SHOCKING LEAK: Xnxx Sex Pics Exposed In Massive Data Breach!
What if your most private moments—your browsing history, your intimate photos, your secret desires—were suddenly laid bare for the world to see? This isn't a dystopian fiction; it's the alarming reality emerging from a cascade of catastrophic data breaches. The latest shockwave involves Xnxx, a major adult entertainment platform, where millions of users' private content has been exposed. But this incident is far from isolated. It's a chilling chapter in an ongoing saga where billions of personal records, from social media logins to sensitive dating app photos, have been left vulnerable. The pattern is undeniable: from analytics tools to AI chatbots, no corner of our digital lives seems immune. As cybersecurity expert Kurt "Cyberguy" Knutsson warns, the implication is clear—this is not good. So, how did we get here, and more importantly, how can you armor yourself against the next inevitable leak?
The Anatomy of Modern Data Breaches: How Your Data Slips Through the Cracks
Understanding the scale of the problem requires dissecting the mechanics of these leaks. They aren't all masterminded by shadowy hackers exploiting zero-day vulnerabilities (though some are). A shocking number stem from basic security failures—unlocked digital doors left ajar in the vast, complex infrastructure of the modern internet.
The Pornhub Mixpanel Leak: Analytics Tools as Unintentional Weak Links
The first domino in this recent chain involved Pornhub. The platform alerted users after a major data leak exposed user emails and detailed viewing activity. The breach vector was particularly insidious: Mixpanel, a third-party analytics service used to track user behavior. This incident underscores a critical, often overlooked risk: your data's journey doesn't end with the primary service you use. It flows through a labyrinth of third-party integrations—analytics, advertising networks, cloud storage providers—each a potential point of failure. In this case, while passwords and payment details remained secure due to proper encryption, the exposure of viewing history is a profound violation of privacy. It reveals intimate preferences and habits, opening the door to blackmail, phishing, and severe reputational damage. The lesson? Even platforms with robust internal security can be compromised through their supply chain.
- Exclusive Princess Nikki Xxxs Sex Tape Leaked You Wont Believe Whats Inside
- Massive Porn Site Breach Nude Photos And Videos Leaked
- Shocking Leak Exposes Brixx Wood Fired Pizzas Secret Ingredient Sending Mason Oh Into A Frenzy
Secret Desires: When AI Chatbots Become Data Vaults
Next, the breach of "Secret Desires," an erotic chatbot and AI image generator, left millions of user-generated photos and videos vulnerable to the public. This highlights the new frontier of data risk: AI-driven platforms. These services thrive on user input to train models and generate content, amassing vast databases of highly sensitive, personal media. The vulnerability likely stemmed from an unsecured database or API endpoint, a common misconfiguration where data is stored without authentication or encryption. For users, the exposure isn't just a privacy issue; it's a potential lifelong digital scar. Unlike a password, which can be changed, a leaked intimate photo can circulate forever, resurfacing to cause emotional and professional harm years later.
The Unsecured Server Epidemic: A Goldmine for Hackers
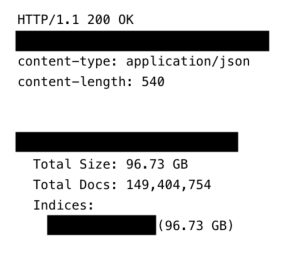
A recurring theme across these breaches is the phrase: "The data was left unsecured and accessible via an [unprotected server/API]." This is the digital equivalent of leaving a bank vault door open with a sign that says "Take Me." Cybersecurity researchers and malicious actors alike constantly scan the internet for misconfigured cloud storage buckets (like Amazon S3), open Elasticsearch clusters, or databases with default passwords. When they find one, they don't necessarily need to "hack" in; they simply download the data. This is often the cause behind the staggering statistics we see: 149 million login credentials from various online services, 184 million+ logins from top platforms, and the record-shattering 16 billion records leaked in the biggest breach in history. These aren't targeted attacks on Fort Knox; they are the digital equivalent of picking low-hanging, poorly guarded fruit.
The Scale of the Problem: A Tsunami of Exposed Identities
The numbers are so vast they become almost abstract. Yet each record represents a human being whose life can be upended.
- Shocking Leak Nikki Sixxs Secret Quotes On Nude Encounters And Wild Sex Must Read
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
- Unseen Nudity In Maxxxine End Credits Full Leak Revealed
The 16 Billion Record Breach: A Historical Low Point
In what is being called the biggest data breach in history, a staggering 16 billion records have been leaked. This monumental haul aggregates credentials from major global platforms over years, likely compiled from multiple previous breaches and now sold or released en masse. It includes usernames and passwords in plain text or weakly hashed formats, making it a treasure trove for credential stuffing attacks (where hackers automatically try stolen passwords on other sites). The sheer volume means that if you have an account on any popular service from the last decade, there's a high probability your credentials are in this dump.
Platform-Specific Catastrophes: From X to Niche Dating Apps
The fallout isn't limited to aggregated data. Specific, high-profile platforms have suffered devastating, targeted leaks:
- X (formerly Twitter) was hit with a massive data breach exposing 200 million records, including email addresses. This data, allegedly linked to an API vulnerability, provides a direct map to user identities, enabling highly targeted phishing and social engineering.
- Pornhub again, this time targeted by the notorious hacking group ShinyHunters, saw over 200 million records exposed. This breach, separate from the Mixpanel incident, likely involved direct intrusion into their systems, highlighting that even after a breach, a platform remains a target.
- The adult and niche dating sector suffered perhaps its most damaging blow since Ashley Madison. Over 1.5 million private photos from users on niche dating apps were exposed. This is the apex of privacy violation, combining personal identifiers with explicit imagery. The Ashley Madison 2015 breach was a watershed moment, but this new leak suggests the problem is escalating, not abating.
The "250 Million Identities" Leak: The Invisible Mass
Adding to the chaos, reports indicate more than 250 million personal identities have leaked online. The phrasing "the leak is almost certainly" larger or more impactful than reported is a crucial insight. Companies often downplay breaches, and many go undetected for months or years. The true scale is a murky, terrifying unknown. This data isn't just emails; it's the full identity package: names, physical addresses, dates of birth, phone numbers, and even national identification numbers (like Social Security Numbers or National Insurance numbers). This is the key that unlocks full identity theft, allowing criminals to open credit lines, file fraudulent tax returns, or commit crimes in your name.
What Type of Data Gets Exposed? From Annoyance to Annihilation
Not all data is created equal. Understanding the hierarchy of exposure helps gauge the risk.
Beyond Passwords: The Danger of Personal Identifiers
While a leaked password is serious, it's often changeable. The real long-term danger lies in static personal data:
- Email Address: Your digital home address. The hub for password resets, a vector for phishing.
- Phone Number: Used for two-factor authentication (2FA) and account recovery. Its exposure can lead to SIM-swapping attacks.
- Physical Address & Date of Birth: Core components for identity verification. Used to answer security questions or apply for credit.
- National ID Numbers: The master key to your financial and governmental identity. Extremely difficult to change.
When this data combines with a breached password, a hacker has a complete toolkit to impersonate you across financial, social, and governmental systems.
How These Breaches Happen: Common Vulnerabilities Exposed
The "how" is often mundane, which is why it's so prevalent.
Misconfigured Databases and Cloud Storage
This is the #1 cause of "unsecured" leaks. A developer sets up a new database for an app, forgets to set a password, or misapplies access permissions. The database is then indexed by search engines like Shodan and found by hackers. It's a human error, not a sophisticated hack.
Third-Party Service Compromises
As seen with the Mixpanel incident, you trust your vendors with your data. If their security fails, yours does too. This creates a domino effect where one breach can expose users across thousands of companies.
API Vulnerabilities
Application Programming Interfaces (APIs) are how software talks to software. If an API endpoint (like the one for X's data leak) doesn't properly authenticate requests, it can spew data to anyone who knows the URL. This is a common flaw in fast-moving development environments.
Insider Threats and Ransomware
Sometimes, the threat comes from within. Disgruntled employees or financially motivated insiders exfiltrate data. Increasingly, ransomware gangs steal data before encrypting systems, then threaten to publish it if a ransom isn't paid—the "double extortion" model. The ShinyHunters group often operates this way.
Protecting Yourself After a Major Leak: 7 Essential Steps from Cyberguy
Kurt "Cyberguy" Knutsson’s advice is a critical action plan. Don't just read it; implement it now.
- Assume You're Breached. The first step is psychological. With billions of records out there, your data is likely in at least one dump. Act accordingly.
- Check Your Exposure. Use reputable sites like HaveIBeenPwned (HIBP). Enter your email and phone numbers. This free service tells you which breaches your accounts appeared in and what data was exposed.
- Change Passwords Immediately… For any account where your password was exposed (HIBP will tell you). Use strong, unique passwords for every single account. A password manager (Bitwarden, 1Password, KeePass) is non-negotiable. It generates and stores complex passwords you can't possibly remember.
- …And Enable Two-Factor Authentication (2FA) Everywhere. This is your single most powerful defense. Even if a password is stolen, a hacker needs the second factor (your phone or security key) to log in. Use an authenticator app (Google Authenticator, Authy) or a physical security key (YubiKey). Avoid SMS-based 2FA where possible, as it's vulnerable to SIM-swapping.
- Scrub Your Digital Footprint. Search for your name, old usernames, and phone number online. Request removal from data broker sites (like Spokeo, Whitepages) that sell your personal info. This reduces the data available for social engineering.
- Monitor Financial and Credit Reports. Get free annual credit reports (AnnualCreditReport.com in the US). Consider a credit freeze with all three major bureaus. This prevents anyone from opening new accounts in your name without your explicit PIN.
- Be Vigilant Against Phishing. Expect a surge in highly targeted "spear phishing" emails and texts using your breached data (e.g., "Hi [Your Name], I saw you on [Site Name]..."). Never click links or open attachments from unsolicited messages. Verify requests for money or information through a separate, known communication channel.
The Inevitability Question: Are We All at Risk?
The relentless parade of breaches—from Xnxx to X, from Pornhub to password dumps of 16 billion—leads to a grim conclusion: complete data security is a myth. The goal is no longer to be unhackable; it's to be resilient. Your strategy must shift from prevention-only to damage control and rapid recovery.
The "leak is almost certainly" worse than reported. Companies hide breaches for fear of reputational and financial damage. Many small to mid-sized businesses lack the tools to even detect a breach. Your data is stored in hundreds of places, many you've forgotten about. The attack surface is infinite.
Conclusion: Your Privacy is a Constant Battle, Not a Given State
The SHOCKING LEAK: Xnxx Sex Pics Exposed in Massive Data Breach! is not an anomaly. It is the logical outcome of a digital economy built on data extraction with inconsistent security standards, a sprawling ecosystem of third-party dependencies, and attackers armed with automated tools scanning for the slightest misconfiguration. From the Mixpanel analytics flaw to the unsecured server holding 1.5 million private dating photos, the story is the same: convenience and speed too often trump security and privacy.
The exposure of names, addresses, dates of birth, emails, phone numbers and even national IDs in these breaches creates a permanent, searchable shadow of your identity. Passwords can be reset. A national ID number cannot. The breach of 200 million records from Pornhub by ShinyHunters or the 250 million personal identities now circulating are not just news headlines; they are direct threats to your financial stability, your personal safety, and your peace of mind.
The path forward is proactive and relentless. Assume you are compromised. Use the seven tips from Cyberguy not as a one-time checklist, but as a new lifestyle for your digital existence. A password manager and 2FA are the bedrock. Regular checks on HaveIBeenPwned are your early warning system. Monitoring your credit is your financial immune system.
The era of trusting companies to safeguard our most intimate data is over. The 16 billion record breach proved that. Your security is now in your own hands. Start building your defenses today, because the next "SHOCKING LEAK" is already being compiled, waiting for the moment an unsecured server is discovered. Don't be the next headline. Be the one who was prepared.