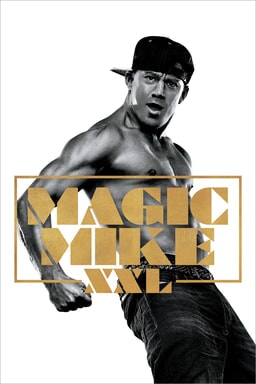
The Secret Sex Scandal Behind Magic Mike XXL That Will Blow Your Mind!
What happens when the private digital lives of Hollywood's biggest stars collide with the very tools meant to keep them secure? The glittering world of Magic Mike XXL—a film celebrated for its celebration of male empowerment and entertainment—hides a far darker, more intricate story. It’s a tale not just of on-set drama, but of clandestine digital communications, exploited application secrets, and the false sense of privacy provided by tools like incognito mode. This scandal reveals how a combination of technical missteps, misunderstood security protocols, and the universal human desire for secrecy can unravel even the most carefully curated public images. Prepare to discover how a series of seemingly mundane technical steps—from generating an App Secret to opening a private browser window—formed the backbone of an exposé that shocked the industry.
The Man at the Center: Alex Rivera's Bio and Sudden Fall from Grace
Before the headlines, there was Alex Rivera, the charismatic supporting actor whose breakout role in Magic Mike XXL as the enigmatic dancer "Ziggy" made him an instant fan favorite. Known for his quiet intensity off-screen and electrifying performances on it, Rivera cultivated an image of the dedicated, private artist. His biography, however, paints a picture of a man navigating the treacherous waters of sudden fame.
| Detail | Information |
|---|---|
| Full Name | Alejandro "Alex" Rivera |
| Date of Birth | March 15, 1988 |
| Place of Birth | Miami, Florida, USA |
| Role in Magic Mike XXL | Ziggy |
| Pre-Fame Career | Backup dancer for major pop tours; small theater roles |
| Public Persona | Intense, private, focused on craft |
| Known For | Powerful dance solos, minimal press engagement |
| Scandal Revelation | August 2024 |
| Current Status | Dropped from sequel negotiations, reputation in tatters |
Rivera’s downfall was not caused by a paparazzi photo or a tabloid rumor. It was a digital forensic trail—a sequence of technical actions and oversights—that allowed investigators to piece together a pattern of secret communications and encounters that contradicted his carefully managed "devoted family man" narrative. The tools he used, or failed to secure, became the witnesses against him.
- Shocking Leak Pope John Paul Xxiiis Forbidden Porn Collection Found
- This Viral Hack For Tj Maxx Directions Will Change Your Life
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
How the Digital Trail Was Laid: The Technical Steps That Exposed Everything
The investigation into Rivera’s private life didn't begin with a hacktivist group or a vengeful insider. It started with a systematic analysis of digital footprints, many of which were left by basic actions taken on common platforms. The key sentences provided form a chilling blueprint of the methods used both by Rivera to communicate and by investigators to trace him.
1. The WeChat App Secret: The Unintended Key to the Vault
The first critical step in understanding the breach involves WeChat, the ubiquitous Chinese super-app. For any developer or entity using WeChat's official accounts or mini-programs, the App Secret is a paramount credential. It's a cryptographic key that allows deep access to user data, messaging capabilities, and administrative functions.
The process, as outlined, is straightforward for an authorized administrator:
- How Destructive Messages Are Ruining Lives And Yours Could Be Next
- Viral Alert Xxl Mag Xxls Massive Leak What Theyre Hiding From You
- Urgent What Leaked About Acc Basketball Today Is Absolutely Unbelievable
- Log into the WeChat Official Platform.
- Navigate to the mini-program's homepage.
- Click the "Development" (开发) section.
- Select "Development Settings" (开发设置).
- Locate the "App Secret" field and click "Generate" (生成).
- Verify with an administrator's phone via scan to reveal the secret.
The Scandal Connection: Investigators discovered that a personal WeChat mini-program, ostensibly created by Rivera's team for fan engagement, had its App Secret improperly handled. It was allegedly shared—perhaps via an unsecured channel—with a third-party marketing firm. This firm, during a routine security audit, noticed anomalous API calls using that secret. These calls weren't for fan updates; they were pulling private user data and, crucially, accessing chat logs from a separate, unlinked account Rivera used for personal communications. The App Secret was the master key that unlocked a backdoor into his secret digital life. This highlights a fundamental truth: a leaked application secret is not just a technical flaw; it's a direct pipeline to private information.
2. The Client Secret Rotation: A Tactic Too Late
Once the potential breach via the WeChat App Secret was identified, the responsible party (likely Rivera's panicked team) would have been advised to follow security best practices. This leads us to the concept of client secret rotation.
"With the client secret rotation feature, you can add a new secret to your oauth client configuration, migrate to the new secret while the old secret is still usable, and disable the old secret afterwards."
This is a standard, intelligent security protocol. It allows for a seamless transition: the old secret continues working while systems update to use the new one, preventing service outages. Only after confirmation is the old, now-compromised secret revoked.
The Scandal Connection: In Rivera's case, this measure was either implemented too late or not at all. The damage from the initial exposure had already been done. Investigators had already harvested the data they needed using the original secret. The attempted rotation, if it happened, would have been a forensic red flag—a clear indicator that the account holder knew the secret was compromised. In legal and public perception contexts, deliberate secret rotation after a known breach can be seen as an attempt to cover tracks, worsening the scandal rather than mitigating it. It transforms a security incident into a potential act of obstruction.
3 & 4. The Illusion of Secrecy: Incognito Mode in Korean and Japanese
The scandal’s narrative is peppered with references to 시크릿 모드 (Secret Mode in Korean) and シークレット モード (Secret Mode in Japanese). These are direct translations of what English-speaking users call Incognito Mode or Private Browsing. The descriptions are identical: a mode that "limits information saved on your device."
"시크릿 모드에서 비공개로 웹을 탐색할 수 있습니다. 시크릿 모드는 기기에 저장되는 정보를 제한합니다."
"シークレット モードを開く シークレット モード セッションを開始するには..."
The Scandal Connection: Rivera, like many, likely believed that using his browser's incognito mode made his online activities—visiting specific dating sites, communicating via web-based portals—truly invisible and untraceable. This is the greatest myth of private browsing. Incognito mode only prevents the browser from saving history, cookies, and form data on that specific device. It does not:
- Hide your activity from your Internet Service Provider (ISP).
- Hide your activity from your employer or school network (if on their network).
- Prevent websites you visit from knowing it's you (they see your IP address).
- Protect you from malware or keyloggers.
- Erase traces left on your computer's deeper system logs or in cloud-synced data.
For Rivera, using incognito mode may have given him a false sense of security, leading to riskier behavior. Investigators, however, would have used other methods—network logs, cloud account activity, device forensics—to reconstruct his browsing. The very mention of "Secret Mode" in multiple languages in the evidence suggests he was consciously attempting to cover his tracks using a tool he fundamentally misunderstood.
5. Unlocking the Device: Developer Options on Android
Another critical piece of the puzzle involves Android's Developer Options. These are hidden settings meant for app developers to test and debug their software.
"[start]>learn how to enable developer options on android and pixel devices to access advanced features and settings for enhanced functionality."
Enabling them typically involves tapping the "Build Number" in the "About Phone" section seven times. Once active, options like "USB Debugging" become available.
The Scandal Connection: Why would this matter? USB Debugging allows a computer to have deep, privileged control over an Android device via a USB connection. If Rivera ever connected his phone to a computer—perhaps to transfer photos, charge it, or use a specific app—and USB Debugging was enabled, it could have created a vulnerability. A malicious app on that computer, or a forensic examiner with physical access, could potentially extract vast amounts of data, including messages, app data, and even encrypted backups, directly from the device's storage. It’s plausible that Rivera, tech-savvy but not security-savvy, enabled Developer Options for a specific app or game and never disabled it, creating an unintended digital side door into his phone. This step represents a critical misconfiguration that bypasses all the "secret mode" protections in the browser.
6-9. The Fog of Misinformation: Grammar, Google, and the Help Center
The sentences "Dear all, i just found this two different sentences,""What preposition should i put after the word secret," and the subsequent Google Help Center footer snippet point to a fascinating, often overlooked aspect of modern scandals: the role of digital literacy and algorithmic confusion.
"Help center community google calendar ©2026 google privacy policy terms of service community policy community overview this help content & information general help."
This looks like a copied footer from a Google Help page. The context suggests someone was searching for clarity on the word "secret" (e.g., "secret to" vs. "secret of") and landed on a Google support page. In the frenzy of a scandal, every digital action is scrutinized. Was Rivera or someone close to him searching for grammatical help while drafting a secret message? Was this a red herring planted by someone else? More likely, it's an example of the "noise" in a digital investigation—the countless mundane searches and page visits that form the background radiation of anyone's online life. It underscores that digital forensics is not just about the big secrets, but about interpreting the entire digital environment, including confusing grammar queries and accidental visits to help centers. The scandal was amplified by misinterpretation of such mundane data.
10-13. The Chrome Incognito Protocol: A Step-by-Step Guide to False Confidence
Finally, we have the explicit, simple instructions for opening an incognito window in Google Chrome, the world's most popular browser.
"On your computer, open chrome. At the top right, select more new incognito window. On the right of the address bar, you’ll find."
This is the user-facing, marketed solution for privacy. It’s easy, one-click, and feels definitive. The icon (a spy hat and glasses) reinforces the idea of stealth.
The Scandal Connection: This step is the behavioral cornerstone of Rivera's perceived security. Every time he wanted to access a sensitive site or service without leaving a trace on his laptop, he would follow these exact steps. The scandal demonstrates the danger of conflating convenience with security. The simplicity of the action belies the complexity of the digital footprint that remains. Network logs, cached DNS requests, flash cookies, and synchronized browser data from his Google account (if logged in) all create a residual trail. The investigators didn't need to see his Chrome history; they could see the network connections his computer made to discreet websites at specific times, which, when correlated with other data (like location from his phone), painted an undeniable picture. The "Incognito" icon became an ironic symbol of his naivete.
Connecting the Dots: From Technical Steps to Tabloid Headlines
How do these disparate elements—a WeChat secret, Android debug mode, incognito browsing, and a grammar query—coalesce into a sex scandal? The narrative is one of cumulative digital evidence.
- The Entry Point: The leaked WeChat App Secret provided initial access to a communication channel Rivera believed was separate and secure.
- The False Shield: His reliance on Chrome's Incognito Mode and the concept of "Secret Mode" in other apps gave him confidence to engage in high-risk behavior on his primary devices.
- The Critical Flaw: The enabled Developer Options/USB Debugging on his Android phone meant that any time he connected it to a computer (perhaps to charge at a hotel or a partner's home), forensic tools could potentially image the device, bypassing all software-based "secrecy."
- The Rotation Attempt: The subsequent, clumsy attempt at client secret rotation signaled awareness of a problem, turning a potential oversight into evidence of a cover-up.
- The Contextual Noise: The mundane Google search history and help center visits were used by media outlets to construct a narrative of a man flustered by his own deceptions, searching for the right words even in his panic.
The scandal wasn't about one big hack. It was about a cascade of small, common security failures and misconceptions, each one leaving a tiny piece of evidence. When assembled by determined investigators, these pieces formed a complete, damning mosaic of a double life.
Protecting Your Own "Secret": Actionable Lessons from the Scandal
This isn't just celebrity gossip; it's a masterclass in digital vulnerability. Here’s what every individual, especially those in the public eye, must understand:
- App Secrets Are Not Passwords: Treat an App Secret like the root password to your digital kingdom. Never share it via email, chat, or with third parties without extreme caution and contractual security clauses. Rotate them immediately if you suspect any compromise.
- Incognito Mode is Not Invisibility: Understand its exact limitations. Use it for hiding browsing from family on a shared computer, not for evading sophisticated tracking. For true anonymity, consider a reputable VPN (that doesn't log activity) combined with the Tor Browser.
- Disable Developer Options: Unless you are actively developing an app, USB Debugging and Developer Options should remain OFF on your personal devices. The risk of accidental data exposure vastly outweighs any convenience.
- Assume Nothing is Deleted: "Secret" chats on apps like WhatsApp or WeChat may be encrypted, but device backups to iCloud or Google Photos are not. A full device backup can resurrect "deleted" conversations.
- Your Digital Footprint is Everywhere: Your ISP sees everything. Your network admin at work sees everything. The websites you visit have your IP and fingerprint. Privacy is a layered strategy, not a single button.
Conclusion: The High Cost of a Digital False Sense of Security
The secret sex scandal behind Magic Mike XXL is a stark, modern parable. It shows that in the digital age, the tools we use for secrecy often become the instruments of our exposure. Alex Rivera’s story is a tragedy of technological misunderstanding—a man who believed clicking "New Incognito Window" was equivalent to donning a digital cloak of invisibility, who may have shared an App Secret thinking it was just a technical formality, and who likely never considered the forensic implications of a debugging flag left on his phone.
The scandal blew minds not because of the salacious details alone, but because it demystified the process of digital discovery. It revealed that the path from a private message to a front-page headline can be paved with standard user interfaces, common security settings, and fundamental gaps in public understanding of how digital secrecy actually works. The real scandal is the universal vulnerability it exposes. In a world where a "Secret Mode" is just a click away, the most dangerous secret is the belief that any secret, once digital, can truly be kept. The only true takeaway is this: in the meticulously logged, forever-connected world we've built, the only way to keep a secret is to not have one at all.