Doxxing Exposed: Why Your Private Leaks Are Only The Start Of Online Horror
Have you ever felt a chill down your spine when a stranger online mentions your street name or the café you frequent? That unsettling sensation is the first whisper of doxxing—a digital nightmare where your private world is weaponized against you. The phrase "Doxxing Exposed: Why Your Private Leaks Are Only the Start of Online Horror" isn't just clickbait; it’s a stark warning that the publication of your address or phone number is often the opening move in a terrifying real-world game. In an era of ubiquitous data, the line between online conflict and offline danger has vanished. This comprehensive guide will dismantle the myth of doxxing as mere "internet drama," revealing it as a severe threat with escalating consequences. We will explore what doxxing truly is, how it happens through both malicious intent and reckless sharing, the devastating real-world impacts, the complex legal battlefield, and, most critically, the actionable steps you can take to report an attack and fortify your digital life.
What Exactly Is Doxxing? Defining the Digital Assassination of Your Privacy
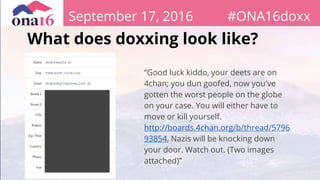
Doxxing—also spelled doxing—is the act of publicly revealing or publishing someone’s private or personal information online without their consent. The term originates from "dropping docs," referring to the documents containing the target's sensitive data. This isn't just about a hacker breaching a mainframe; it’s the malicious online exposure of your private data, which can include your full name, home address, phone number, email, workplace, family members' details, financial information, or private photos.
The key element is non-consensual publication with intent to harm, harass, intimidate, or incite others. It transforms abstract online disagreement into a targeted, real-world threat. Doxxing publishes private personal information such as an address or workplace, but its true danger lies in the context. Publishing a CEO's corporate email is different from posting a private citizen's home address alongside accusations. The latter acts as a beacon for harassment, inviting strangers to show up at their door, call incessantly, or worse. It’s a form of digital vigilantism that bypasses legal due process, handing out sentences of fear and danger based on unverified online claims.
- Tj Maxx Common Thread Towels Leaked Shocking Images Expose Hidden Flaws
- Exclusive Walking Dead Stars Forbidden Porn Leak What The Network Buried
- Ai Terminator Robot Syntaxx Leaked The Code That Could Trigger Skynet
Beyond the Hackers: How Everyday Actions and Reckless Sharing Fuel Doxxing
A common misconception, addressed in our key points, is that doxxing isn’t just about malicious hackers in hoodies. While sophisticated hacking is one vector, the most frequent pathways are shockingly mundane, stemming from our own digital footprints and the platforms we trust. It can also happen through reckless sharing of personal information online, either by ourselves, our connections, or the platforms we use.
Social media platforms are rich with data, and users often overlook how their casual posts create a mosaic of their private lives. Consider:
- Geotags and Check-ins: A photo tagged at your favorite restaurant reveals your routine and location.
- "Friends Only" is a Mirage: A post visible to "Friends" can be screenshot and shared publicly by anyone in that network.
- Metadata in Images: Photos often contain EXIF data with GPS coordinates, camera type, and timestamps.
- Answering "Security Questions": Posting about your first pet or your mother's maiden name gives away answers to common account recovery questions.
- Data Brokers: Companies like Spokeo, Whitepages.com, and PeopleFinder aggregate public records, social media, and other sources to sell detailed dossiers. Your information is likely already on these sites, easily searchable by anyone for a small fee.
Furthermore, doxxing can occur through data breaches where your information is stolen from a company's database and later leaked. The 2023 MOVEit transfer hack exposed millions of records. Once your email and password are in a hacker's hands, they can use it to access other accounts, find more personal details, and eventually assemble a doxxing file. The pathway is rarely a single dramatic breach; it’s a slow drip of exposed data that a motivated actor can compile.
- Maxxine Dupris Nude Leak What Youre Not Supposed To See Full Reveal
- Massive Porn Site Breach Nude Photos And Videos Leaked
- Idexx Cancer Test Exposed The Porn Style Deception In Veterinary Medicine
The Devastating Ripple Effects: Why Doxxing Is Only the Start of the Horror
Doxxing, the act of publicly revealing private information about individuals, carries severe consequences for the victims, affecting them in ways that extend far beyond online distress. Individuals targeted by doxing endure significant repercussions that extend beyond mere online distress; they face tangible, life-altering dangers.
- Physical Harm and "Swatting": This is the most terrifying escalation. Publishing a home address can lead to "swatting"—the false report of a dangerous situation (like a hostage crisis) at the victim's address, triggering a massive, armed police response. This has led to fatalities, as police, expecting violence, arrive in a state of high alert. Victims also face in-person stalking, vandalism, and physical assault from extremists who believe they are justified.
- Psychological Trauma: The violation induces chronic anxiety, PTSD, hypervigilance, and depression. Victims feel their sanctuary is destroyed. The fear of being watched or followed becomes constant. Many report having to move homes, change jobs, and sever social ties to regain a sense of safety.
- Financial Ruin: Doxxing often includes financial details or enables identity theft. Victims may have their bank accounts drained, credit cards opened in their name, or be targeted by sophisticated phishing scams using their leaked information.
- Career and Reputation Destruction: Employers, colleagues, and clients may be exposed to the doxxer's narrative. Even if baseless, the association with online controversy or harassment campaigns can lead to job loss, professional ostracization, and irreparable damage to one's reputation.
- Impact on Family and Loved Ones: Doxxers frequently target family members, publishing spouses' and children's information. This extends the terror to the victim's entire support system, forcing them into hiding as well.
Learn why it escalates recovery risk and the defensive steps that reduce exposure. The initial leak is the spark; the ensuing chaos is the fire. Recovery is a long, expensive process involving legal action, security overhauls, and emotional healing, with no guarantee the harassment will stop.
The Legal Landscape: Is Doxxing a Crime? A Complex Patchwork of Laws
Here’s a breakdown of what doxxing is, how it can happen, how to report it and whether it’s legal. The legality of doxxing is a complex, jurisdictional minefield. There is no single federal law in the United States called "Anti-Doxxing Law." Instead, prosecutors must fit doxxing into existing statutes, which varies wildly by state and country.
- Criminal Laws: Doxxing can be prosecuted under laws related to:
- Stalking/Harassment: Many states have criminal stalking statutes that include credible threats made online. Publishing information with the intent to cause fear can qualify.
- Cyberstalking: Federal law (18 U.S.C. § 2261A) covers using interstate communication (the internet) to stalk or harass.
- Identity Theft: If financial information or Social Security numbers are used or shared.
- Threats: If the doxxing is accompanied by direct threats of violence.
- Conspiracy: If multiple people coordinate the doxxing.
- "Swatting" Laws: Many states now have specific, severe penalties for making false reports that trigger a SWAT response.
- Civil Lawsuits: Victims can sue for:
- Invasion of Privacy (Public Disclosure of Private Facts): Publishing private information that is not of public concern and would be offensive to a reasonable person.
- Intentional Infliction of Emotional Distress (IIED): For extreme and outrageous conduct causing severe emotional trauma.
- Defamation: If false statements are published alongside the private information.
- Platform Terms of Service: All major social media and forum platforms explicitly prohibit doxxing in their Terms of Service. This is often the first and fastest line of defense for removal.
The challenge? Proving intent and connecting the doxxer to the act, especially if they use anonymizing tools. Laws also differ internationally, making cross-border doxxing particularly difficult to prosecute. Learn what doxxing means, how it works, and why it’s dangerous—its danger is amplified by the legal gray zones that can leave victims feeling powerless.
What to Do If You’ve Been Doxxed: An Immediate Action Plan
Learn how doxing works, how to report attacks, and what steps to take if you’ve been doxed. If your private information is published, time is critical. Panic is natural, but a methodical response is essential.
Step 1: Document Everything (Do Not Delete).
- Take screenshots and screen recordings of the post, including the URL, date, time, and number of views/shares if visible.
- Document any subsequent harassment (calls, messages, threats).
- Use tools like
archive.isorarchive.orgto save a permanent, unalterable copy of the webpage.
Step 2: Secure Your Digital Life Immediately.
- Change all passwords to strong, unique ones. Use a password manager.
- Enable two-factor authentication (2FA) on every account (email, social media, banking).
- Review account recovery options (email, phone) and remove any that may have been compromised.
- Check for data breaches on sites like
HaveIBeenPwned.comand change passwords on affected accounts. - Remove geotags from existing social media photos and disable future location sharing.
Step 3: Report to the Platform.
- Use the platform's reporting tools for "Privacy Violation," "Harassment," or "Threats." Provide your documentation.
- Report multiple times if the post is shared across different groups or pages. Be persistent.
Step 4: Contact Law Enforcement.
- File a report with your local police department. Bring all your documentation. Even if they can't act immediately, it creates an official record.
- If the threat is imminent (e.g., you believe someone is coming to your home), call 911 immediately.
- In the U.S., you can also report to the FBI's Internet Crime Complaint Center (IC3). Other countries have similar national cybercrime units.
Step 5: Seek Legal Counsel.
- Consult with a lawyer specializing in cyberlaw, privacy, or harassment. They can advise on civil suits, restraining orders, and cease-and-desist letters.
- Legal aid societies or cybercivil rights initiatives (like the Cyber Civil Rights Initiative) may offer resources or referrals.
Step 6: Alert Your Inner Circle.
- Inform your family, employer, and close friends about the situation. Warn them about potential phishing attempts or impersonation. Ask them not to engage with harassers.
Step 7: Consider a Data Removal Service.
- Services like DeleteMe, Incogni, or Jumbo can help scrub your personal data from data broker sites, a major source of aggregated information for doxxers. This is a longer-term mitigation strategy.
Proactive Defense: How to Lock Down Your Digital Footprint and Protect Your Personal Data
Protect your personal data from online exposure. The best defense is a proactive offense. Discover real examples and essential tips to protect yourself online by treating your digital footprint as a fortress under constant siege.
1. Master Your Social Media Privacy:
- Audit Settings Quarterly: Go through every privacy setting on Facebook, Instagram, Twitter/X, LinkedIn, etc. Set "Who can see your friends list?" to "Friends" or "Only Me." Limit who can see your past posts.
- Assume Nothing is Private: Never post anything you wouldn't want on a billboard. Avoid sharing:
- Home or work addresses.
- Daily routines (gym times, school drop-offs).
- Geotagged photos in real-time. Post them days later.
- Photos of your children's school uniforms, license plates, or mail with your address.
- Be Wary of Quizzes and Apps: Those fun "What's your superhero name?" quizzes often harvest your data and your friends' lists. Think before you authorize any third-party app.
2. Dismantle Your Data Broker Dossier:
- Search Yourself: Regularly search your name, phone number, and address on Google and on major data broker sites (Spokeo, Whitepages, BeenVerified, PeopleFinder, Instant Checkmate).
- Opt-Out Manually: Most brokers have an opt-out process, but it's often deliberately difficult and hidden. You must do it for each site individually. Document your requests.
- Use Data Removal Services: For a fee, services like DeleteMe or Incogni will handle the tedious opt-out process for dozens of brokers and monitor for re-listing. This is a highly effective, if costly, layer of protection.
3. Harden Your Core Accounts:
- Password Manager: Use one (Bitwarden, 1Password, Dashlane) to generate and store complex, unique passwords for every account.
- Two-Factor Authentication (2FA):Always use an authenticator app (Google Authenticator, Authy) or a security key (Yubikey). SMS-based 2FA is vulnerable to SIM-swapping attacks.
- Separate Email Addresses: Use a dedicated, anonymous email for non-critical sign-ups and forums. Never use your primary email for public-facing accounts.
- Recovery Questions: Use fake answers stored in your password manager. Your mother's real maiden name is not a secret if it's on public genealogy sites.
4. Cultivate Digital Hygiene Habits:
- Think Before You Share: The 10-second rule. Is this information necessary? Could it be used against me or someone I love?
- Educate Your Circle: Talk to family, especially older relatives and children, about privacy. Their oversharing can expose you.
- Use a VPN: A reputable Virtual Private Network masks your IP address, making it harder to link your online activity to a physical location, especially on public Wi-Fi.
- Regular Security Scans: Use tools like Malwarebytes and your antivirus to scan for keyloggers or spyware that could capture your keystrokes and private data.
5. Prepare an Incident Response Plan:
- Have a secure, offline folder (digital or physical) with:
- Key account passwords (stored in a password manager, of course).
- Copies of important IDs (driver's license, passport) in case you need to prove identity for new accounts or to police.
- Contact information for your lawyer, local police cyber unit, and a trusted IT support person.
- A checklist of the immediate steps from the previous section.
Conclusion: Your Privacy is a Battlefield—Start Fortifying Today
Doxxing Exposed: Why Your Private Leaks Are Only the Start of Online Horror has traversed the grim landscape of this modern threat. We've seen that doxxing is not a prank but a malicious act of online exposure designed to inflict real-world harm. It thrives not only on the work of dedicated hackers but on the reckless sharing of personal information we all sometimes do, amplified by the data-hungry ecosystem of social media platforms and data brokers. The consequences—swatting, stalking, financial ruin, psychological trauma—are severe and life-disrupting.
The legal path is fraught with challenges, making proactive defense your most powerful weapon. Protecting your personal data requires a shift from passive sharing to active guarding. It means auditing your social media, opting out of data brokers, hardening your accounts with a password manager and authenticator apps, and cultivating relentless digital hygiene. Learn what doxxing is, how it works, and how to protect your personal information from it—this knowledge is your primary shield.
If you are targeted, remember the action plan: Document, Secure, Report, Involve Authorities, Seek Legal Help. Do not engage with the harassers. Let the systems of platforms and law enforcement work, while you work to secure your world.
The internet does not have to be a horror story of exposed privacy. By understanding the mechanisms of doxxing and rigorously applying these defensive steps, you reclaim control. Your private life is not public commodity. Start fortifying your digital footprint today, because in the battle for your privacy, the best victory is the one where the enemy never finds a foothold.