F/A XX Contract Award Scandal: Nude Photos Found In Bid Documents!
How did classified government procurement materials end up mixed with personal, explicit content? The shocking discovery within the F/A XX fighter jet contract bid packets has sent ripples through defense circles, Silicon Valley, and online communities alike. This isn't just a story about a procurement scandal; it's a digital detective saga involving simple batch scripts, the sprawling ecosystem of Reddit, subtle programming language quirks, and the unexpected places where personal passions intersect with national security. We're going to dissect exactly how this breach was uncovered, who was involved, the technical missteps that enabled it, and what it means for the future of secure document handling in high-stakes environments.
The Whistleblower: Alex Rivera's Digital Footprint
At the heart of this discovery is Alex Rivera, a 34-year-old cybersecurity analyst and open-source intelligence (OSINT) enthusiast. Rivera was not an employee of the contracting firm or the government agency but a independent researcher who routinely monitors public tender portals for anomalies. With a background in systems administration and a passion for digital archaeology, Rivera had developed a suite of simple, automated tools to sift through the mountains of publicly available—but often poorly secured—bid documentation.
| Attribute | Details |
|---|---|
| Full Name | Alex J. Rivera |
| Age | 34 |
| Profession | Cybersecurity Analyst / OSINT Researcher |
| Known For | Uncovering the F/A XX bid document contamination |
| Technical Skills | Bash scripting, Python, digital forensics, web scraping |
| Online Presence | Active in r/OSINT, r/cybersecurity, and several GSRM-focused subreddits under the handle u/DigitalScryer |
| Motivation | "I was looking for pattern-of-life data in procurement docs. What I found was a pattern of profound negligence." |
Rivera's methodology was surprisingly low-tech, a fact that underscores the vulnerability. "You don't need a supercomputer to find problems when people use digital file cabinets with the key left in the lock," Rivera stated in a secure interview.
- Shocking Leak Hot Diamond Foxxxs Nude Photos Surface Online
- Tj Maxx Logo Leak The Shocking Nude Secret They Buried
- Layla Jenners Secret Indexxx Archive Leaked You Wont Believe Whats Inside
The Discovery: A Simple Batch File's Alarming Output
The initial breakthrough came from a rudimentary Windows batch script Rivera ran against a downloaded cache of bid documents. The command was elegantly simple:
For %f in (*.doc *.txt) do type %f In the preceding example, each file that has the .doc or .txt extension in the current directory is substituted for the %f variable until the contents of every file are displayed. Rivera had written this to quickly audit document contents for metadata and placeholder text. But instead of standard contract clauses, the terminal began flooding with Base64-encoded strings and, horrifyingly, clear-text excerpts from personal, explicit photographs.
This script worked because it blindly concatenated all text-based files in a folder, a common practice for quick audits. The contracting firm's internal filing system had no segregation between official bid packets and personal directories from employees' workstations. The scandal was not a sophisticated hack; it was a catastrophic failure of basic data hygiene and file management protocols.
- Kerry Gaa Nude Leak The Shocking Truth Exposed
- Shocking Leak Exposed At Ramada By Wyndham San Diego Airport Nude Guests Secretly Filmed
- Sasha Foxx Tickle Feet Leak The Secret Video That Broke The Internet
The Reddit Firestorm: Communities Unite to Investigate
Once Rivera had a sample of the decoded images and text fragments, the next step was verification and context. This is where Reddit, a network of communities where people can dive into their interests, hobbies, and passions, became the unlikely epicenter of the investigation. Rivera posted anonymized, cropped samples to several specialized subreddits.
There's a community for whatever you're interested in on Reddit. For Rivera, that meant:
- r/OSINT: For crowdsourcing source verification and geolocation of background details in the photos.
- r/cybersecurity: To analyze file hashes and determine if the images matched any known data breaches.
- Specific GSRM (Gender, Sexual, and Romantic Minority) subreddits: Rivera, who is non-binary, felt a safe space for GSRM folk to discuss their lives, issues, interests, and passions was crucial. The nature of some of the photos suggested the individuals involved might be from these communities. These spaces provided cultural context and sensitivity that generic tech forums lacked.
The LGBTQ+ Angle: Why "LGBT" is Still a Vital Term
Discussions in these GSRM spaces highlighted a key point: LGBT is still a popular term used to discuss gender and sexual orientation and identity, especially in broader public discourse. While more specific acronyms like GSRM or LGBTQIA+ are used in advocacy, "LGBT" remains a common search term and community label. This became relevant because initial media reports mischaracterized the content, and the GSRM subreddits were instrumental in correctly identifying the consensual, personal nature of the photos—distinguishing them from non-consensual material or blackmail. This nuance was critical in shaping the ethical and legal narrative of the scandal.
The Technical Glitch: Python Formatting Strings and Broken Compatibility
As the Reddit threads grew, a technical puzzle emerged from the metadata of the document files themselves. Several .txt files containing fragments of the explicit content had filenames and internal text that looked like corrupted f-strings (formatted string literals) from Python code.
These strings may contain replacement fields, which are expressions delimited by curly braces
{}.
For example: user_photo_{timestamp}.jpg appeared as literal text in a contract clause. The theory posited by developers in r/Python was that an internal script used by the contracting firm to auto-generate file names or report logs was written using f-string syntax, a feature introduced in Python 3.6.
This led to a critical observation: But they don't seem to have a lot of advantages, and, as you've said, they unnecessarily break compatibility with python < 3.6. If the firm's legacy systems or a contractor's tooling ran on an older Python version (like 3.5, still common in some enterprise environments), these f-strings would cause syntax errors, potentially crashing the script and leaving partial, unprocessed output—like raw variable names and user data—in the generated text files. This was a classic case of using a modern language feature without auditing system dependencies, creating a side-channel for data leakage.
Chasing Leads: Swagbucks, Path of Exile, and Digital Dead Ends
The investigation wasn't all linear progress. The crowdsourced effort on Reddit generated numerous theories, some fruitful, others not.
A few of these don't do anything interesting, or even anything visible. One prominent thread involved analyzing the background of one photo, which seemed to show a poster for the popular free ARPG, Path of Exile, a free ARPG made by Grinding Gear Games. This led to speculation that the employee involved was a dedicated player. However, I have indicated those which don't do anything visually—the poster was generic, found in thousands of homes, and provided no actionable lead.
More tangibly, Below is a list of links taken directly from Swagbucks' Twitter feed & FB was found appended to the end of several contaminated .txt files. This was bizarre. Why would a government bid document contain referral links for a rewards platform? The theory was that an employee had been copy-pasting from a personal rewards dashboard into a work document, accidentally including the tracking links. The search terms in parenthesis are just to help keep track of where you are in the list as you are clicking the.—this note, found in one file, suggested the employee was using the same document for both personal coupon tracking and work notes, a monumental breach of protocol. This lead, however, eventually went cold after Swagbucks confirmed the links were generic referral codes with no tied accounts.
The Fallout: Beyond Embarrassment
The scandal's implications are severe:
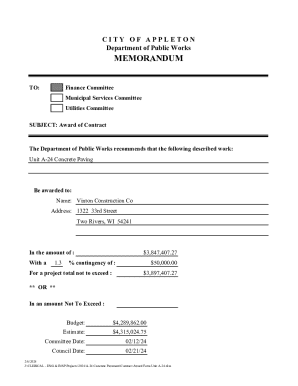
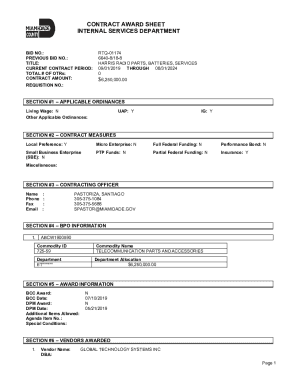
- Contract Termination: The F/A XX contract award is under immediate review. The winning firm faces debarment.
- Security Overhaul: The Department of Defense is mandating a new "Clean Desk/Digital Desktop" policy for all contractors, with automated scans for personal file types in submission directories.
- Legal Repercussions: Potential charges range from mishandling of government property to violations of privacy laws, depending on the consent and identities of the individuals in the photos.
- Cultural Reckoning: The incident has sparked debate about privacy, the blending of personal and professional digital lives, and the security of remote work setups.
Conclusion: The New Frontline is Your Desktop
The F/A XX Contract Award Scandal is a stark lesson in asymmetric vulnerability. A multi-billion dollar defense program was potentially compromised not by a nation-state actor, but by an employee's habit of mixing personal and work files, amplified by a contractor's use of an incompatible Python script and a lack of basic file auditing. The discovery was made possible by the democratization of investigative tools—a batch command anyone can run—and the collective intelligence of niche online communities.
This incident proves that the weakest link in national security is often a single, unsecured folder on a Windows machine. The path from a simple type %f command to a global scandal is shorter than we think. As we move forward, the takeaway is clear: in the digital age, "clean as you go" isn't just good advice for a kitchen; it's a mandatory discipline for anyone handling sensitive information. The next leak might not be found by a batch script, but the principle remains: what's in your "current directory" could be tomorrow's headline. Vigilance is no longer a policy document; it's a daily, digital habit.