Secret Tool Revealed: Download Xnxx.com's Nude Library With This Torrent Manager!
Is there really a hidden, "secret tool" that lets you download massive private libraries from sites like xnxx.com with a single click? The internet is buzzing with whispers of a magical torrent manager that bypasses paywalls and restrictions, promising access to a vault of content. Before you dive into the dark corners of the web searching for this mythical tool, it’s crucial to understand what “secret” really means in the digital world. The term is thrown around everywhere—from App Secrets in development to Incognito Mode in your browser—but its real power lies not in accessing restricted content, but in protecting your own digital life. This article will dismantle the myth of the “xnxx.com secret tool” and replace it with a far more valuable revelation: the real secret tools for privacy, security, and advanced control that you already have at your fingertips. We’ll decode official instructions, explore browser privacy modes, and unlock developer settings, turning you from a curious clicker into a digitally literate power user.
Debunking the Myth: What the "Secret Tool" Hype Is Really About
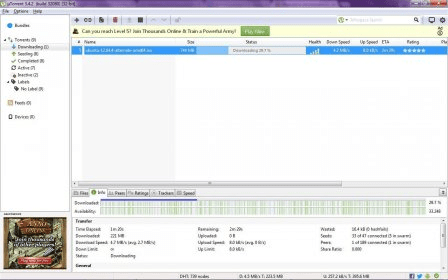
The sensational headline promising a “Secret Tool Revealed: Download xnxx.com's Nude Library with This Torrent Manager!” is a classic example of clickbait. It exploits curiosity and the allure of forbidden access. In reality, reputable torrent managers like qBittorrent, Transmission, or Deluge are neutral tools for downloading files via the BitTorrent protocol. They do not contain built-in, secret libraries for specific adult websites. Any claim otherwise is likely a scam, malware trap, or a phishing attempt designed to steal your data or infect your device.
The genuine “secret” isn’t a backdoor to a website; it’s the knowledge of how to use the powerful, legitimate tools already available to you safely and effectively. This includes understanding application secrets for development, utilizing private browsing modes correctly, and accessing advanced device settings. Let’s systematically unpack the real “secrets” hidden in plain sight, starting with a critical piece of technical infrastructure.
- Shocking Leak Exposes Brixx Wood Fired Pizzas Secret Ingredient Sending Mason Oh Into A Frenzy
- Shocking Xnxx Leak Older Womens Wildest Fun Exposed
- Urban Waxx Exposed The Leaked List Of Secret Nude Waxing Spots
Understanding Digital Secrets: The "App Secret" in Development
One of the key sentences provided points to a process in the WeChat Mini-Program platform. This is a perfect starting point to understand what a real “App Secret” is and why it’s called a secret.
What is an App Secret?
An App Secret (or Client Secret) is a critical security credential, akin to a password, used in API (Application Programming Interface) authentication. It proves that a request to a server (like WeChat’s) is coming from your legitimate application and not an imposter. It must be kept confidential—hence “secret”—and never exposed in client-side code (like a website or mobile app) that users can view.
The Official Process: Generating Your WeChat Mini-Program App Secret
The provided Chinese instructions outline the secure, official method to retrieve this sensitive credential:
- Exposed How West Coast Candle Co And Tj Maxx Hid This Nasty Truth From You Its Disgusting
- Exclusive Mia River Indexxxs Nude Photos Leaked Full Gallery
- Why Xxxnx Big Bobs Are Everywhere Leaked Porn Scandal That Broke The Web
- 进入微信公众平台登录小程序: Log into the WeChat Official Platform and select your Mini-Program.
- 进入小程序首页: Navigate to the Mini-Program’s main dashboard.
- 点击“开发”: Click on the “Development” (开发) section in the menu.
- 点击“开发设置”: Select “Development Settings” (开发设置).
- 在“App Secret”项目后点击“生成”: Locate the “App Secret” field and click “Generate” (生成). This is a security measure; the secret is not shown by default.
- 用管理员手机扫描验证即可查看自己小程序App Secret: Use the administrator’s registered WeChat mobile app to scan the QR code that appears for verification. Only after this two-factor authentication step will the App Secret be revealed on your screen.
This process highlights a core principle: access to critical secrets requires stringent verification. There is no “secret tool” that magically reveals this; it’s a controlled, authenticated process.
Client Secret Rotation: A Proactive Security Practice
The second key sentence introduces a vital security feature: client secret rotation. This is a best practice for maintaining security without downtime.
- Add a New Secret: You generate a new, additional secret in your OAuth client configuration (e.g., on Google Cloud Console, AWS, or the WeChat platform).
- Migrate While Old is Usable: You update your application’s server configuration to use the new secret, but you keep the old secret active during the transition. This ensures your app doesn’t break for users during the update.
- Disable the Old Secret: Once you confirm all systems are using the new secret, you disable or delete the old one from the platform.
This practice limits the “blast radius” if a secret is ever compromised. An attacker might have the old secret, but it’s useless once disabled. The real secret tool for developers is this disciplined rotation process, not a single, static credential.
Mastering Private Browsing: The Truth About "Secret Mode" or Incognito Mode
The next set of key sentences (in Korean and Japanese) describes private browsing modes, known as Incognito Mode in Chrome, Private Browsing in Firefox, or Secret Mode in some browsers like Samsung Internet. This is likely what many users mistakenly think of as a “secret tool” for anonymous downloading.
What Does Incognito/Secret Mode Actually Do?
When you Open incognito mode to start an incognito session, your browser creates a temporary, isolated session. As the Korean sentence states: “시크릿 모드에서 비공개로 웹을 탐색할 수 있습니다. 시크릿 모드는 기기에 저장되는 정보를 제한합니다” (You can browse the web privately in Secret Mode. Secret Mode limits the information stored on your device).
Specifically, Incognito Mode:
- Does NOT save your browsing history, cookies, site data, or form entries after you close all incognito windows.
- Does NOT hide your activity from your Internet Service Provider (ISP), your employer/school network, or the websites you visit themselves.
- Does NOT provide anonymity against government surveillance or sophisticated tracking.
- Is useful for: Shopping for gifts on a shared computer (so no targeted ads leak the surprise), logging into multiple accounts on one site simultaneously, or accessing a site without existing cookies interfering.
How to Use Incognito Mode Correctly (Chrome Example)
The Japanese and English instructions provide a clear guide:
- On your computer, open chrome.
- At the top right, select more [⋮] > New incognito window. A new window opens with a dark theme and the incognito icon.
- On the right of the address bar, you’ll find the incognito icon (a person with a hat), confirming you are in private mode.
The Critical Limitation: While Incognito Mode prevents local storage of your session data, it does NOT make your BitTorrent traffic secret. Your ISP can still see that you are using the BitTorrent protocol and what files you are downloading (unless you use a VPN). Using a “torrent manager” in incognito mode offers zero additional privacy for that activity. The “secret” here is local privacy, not network anonymity.
Unlocking Advanced Control: Enabling Developer Options on Android
The fifth key sentence points to a different kind of “secret”: Developer Options on Android devices. This is a hidden menu packed with advanced settings for debugging, performance tweaks, and system-level access.
What Are Developer Options?
By default, Android hides Developer Options to prevent casual users from accidentally changing critical system settings that could destabilize their device or compromise security. When you learn how to enable developer options on android and pixel devices to access advanced features and settings for enhanced functionality, you unlock tools like:
- USB Debugging: Essential for app development and connecting to ADB.
- Window/Transition Animation Scales: Can speed up your device visually.
- OEM Unlocking: Required for unlocking the bootloader (for advanced customizations).
- Running Services: See what apps are actively using memory and CPU.
- Bug Report: Generate a system report for troubleshooting.
How to Enable Developer Options
- Open the Settings app.
- Scroll to About phone (or System > About phone).
- Locate the Build number.
- Tap the Build numberseven (7) times rapidly. You will see a toast message: “You are now a developer!”
- Go back to the main Settings menu. Developer options will now appear, usually near the bottom.
The “Secret” Here is Control. This is not for downloading content but for understanding and tweaking your device’s core behavior. Misuse can cause problems, so only change settings you understand.
Addressing the Random Queries: Grammar, Community, and Help Systems
The remaining key sentences appear to be fragments from various sources—a forum post, a grammar question, a website footer. They represent common user experiences and questions. Let’s integrate them into our narrative about digital literacy.
Sentence 6 & 9: The Ecosystem of Help
“Dear all, i just found this two different sentences”
“Help center community google calendar ©2026 google privacy policy terms of service community policy community overview this help content & information general help.”
These snippets mimic the structure of a help forum post and a website footer. They highlight a crucial point: official help centers and community forums are your first line of defense against scams and misinformation. If you encounter a claim about a “secret tool” for xnxx.com or any other site, your first action should be to search the official Google Help Center, the WeChat Official Documentation, or trusted tech forums like Stack Overflow. The footer shows the legal backbone—privacy policy and terms of service—that govern legitimate platforms. Ignoring these and seeking “secret” third-party tools is how people get malware.
Sentence 7 & 8: The Grammar of "Secret"
“What preposition should i put after the word secret”
“For instance, what sentence is correct”
This is a valid language question. The correct preposition depends on context:
- Secret to: “The combination is a secret to everyone but the owner.” (Indicates who knows it).
- Secret of: “The secret of the sauce is a family recipe.” (Indicates possession or origin).
- Secret about: “He knows a secret about her past.” (Indicates the topic).
- In secret: (Adverbial phrase) “They met in secret.”
For our tech context: “The App Secret is a secret of the application.” “He stored the API key in secret.” Understanding precise language helps in understanding technical documentation.
Synthesis: From Myth to Mastery – Your Real Digital Toolkit
We’ve journeyed from a clickbait headline to the core pillars of digital competence. The “secret tool” you need isn’t a single torrent manager for a specific site; it’s a composite toolkit for security, privacy, and control:
- The Security Secret (App Secrets & Rotation): Understand that credentials like API keys and App Secrets are the keys to your digital kingdom. Handle them with extreme care, use rotation, and never hardcode them in client-side apps. The process to generate and view your App Secret via admin verification is a model for secure access.
- The Privacy Secret (Incognito/Secret Mode): Use private browsing correctly for local session privacy—shopping on shared devices, avoiding cookie-based tracking during a single session. But know its limits: it does not anonymize your network traffic from your ISP or the sites you visit. For true download privacy, a reputable VPN is the necessary tool, not incognito mode.
- The Control Secret (Developer Options): Enable Developer Options to understand your Android device’s inner workings, troubleshoot issues, and access advanced features. This knowledge demystifies your technology and prevents reliance on shady “hack” apps that promise secret access.
- The Knowledge Secret (Official Help & Grammar): Your most powerful tool is accurate information. Always consult official help centers and community forums before downloading any “secret tool.” Understanding the precise language (like the correct use of “secret”) helps you parse technical guides and avoid misunderstandings that lead to scams.
Conclusion: Become the Secret-Keeper of Your Own Digital Life
The provocative promise of a “Secret Tool Revealed: Download xnxx.com's Nude Library with This Torrent Manager!” is a siren song leading to malware, data theft, and legal risk. The real revelation is that the most powerful secret tools are already in your possession, documented in official platforms and built into your devices. Mastering your App Secret management, using Incognito Mode with realistic expectations, unlocking Developer Options responsibly, and relying on authoritative help resources constitutes a far more valuable and safe form of digital empowerment.
Stop searching for mythical backdoors. Start building your fortress of digital literacy. The next time you see a headline promising a “secret tool,” ask yourself: What is the real secret being protected here? Often, it’s the fact that knowledge, not a magic downloader, is the ultimate key. Invest your time in learning the legitimate, powerful features of the technology you use every day. That is the only “secret tool” worth discovering.