should ever have access to view or manage this secret. The verification step is your audit trail.
OAuth Client Secret Rotation: A Proactive Security Stance
The second sentence introduces a powerful security concept: "With the client secret rotation feature, you can add a new secret to your oauth client configuration, migrate to the new secret while the old secret is still usable, and disable the old secret afterwards."
This is not just a technical feature; it's a security protocol. Think of it like changing the locks on your house. You get a new key made (add a new secret), give it to everyone who needs access (migrate your applications/servers to use the new secret), and only once everyone is in with the new key do you render the old key useless (disable the old secret). The period of overlap is crucial to prevent service outages.
Why is this vital?
- Breach Containment: If an old secret is accidentally exposed in a code repository or log file, you can be confident it will soon be useless.
- Regular Hygiene: Mandating periodic secret rotation (e.g., every 90 days) is a cornerstone of a robust security policy, reducing the "window of opportunity" for an attacker.
- Incident Response: If you know a specific secret was compromised, you can immediately initiate rotation, knowing your services will stay online.
Actionable Tip: Audit all your OAuth clients (Google, Facebook, GitHub, etc.) and any API keys. Identify which services support secret rotation and implement a schedule. For those that don't, treat those secrets with extreme caution and plan for migration to services that do.
Private Browsing: Understanding the Limits of "Secret Mode"
Sentences three and four, in Korean and Japanese, describe Incognito/Secret Mode in Chrome. The core message is consistent: "Secret mode allows you to browse the web privately. Secret mode limits the information saved on your device." This is accurate but often misunderstood.
What Incognito Mode DOES:
- Prevents browsing history, search history, cookies, site data, and form entries from being saved on your local device.
- Creates a temporary session separate from your main browser session, so you're logged out of most sites.
- Is useful for signing into multiple accounts on the same site, testing logged-out views of your website, or avoiding targeted ads based on that session's activity on your device.
What Incognito Mode DOES NOT Do:
- Make you anonymous to your ISP or employer. They can still see your traffic.
- Hide your activity from the websites you visit. They know you visited.
- Protect you from malware or phishing.
- Prevent fingerprinting. Advanced tracking techniques can often still identify you.
The scandal of a leaked sex tape often begins with a moment of perceived privacy—perhaps recording on a personal phone or using a "private" browser window. The lesson is clear: true digital privacy requires more than just a browser setting; it requires encrypting files, using secure communication channels, and understanding the full data path of your actions.
Unlocking Power: Android Developer Options
Sentence five is a call to action: "learn how to enable developer options on android and pixel devices to access advanced features and settings for enhanced functionality." Enabling Developer Options (by tapping the Build Number in Settings > About Phone 7 times) is like unlocking the hood of your car. It's powerful but comes with risks.
Useful Features for Privacy & Security:
- USB Debugging: Essential for app development, but a major security hole if left on. Always disable it when not in use.
- Stay Awake: Keeps the screen on while charging, useful for monitoring.
- Background Process Limit: Can be used to aggressively stop apps from running in the background, reducing tracking.
- Mock Locations: For developers testing location-based apps.
- Show Touches/Pointer Location: Visual feedback for UI testing.
The Dark Side: These options can also be used to sideload malicious apps, extract data, or bypass security restrictions if your phone is physically accessed by an adversary. The scandal of a private tape could involve a device that was left unlocked and with Developer Options enabled, allowing for data extraction tools to be used.
Rule: Enable Developer Options only if you need them for a specific, short-term task. Once done, disable them. Never enable USB Debugging on a device you use for daily personal activities.
The Google Authenticator Seed: Your Unforgotten Secret
Sentences ten and eleven form a critical personal anecdote: "I've downloaded the google authenticator app on my phone a long time ago. I didnt realize i should have written down the secret key (seed) in case something happens to my phone."
This is one of the most common and costly mistakes in personal digital security. The seed (often presented as a QR code and a 16-32 character alphanumeric string during setup) is the master secret. Your phone uses this seed and the current time to generate the 6-digit codes. The seed is NOT stored on Google's servers. If you lose your phone and have no backup of this seed, you are locked out forever.
The Correct Setup Process:
- When setting up 2FA for an account (Google, GitHub, etc.), the service provides a QR code and the alphanumeric seed.
- BEFORE scanning the QR code, write down the alphanumeric seed on paper and store it in a secure, offline location (like a safe or safety deposit box).
- Scan the QR code with your Google Authenticator app.
- Verify the setup with a code from the app.
- Store recovery codes for the service separately.
What to Do If You Didn't Write It Down:
- If you still have the old phone with the app installed, some apps (like Authy) have cloud backup features. Google Authenticator did not originally have this, but newer versions offer encrypted backup to your Google Account. Ensure this is turned ON if you use it.
- If the phone is gone and no backup exists, you must use the account recovery processes for each service (which often involve alternate emails, phone numbers, or security questions). This can be a lengthy and uncertain process.
The Grammar of Secrecy: Prepositions and Perception
Sentences six, seven, and eight pose a linguistic question: "Dear all, i just found this two different sentences. What preposition should i put after the word secret? For instance, what sentence is correct."
While seemingly trivial, the preposition we use shapes our mental model of a secret.
- Secret to: Implies exclusivity and access. "The secret to the formula" means the formula is accessible only to those who know the secret. It's about a key.
- Secret of: Implies ownership and essence. "The secret of her success" suggests the success itself contains an intrinsic, knowable quality. It's about the core.
In the context of digital security:
- The App Secret is to your mini-program. It is the key that grants access.
- The seed is the secret of your 2FA. It is the core component from which your codes are derived.
This nuance matters. We must think of our digital credentials not as vague "secrets" but as keys (secret to)—specific, functional, and high-value items that must be guarded with the same care as a physical key to a vault. The scandal of a leaked tape is the ultimate violation of a secret of someone's private life, made possible by failing to protect the digital keys to their private data.
When Secrets Leak: Real-World Consequences of Digital Exposure
The Help Center snippet (sentence 9) mentions policies and privacy, which are the last lines of defense. When digital secrets are exposed, these policies determine your recourse, but the damage is often already done. The consequences of a leak—be it an App Secret, a browsing history, or a personal video—are severe and multi-faceted:
- Financial Loss: Compromised App Secrets or OAuth tokens can lead to fraudulent transactions, API abuse leading to massive cloud bills, or theft of cryptocurrency.
- Identity Theft & Account Takeover: Leaked credentials or 2FA seeds give attackers the keys to your entire digital identity—email, social media, banking.
- Reputational Ruin: This is the core of the Amber Lynn scandal scenario. A private video, intended for one person, becomes public, leading to shame, harassment, professional blacklisting, and profound personal trauma.
- Legal Liability: If leaked data includes customer information (PII), you could face lawsuits and regulatory fines under GDPR, CCPA, etc.
- Permanent Record: Unlike a physical document that can be destroyed, a digital leak can be copied, archived, and resurfaced indefinitely across the dark web and archive sites.
Statistics from cybersecurity firms consistently show that human error—like failing to rotate secrets, misconfiguring cloud storage, or losing a 2FA seed—is the leading cause of data breaches. The scandal isn't always a sophisticated hack; it's often a simple, devastating mistake.
Proactive Measures: Building Your Digital Fortress
So, how do you protect your secrets? Move beyond Incognito Mode and into a proactive security mindset.
- Inventory Your Secrets: List every critical digital key: App Secrets, API keys, OAuth client secrets, 2FA seeds, database passwords, SSH keys.
- Use a Password Manager: For secrets that are passwords, use a reputable manager (Bitwarden, 1Password). For non-password secrets (like long API keys), many managers allow secure notes.
- Enable 2FA Everywhere, and BACK UP THE SEED: Use an authenticator app (Google Authenticator, Authy, Aegis) and write down the initial seed for each account. Store these backups securely and offline.
- Rotate Critical Secrets: Implement a calendar reminder to rotate your most important application and OAuth secrets every 3-6 months.
- Audit Your App Permissions: Regularly review which third-party apps have access to your Google, Facebook, and other accounts (via "Apps & Websites" settings). Revoke any you don't recognize or use.
- Encrypt Your Devices: Use full-disk encryption on your phone and computer. This is your last line of defense if a device is lost or stolen.
- Think Before You Record: The most effective way to prevent a sex tape scandal is to never create one. If you do, store it only on an encrypted, password-protected device, never in cloud sync folders, and have explicit, documented consent from all parties involved.
- Understand the Tools: Know what Incognito Mode does and doesn't do. Know what Developer Options enable. Knowledge is your primary defense.
Conclusion: Your Secrets Are Your Responsibility
The fragmented clues—from the step-by-step guide to generating an App Secret, to the philosophical query about prepositions, to the panicked realization about a lost Authenticator seed—all paint a single, unifying picture: in the digital world, you are the sole guardian of your own privacy. The scandal involving Amber Lynn is a public spectacle, but the principles are universal. The "secret sex tape" is merely the payload; the vulnerability is the compromised key, the misconfigured setting, or the unencrypted file.
The client secret rotation feature exists because secrets will leak. Incognito Mode exists because we desire private moments. Developer Options exist because we need control, but that power demands responsibility. The Google Authenticator seed is the ultimate test: did you prepare for the loss of your device?
Don't wait for a scandal to force you to confront your digital vulnerabilities. Start today. Inventory one secret. Rotate one key. Write down one seed. Secure one device. The exposed secret is no longer a secret at all; it's a liability. Your privacy is not a default setting—it is a meticulously maintained fortress, built one conscious decision at a time. Build it now, before the moment you need it most has already passed.