TERRIFYING: How Doxxing Exposes Your Leaked Porn And Private Life!
{{meta_keyword}}
What if a single post, a forgotten photo, or a casual comment could unravel your entire private life? What if that digital breadcrumb trail led not just to your doorstep, but to the most intimate corners of your existence—your leaked porn, your home address, your family’s safety—all weaponized against you? This isn't a dystopian fiction; it's the terrifying reality of doxxing. The act of publicly revealing private information has evolved from a niche hacker tactic into a pervasive weapon of online terror, capable of destroying lives in minutes. One moment of online activity can make you a target, and the fallout is devastating, affecting your emotional well-being, physical safety, and professional future. But understanding this threat is the first step to defense. This guide breaks down exactly what doxxing is, how it happens, the severe consequences you face, and—most critically—the preventative measures you can take right now to protect your data, set firm boundaries, and fight back in a digital world often designed to exploit silence.
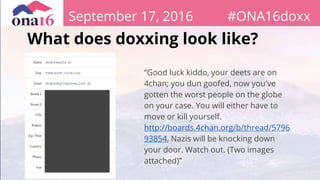
What Exactly Is Doxxing? A Breakdown of the Cyberbullying Epidemic
The term “doxxing” (or “doxing”) is used to describe the act of making someone’s private or sensitive information public on the internet, typically with malicious intent. It is considered a form of cyberbullying, but one that often transcends the digital realm, spilling into real-world violence and harassment. At its core, doxxing is about power and control—using information as a weapon to intimidate, silence, or harm an individual. The information revealed can range from seemingly mundane details like a phone number or workplace to the deeply personal and traumatic, including leaked porn, medical records, financial data, or home addresses.
- This Viral Hack For Tj Maxx Directions Will Change Your Life
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
- Shocking Exposé Whats Really Hidden In Your Dixxon Flannel Limited Edition
The psychology behind doxxing is rooted in anonymity and mob mentality. Perpetrators, hiding behind screens, believe they are untouchable. They gather fragments of data—a username here, a geotagged photo there, a forgotten forum post—and piece them together like a digital puzzle. Once published on platforms like 4chan, Reddit, or dedicated “dox” sites, this information is disseminated to a vast, often vengeful audience. The goal is to invite harassment, stalking, and threats from others, effectively outsourcing the attack to a digital mob. This isn't just about malicious hackers in hoodies; it can also happen through reckless sharing of personal information online by the victim themselves, creating an open book for anyone with ill intent to read.
How Doxxing Happens: The Digital Breadcrumb Trail
You might think you’re safe if you never engage in controversial topics, but doxxing isn’t just about malicious hackers. Often, the information used comes from your own digital footprint, carelessly left behind. Social media platforms are rich with data, and users often underestimate how much they reveal. A vacation photo with a visible mailbox provides a home address. A LinkedIn update announces a new job and workplace. A fitness app shares daily running routes. A decade-old forum post under an old username can be linked to your current identity through data breaches or simple sleuthing.
One post is all it takes to become a target of doxxing. A heated political argument, a critical comment about a public figure, or even defending someone else can mark you. Perpetrators then engage in OSINT (Open-Source Intelligence) gathering. They cross-reference your social media profiles, use reverse image search on your photos, check data breach databases for your old emails, and even scrape public records. They look for any connection: a mutual friend’s tagged photo, a reused password from a breached site, a mention in a family member’s public post. Learn how your online activity can be used against you—that enthusiastic “Check out my new house!” post with a street sign in the background? That’s a gift to a doxxer. Not giving out any personal info without proxy, like a po box or burner email, is a fundamental shield, but many never consider these tools until it's too late.
- Kenzie Anne Xxx Nude Photos Leaked Full Story Inside
- Unbelievable How Older Women Are Turning Xnxx Upside Down
- Heather Van Normans Secret Sex Tape Surfaces What Shes Hiding
The Four General Types of Doxxing Events
While anyone can fall victim to doxxing, our experts have broken down doxxing events into four general types, each with a distinct motive and method:
- Targeted Harassment / Revenge Doxxing: This is the most common. It stems from a personal conflict—an ex-partner, a disgruntled coworker, or someone you had an online dispute with. The goal is to ruin your life by exposing your private info to encourage stalking, threats, and job loss. Leaked intimate images are a frequent, devastating weapon in this category.
- Mistaken Identity Doxxing: Here, the perpetrator targets the wrong person. Someone with a similar username, a shared last name, or who simply resembles the intended target gets caught in the crossfire. The consequences are just as severe for the innocent victim, who must then prove their identity while under attack.
- Political / Ideological Doxxing: Activists, journalists, and outspoken individuals are targeted to silence them. Their personal information is released to intimidate them, their families, and their colleagues, often with the tacit or explicit support of opposing groups. This form aims to suppress free speech through fear.
- Financial Motive / "Swatting" Doxxing: In this brazen type, the revealed information (like a home address) is used to facilitate a physical crime. The most notorious example is "swatting," where a false report of a violent crime (like a hostage situation) is made to the victim's local police, hoping to send a SWAT team to their door. This turns digital harassment into a potentially lethal real-world encounter.
The Devastating Consequences: More Than Just Online Harassment
Doxxing, the act of publicly revealing private information about individuals, carries severe consequences for the victims, affecting them emotionally, physically, and professionally. The impact is a cascading disaster:
- Emotional & Psychological Trauma: Victims experience intense anxiety, paranoia, depression, and PTSD. The feeling of being constantly watched, the fear of opening the door, and the violation of having your most private self exposed is profoundly damaging. Online abuse is real—and it’s terrifying. The relentless stream of hate messages, threats of violence, and sexual harassment can make victims feel unsafe in their own homes and isolated from support networks.
- Physical Safety Risks: Exposed home addresses and daily routines invite stalking, vandalism, and physical assault. The threat of swatting introduces the danger of a violent police encounter. Victims are often forced to relocate, change routines, and invest in security systems, living in a state of perpetual hyper-vigilance.
- Professional & Financial Ruin: Employers conducting simple online searches can find doxxed information, leading to termination, especially if it involves leaked porn or controversial associations. Clients and colleagues may distance themselves. Victims may incur significant costs for legal fees, identity theft protection, credit monitoring, and temporary housing.
- Reputational & Social Damage: Relationships with family and friends can fracture under the strain of public scrutiny and associated harassment. The social stigma, particularly around sexualized leaks, can be lifelong and isolating.
Your Digital Armor: Preventative Measures and Proactive Protection
The harsh truth is, there isn't so much handling as there are preventative measures. Once your information is out there, containing it is a nightmare. The focus must be on building a fortress before you're attacked. Learn how to protect your data, set boundaries, and fight back with these essential strategies:
1. Master Your Social Media Privacy: Treat every platform as a public billboard by default. Go through every privacy setting. Make profiles private. Disable location tagging on photos. Audit your friends/followers lists. Assume anything posted can be screenshot and shared.
2. Use Proxies and Burner Information:Not giving out any personal info without proxy is non-negotiable. Use a PO Box for online shopping and non-essential mail. Create a dedicated burner email (using a secure provider like ProtonMail) for forums, newsletters, and any site that isn't banking or primary communication. Never reuse passwords.
3. Scrub Your Digital Footprint: Regularly Google yourself. Use services like haveibeenpwned.com to check for data breaches involving your emails. Request removal of personal data from data broker sites (like Spokeo, Whitepages) — this is tedious but crucial.
4. Secure Your Core Accounts: Your primary email and phone number are the keys to your digital kingdom. Protect them with the strongest, unique passwords and two-factor authentication (2FA) using an authenticator app (not SMS, which can be SIM-swapped).
5. Practice Operational Security (OpSec): Be mindful of what you share in real-time. Avoid geotagging. Use a VPN on public Wi-Fi. Be suspicious of quizzes and apps that ask for personal details (mother's maiden name, first pet) that could be security questions.
6. Educate Your Circle: Your family's oversharing can expose you. Talk to partners, parents, and children about the risks of posting your info or photos. Secure their social media accounts with strong privacy settings too.
If You're Doxxed: Immediate Steps to Report and Respond
Learn how doxing works, how to report attacks, and what steps to take if you’ve been doxed. Time is critical.
- DOCUMENT EVERYTHING: Immediately take screenshots and archive URLs of the doxxing post and any ensuing harassment. Include dates, times, and usernames. This is your evidence for police and platforms.
- REPORT TO THE PLATFORM: Use the platform's (Reddit, Twitter, Facebook, 4chan) official reporting tools for privacy violations and threats. Be persistent. For content hosted on websites, look for a DMCA or "Report Abuse" link.
- CONTACT LAW ENFORCEMENT: File a report with your local police. Bring your documentation. While cyber laws are complex, this creates an official record. If threats are imminent (like swatting), call 911 immediately. You can also report to the FBI's Internet Crime Complaint Center (IC3) for federal offenses.
- SECURE YOUR IDENTITIES: Change passwords on all accounts, especially email and banking. Enable 2FA everywhere. Contact your bank and credit bureaus (Experian, Equifax, TransUnion) to place fraud alerts or credit freezes.
- INFORM YOUR NETWORK: Alert your employer (HR/Legal), family, and close friends. They can be vigilant for suspicious activity and provide support.
- SEEK PROFESSIONAL HELP: Consult a lawyer specializing in cyber law or harassment. Consider services like takedown experts or online reputation management firms for persistent removal issues. Prioritize your mental health with a therapist experienced in trauma.
The Legal Landscape: Is Doxxing Illegal?
The legality of doxxing is a complex patchwork. Is doxxing illegal? Often, yes, but not under a single universal "anti-doxxing" law. Prosecution typically relies on existing statutes:
- Harassment & Stalking Laws: Most states have laws against cyber harassment and stalking. Publishing info with intent to cause fear or distress can violate these.
- Threats & Assault Laws: If the doxxing is accompanied by threats of violence ("I know where you sleep"), it can constitute criminal threats.
- Interstate Communications & Cyberstalking: Federal laws, like the Interstate Communications Statute and the Computer Fraud and Abuse Act (CFAA), can apply if the perpetrator crosses state lines or uses interstate communications (which the internet always does).
- Data Protection Laws: In regions like the European Union (under GDPR) and California (under CCPA), the reckless sharing of personal data can violate privacy regulations, though these are more often used against companies than individuals.
- Specific "Swatting" Laws: Many jurisdictions now have specific laws against making false reports to emergency services, recognizing the extreme danger of swatting.
The challenge is attribution—finding the anonymous perpetrator—and proving intent. This is why preventative measures are so vital; the legal process is slow and uncertain for victims already in crisis.
The Bigger Picture: Why Women and Marginalized Groups Are Primary Targets
Online abuse is real—and it’s terrifying, but its impact is not evenly distributed. Learn how to protect your data, set boundaries, and fight back in a digital world designed to exploit women’s silence. Doxxing is a gendered weapon. Women, LGBTQ+ individuals, people of color, and activists are disproportionately targeted. The threat of leaked porn (often called "revenge porn" when distributed by ex-partners) is a specific and brutal form of doxxing used to shame, control, and silence women. The goal is often to force them offline, to punish them for having a voice, a sexuality, or an opinion.
This isn't accidental. It stems from deep-seated misogyny and a desire to police behavior. The "exploitation of women's silence" is a strategic tactic: if the threat of having your most intimate moments broadcast to your boss, family, and community is used to keep women quiet online, then the digital public square remains a male-dominated space. Fighting doxxing, therefore, is not just about personal privacy; it's about digital equity and safety. It requires platforms to take stronger action, lawmakers to create better protections, and a collective shift in culture that refuses to blame the victim for the perpetrator's crime.
Conclusion: Your Privacy is a Right, Not a Privilege
The terrifying truth about doxxing is that it turns our connected world against us. The very tools that empower us—social media, easy communication, public platforms—can be twisted into instruments of terror. The exposure of leaked porn and private life is not a hypothetical risk; it's a daily reality for thousands, leaving scars that never fully heal. However, this guide has shown that knowledge is your strongest shield. Doxxing works by exploiting carelessness and anonymity. You can break that chain.
Protect your personal data from online exposure by adopting a mindset of proactive defense. Audit your digital life. Use proxies and burner information. Secure your core accounts. Understand that your online activity is a permanent record. If the worst happens, know the steps: document, report, secure, and seek help. Doxxing carries severe consequences, but those consequences must land on the perpetrators, not the victims. By taking control of your digital footprint, setting ironclad boundaries, and refusing to be silenced, you reclaim your power. Your private life is yours to protect. Start today.