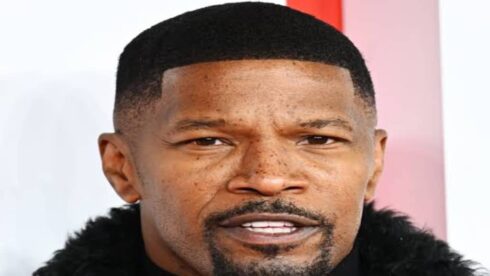
SHOCKING LEAK: Jamie Foxx And Drake's 'Type' Fetish Exposed—Nude Photos And Secret Messages!
What would you do if your most private messages and photos were suddenly public? For high-profile figures like Jamie Foxx and Drake, this isn't just a hypothetical—it's a recurring nightmare. Recent rumors swirl around a shocking leak allegedly exposing the duo's intimate "Type" fetish, complete with nude photos and secret messages. While the veracity of this specific claim remains unconfirmed, it underscores a terrifying reality: no one is safe from digital exposure. Whether you're a celebrity or an everyday internet user, your online footprint can be exploited. But here’s the empowering truth: you hold more control than you think. Major platforms like Google have baked-in powerful, often overlooked tools designed to protect your privacy and security. This article dives deep into the alleged scandal, then pivots to actionable strategies using Google’s ecosystem—from account hardening to secure browsing—so you can navigate the web with confidence, regardless of your "type" or notoriety.
Who Are Jamie Foxx and Drake? A Brief Biography
Before dissecting the leak, it’s crucial to understand the individuals at the center of the storm. Both are iconic figures whose careers span decades, yet their digital vulnerabilities highlight a universal risk.
| Full Name | Jamie Foxx | Drake |
|---|---|---|
| Birth Date | December 13, 1967 | October 24, 1986 |
| Profession | Actor, Singer, Comedian, Producer | Rapper, Singer, Songwriter, Actor |
| Notable Works | Ray (Academy Award), Collateral, In Living Color, Blame It | Take Care, Scorpion, Views, God’s Plan |
| Awards | Academy Award, Golden Globe, SAG Award | 5 Grammy Awards, 27 Billboard Music Awards |
| Public Persona | Known for versatility in comedy, drama, and music; active on social media. | One of the most streamed artists globally; deeply engaged with fans via social platforms. |
Both men maintain massive online presences, sharing snippets of their lives, music, and humor. This visibility, while career-boosting, exponentially increases their attack surface for hackers, scammers, and data harvesters. The alleged "Type" fetish leak—whether real or fabricated—serves as a stark reminder: digital intimacy is fragile.
- Exclusive Princess Nikki Xxxs Sex Tape Leaked You Wont Believe Whats Inside
- Sasha Foxx Tickle Feet Leak The Secret Video That Broke The Internet
- Xxxtentacions Nude Laser Eyes Video Leaked The Disturbing Footage You Cant Unsee
The Alleged Leak: A Wake-Up Call for Digital Privacy
Rumors of a leak involving Jamie Foxx and Drake purportedly reveal private conversations and images referencing a shared "Type" fetish. While no major news outlet has verified these claims (and they may be part of a malicious disinformation campaign), the narrative itself is a textbook case of celebrity data exploitation. Such leaks often originate from:
- Compromised Accounts: Weak passwords, reused credentials, or successful phishing attacks can grant hackers access to email, cloud storage, or messaging apps.
- Malicious Insiders: Sometimes, individuals with legitimate access leak content for money or notoriety.
- Data Broker Breaches: Information aggregated from multiple breaches can be stitched together to create a damaging narrative, even if the core "photos" are fake.
For the average person, the stakes might seem lower, but the tactics are identical. A leaked private photo, a confidential work document, or a sensitive health query can lead to blackmail, identity theft, or reputational ruin. The Jamie Foxx/Drake scenario, sensational as it is, distills a critical lesson: your digital life is a treasure trove for bad actors. So, how do you fortify your defenses? You start with the very tools you use daily—your Google account and browser.
Taking Control: Google’s Privacy and Security Toolkit
Google isn’t just a search engine; it’s a comprehensive digital ecosystem. The key sentences provided are not random—they are direct pointers to built-in security features often ignored by users. Let’s unpack each one, transforming them from cryptic phrases into your personal security protocol.
- 2018 Xxl Freshman Rappers Nude Photos Just Surfaced You Have To See
- This Traxxas Slash 2wd Is So Sexy Its Banned In Every Country The Truth Behind The Legend
- Ai Terminator Robot Syntaxx Leaked The Code That Could Trigger Skynet
Maximize Account Security with "Encore Plus" Account Options
The phrase "Encore plus » account options" (French for "Even more account options") points to the Google Account dashboard—a control center most users visit only to change their profile picture. Dig deeper, and you’ll find a fortress of settings.
- Two-Factor Authentication (2FA): This is non-negotiable. 2FA requires a second verification step (like a code from an authenticator app) beyond your password. Even if your password is stolen, hackers cannot bypass this. Enable it under Security > 2-Step Verification.
- Recovery Information: Ensure your recovery phone and email are up-to-date and secure. This is your lifeline if you get locked out.
- Your Devices: Regularly review "Your devices" under Security. Remove any unfamiliar phones, laptops, or tablets. A hacker with your password could have logged in from an unknown device.
- Third-Party App Access: Under Security > Third-party apps with account access, revoke permissions for apps you no longer use. A forgotten quiz app from 2015 could still be reading your emails.
- Data & Personalization Controls: Here you can auto-delete activity data (like location history, searches) after 3 or 18 months. Minimizing stored data minimizes breach impact.
Actionable Tip: Spend 20 minutes this week touring your Google Account Security page. Treat it like a financial audit—every unknown entry is a red flag.
Explore New Search Capabilities Without Sacrificing Privacy
"Explore new ways to search" and "Download the google app to experience lens, ar, search labs, voice search, and more" highlight Google’s innovative, but data-rich, features. While exciting, each collects unique data.
- Google Lens: Uses your camera to search what you see. It can process images in real-time. Be mindful: pointing Lens at sensitive documents or private screens can upload that imagery to Google’s servers.
- Augmented Reality (AR): AR searches overlay digital info on your real-world view. This requires camera and location access, creating a detailed behavioral profile.
- Search Labs: Experimental AI features (like SGE - Search Generative Experience) that generate answers. These often process queries in new ways, with unclear data retention policies.
- Voice Search: Always listening on devices? On mobile, voice inputs are stored. Review and delete your voice & audio activity in your Google Account.
The Privacy Paradox: These features are incredibly useful but trade convenience for data. Mitigation: Use them selectively. For highly sensitive searches, switch to a privacy-focused engine like DuckDuckGo in a private window. In the Google app, disable personalized results under Settings > Search > Personal results if you prefer anonymity.
The Critical Importance of Private Browsing
"S'il ne s'agit pas de votre ordinateur, utilisez une fenêtre de navigation privée pour vous connecter" translates to: "If it's not your computer, use a private browsing window to log in." This is a golden rule of cyber hygiene.
- What Incognito/Private Mode Does: It prevents the browser from saving your local history, cookies, and form data on that device. When you close the window, that session vanishes from the machine.
- What It Does NOT Do: It does not make you anonymous to your employer, your internet service provider (ISP), or the websites you visit. Your IP address and activity are still visible to them. It also doesn't protect against malware or keyloggers.
- When to Use It: On any public or shared computer (library, hotel, friend's laptop). It ensures you don't leave behind passwords, session cookies, or search history for the next user.
- The Celebrity Angle: Imagine Jamie Foxx checking his email on a production laptop. Without a private window, his login session could persist, allowing the next person to access his account. A simple incognito window would have prevented this.
Common Misconception: "Private browsing keeps me safe from hackers." It does not. It only protects your privacy on that specific device after you leave.
Leveraging Guest Mode for Shared Devices
"En savoir plus sur l'utilisation du mode invité suivant créer un compte français (france) afrikaans" is a garbled phrase but essentially advises: "Learn more about using guest mode after creating an account [in a specific language]." It points to Chrome's Guest Mode.
- What is Guest Mode? It allows someone to use your Chrome browser without signing into their own Google account or altering your settings. It’s a completely separate, temporary profile.
- When to Use It: Let a colleague or family member use your computer for a quick search without risking your saved passwords, bookmarks, or extensions. It’s more secure than just using your logged-in profile.
- How to Access: Click your profile icon in the top-right of Chrome and select "Guest".
- Language Note: The mention of "français (france) afrikaans" likely refers to Chrome's language settings. You can set your browser interface to any language, but Guest Mode operates in the system's default. This is irrelevant to security but shows Google's localization.
Key Difference from Incognito: Guest Mode is for sharing your device with another person. Incognito is for your own private session on a shared device.
Why Chrome is Your First Line of Defense
"Gagnez en efficacité grâce au nouveau chrome, un navigateur internet plus simple, plus sécurisé et encore plus rapide grâce aux fonctionnalités intelligentes de google intégrées." Translation: "Gain efficiency with the new Chrome, a simpler, more secure, and faster internet browser thanks to integrated intelligent Google features." This isn't just marketing; Chrome has robust, automatic security.
- Sandboxing: Each tab and extension runs in an isolated "sandbox." If one tab is compromised by malware, it can't easily infect other tabs or your system.
- Safe Browsing: Chrome constantly checks websites against Google’s list of dangerous sites (phishing, malware). You get a bright red warning before visiting.
- Automatic Updates: Chrome updates itself silently in the background. These updates patch security vulnerabilities immediately. Using an outdated browser is like leaving your front door unlocked.
- Password Manager: Chrome can generate and store strong, unique passwords. It also alerts you if a password has been compromised in a known breach (Password Checkup).
- Site Isolation: A newer feature that further contains threats by separating websites into different processes.
Efficiency vs. Security: The "intelligent Google features" (like autofill, translation) can be double-edged. They save time but store data. Balance is key: use the password manager, but consider disabling autofill for highly sensitive forms (like banking) if you share your device.
Customizing Your Google Experience Safely
"Votre compte vous offre plus de possibilités en personnalisant votre expérience google et en vous proposant un accès facile à vos informations les plus importantes, où que vous soyez." Means: "Your account offers more possibilities by customizing your Google experience and providing easy access to your most important information, anywhere."
This is the core trade-off: personalization requires data. Your Google account syncs bookmarks, history, passwords, and preferences across all your devices. This is incredibly convenient but creates a centralized data profile.
- Sync Settings: Go to chrome://settings/syncSetup (or Account > Data & Personalization > Sync). You can choose what to sync. For maximum privacy on a shared work computer, sync only passwords. On your personal device, sync everything for convenience.
- Ad Personalization: Under Ad Settings, you can turn off ad personalization. Google will still show ads, but they won't be based on your personal data. This reduces the "filter bubble" and data aggregation.
- Location History: This is a major tracker. Decide if you need it. You can pause it or set it to auto-delete.
- Web & App Activity: This includes your searches and interactions with Google services. Pausing this breaks personalization but drastically cuts data collection.
The "Anywhere" Promise: The ability to access your info anywhere is why we use these services. The security imperative is to lock down that access with a strong, unique password and 2FA. Your "important information" should only be accessible to you.
Practical Steps to Secure Your Digital Life Today
Knowledge is power, but action is security. Here is a consolidated, step-by-step checklist derived from the key sentences:
Audit Your Google Account (15 mins):
- Visit myaccount.google.com/security.
- Enable 2-Step Verification using an authenticator app (Google Authenticator, Authy) or a security key (YubiKey). Avoid SMS-based 2FA if possible, as it can be hijacked.
- Review "Your devices" and remove any you don't recognize.
- Check "Third-party apps with account access" and revoke unused apps.
- Set "Auto-delete" for Web & App Activity and Location History.
Master Your Browser (10 mins):
- Ensure Chrome is updated (Settings > About Chrome).
- In Settings > Privacy and Security, review:
- Cookies and other site data: Block third-party cookies.
- Site Settings: Review permissions for camera, microphone, location. Set to "Ask before accessing."
- Enable "Safe Browsing" (Enhanced protection if you're comfortable with some data sharing for maximum security).
- Use Guest Mode for one-time users on your computer. Use Incognito Mode for your private searches on any computer.
Practice Mindful Searching (Ongoing):
- For routine searches, use your logged-in Chrome for convenience.
- For sensitive searches (health, legal, financial), use Incognito Mode or a separate privacy-focused browser/profile.
- Regularly clear your Google Search history if you don’t want it shaping future results or being stored.
- Be skeptical of "search labs" and AR features—understand what data they collect before using them.
Password Hygiene:
- Let Chrome’s password manager generate and store unique passwords for every site.
- Never reuse passwords. A breach on a low-stakes forum can compromise your Gmail.
- Periodically run Password Checkup (in your Google Security settings) to see if any saved passwords have been exposed in a breach.
Assume Nothing is Fully Private:
- No mode, not even Guest Mode, protects against sophisticated malware or physical surveillance.
- The most secure "private" photo is one never taken or stored on a connected device.
- Encrypt sensitive files before uploading to cloud storage.
- For truly confidential communications, use end-to-end encrypted apps like Signal, not standard SMS or unencrypted email.
Conclusion: From Celebrity Scandal to Personal Empowerment
The alleged "Type" fetish leak involving Jamie Foxx and Drake is more than tabloid fodder; it’s a digital sovereignty crisis. It demonstrates how personal, intimate data can be weaponized, regardless of fame or fortune. While we cannot control malicious hackers or treacherous insiders, we can dramatically reduce our attack surface by mastering the privacy controls already at our fingertips.
The key sentences—from "Encore plus account options" to "Votre compte vous offre plus de possibilités"—are not just technical jargon. They are the pillars of a defensive digital lifestyle. Enhancing account options builds your fortress. Exploring search wisely balances utility with caution. Using private and guest modes respects context and shared spaces. Relying on Chrome’s security provides a baseline of protection. Customizing your experience ensures you trade data only for value you explicitly accept.
The shocking leak should shock you into action, not despair. Your digital footprint is your responsibility. Start today: audit one setting, enable one security feature, practice one new habit. In an era where nude photos and secret messages can define a narrative, your best defense is a proactive, informed, and securely configured digital presence. Don’t wait for a leak to happen to you. Build your shields now.