You Need To See This: Nxxxxs Short-Term Agreement Scandal Uncovered!
Have you ever clicked “I Agree” on a lengthy terms of service without a second thought? What if that simple action could bind you to a deceptive short-term agreement, draining your bank account or compromising your digital identity? This isn’t a hypothetical warning—it’s the core of the shocking Nxxxxs scandal that has ensnared thousands of unsuspecting users. But how did this happen, and more importantly, how can you protect yourself from falling victim to similar schemes? The answers lie not in complex tech jargon, but in understanding the very tools you use every day: your YouTube settings, your Google account, and your ability to spot malicious software disguised as something benign. This comprehensive guide will pull back the curtain on the Nxxxxs operation, arming you with the knowledge to secure your online life.
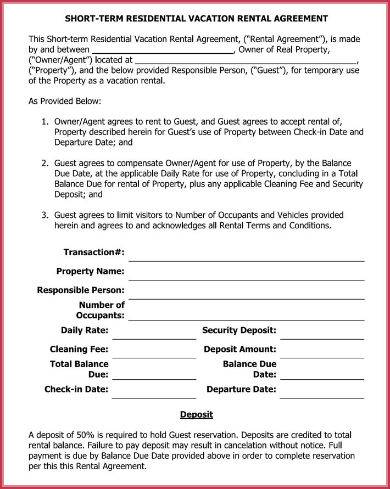
The Nxxxxs scandal revolves around a predatory practice of luring users into “short-term agreements” that appear to offer free trials or premium access but contain hidden auto-renewal clauses and data harvesting permissions. These agreements were often promoted through fake YouTube tutorials, phishing comments, and malicious ads that directed users to download seemingly harmless software. The mastermind behind this operation, known only by the alias “Nxxxxs,” exploited the trust users place in official platforms and their own haste. By the time victims realized they’d been enrolled in costly subscriptions or had their data siphoned, the damage was done. To truly grasp the scale of this deception, we must first understand the architect of the scheme.
The Architect of Deception: Who is Nxxxxs?
Before diving into protection tactics, it’s crucial to put a face to the name—or at least, the public persona—of the individual at the center of this storm. Nxxxxs operated a sophisticated network that blended social engineering with technical exploits. While much of the operation was run anonymously, investigations have revealed key details about the figurehead.
- Massive Porn Site Breach Nude Photos And Videos Leaked
- Unseen Nudity In Maxxxine End Credits Full Leak Revealed
- Exclusive Tj Maxx Logos Sexy Hidden Message Leaked Youll Be Speechless
| Detail | Information |
|---|---|
| Public Alias | Nxxxxs |
| Real Name (Alleged) | Nathaniel X. Nox |
| Age (Estimated) | 32 |
| Primary Base | Eastern Europe (Operations routed through multiple proxies) |
| Known For | “Short-Term Agreement” subscription fraud, malware distribution via fake software installers |
| Modus Operandi | Creating convincing YouTube tutorials and help articles that promoted “free” tools, which were actually installers for subscription traps and spyware. |
| Status | Subject to international warrants; platforms have banned associated accounts, but networks persist under new aliases. |
Nxxxxs’s strategy was insidiously simple: create content that looked like legitimate tech support or software reviews, embed links to download files like AacAmbientlighting.exe, and rely on users not reading the dense, deceptive End-User License Agreements (EULAs). The scandal highlights a brutal truth: the most dangerous threats often wear the mask of helpfulness. Now, let’s break down exactly how these traps were set and, more importantly, how you can dismantle your own vulnerabilities.
Decoding the Trap: The Anatomy of a “Short-Term Agreement” Scam
The term “short-term agreement” in the Nxxxxs context is a misnomer. These were not legitimate, time-limited trials. They were legally binding contracts, buried in pages of text, that enrolled users in expensive monthly subscriptions with difficult cancellation processes. The scam worked in three phases:
- The Bait: A compelling YouTube video or comment would promise a “free premium feature” for YouTube, a “system optimization tool,” or “exclusive access” to content. The call-to-action always involved clicking a link to download a
.exefile or signing up on a third-party website. - The Switch: The downloaded file, often named something innocuous like
AacAmbientlighting.exe(a real example from the scandal), would install a legitimate-looking program but also silently enroll the user in subscription services via “partner offers” checked by default in the installer. Alternatively, the sign-up website would present a checkbox agreement that, if unchecked, prevented the “free” service from working—a dark pattern designed to trick users into consent. - The Hook: Once the agreement was “signed” electronically, the user’s payment method (often a saved card from their Google/YouTube account) was authorized. Small “verification” fees would appear, followed by recurring monthly charges. Canceling required navigating a maze of automated phone systems and hidden web forms, with many victims reporting charges for months after believing they’d canceled.
The critical lesson here is that digital agreements are legally enforceable contracts. You must treat every checkbox and “I Agree” button with the same scrutiny you would a physical document signed in pen. But how do you even know where to look for these deceptive agreements on the platforms you trust? That’s where mastering your account settings becomes your first line of defense.
- Votre Guide Complet Des Locations De Vacances Avec Airbnb Des Appartements Parisiens Aux Maisons Marseillaises
- Shocking Gay Pics From Xnxx Exposed Nude Photos You Cant Unsee
- Exxonmobil Beaumont Careers Leaked The Scandalous Truth They Cant Hide
Your Command Center: Navigating YouTube and Google Account Settings
Your account settings are the control panel for your digital identity. The Nxxxxs scandal often began with users being directed away from official settings pages to fraudulent ones. Always ensure you are on the legitimate google.com or youtube.com domain before entering credentials or adjusting settings.
Finding the Essentials: The Profile & Settings Menu
The first step to regaining control is knowing where the controls are. As noted in the key points, you access your core account menu in two primary ways:
- Via the Profile Picture: In the top right corner of any YouTube or Google page, you’ll see your profile picture or initials. Clicking this icon opens a dropdown menu. This is your gateway.
- Via Your Channel Name: On your YouTube channel page, clicking your channel name in the top bar also leads to account management options.
From this menu, you can access “Settings” (often represented by a gear icon ⚙️) or “Manage your Google Account.” This is where you must regularly audit:
- Connected Apps & Sites: Revoke access to any third-party applications you don’t recognize or no longer use. This is a common entry point for scammers.
- Payment Methods & Subscriptions: Review all saved credit cards and active subscriptions. Look for unfamiliar merchants like “Nxxxxs Services LLC” or cryptic billing descriptors.
- Security: Check your recent security activity, recovery options, and signed-in devices.
The Watch History: A Log of Your Digital Footprint
Your watch history is more than a convenience feature; it’s a forensic log. As stated, “History videos that you've recently watched can be found” under the “History” section in the left sidebar of YouTube. Regularly review this list. Do you see videos you never watched, particularly from obscure channels promising “secret features” or “hacks”? This could be a sign your account was compromised or that you inadvertently clicked a malicious ad. Clear your watch history periodically and use “Incognito Mode” for sensitive searches.
The Ultimate Resource: The Official YouTube Help Center
When in doubt, go to the source. The Official YouTube Help Center (support.google.com/youtube/) is your most reliable source for accurate information. As the key sentences state (in both English and Arabic), it’s where you can find tips, tutorials, and answers to frequently asked questions. Never trust random blogs or YouTube comments for official procedures. Scammers like those behind the Nxxxxs scheme create fake “help” sites that mimic the real thing to steal login credentials or push malware. Always double-check the URL.
The Malware Mirage: Understanding the AacAmbientlighting.exe Example
The Chinese sentence in the key points provides a perfect case study: “要关注的重点是上图中绿色方框标记的软件,是否题主所需要运行的。 假如,我是说假如,这个文件名“AacAmbientlighting.exe”的软件确实是题主所需要运行的软件的话,那么就需要按照蓝色方框中标记.” Translated, it means: “The focus is on the software marked by the green box in the figure above, whether it is the software the questioner needs to run. If, I say if, the software with the filename ‘AacAmbientlighting.exe’ is indeed the software the questioner needs to run, then you need to follow the blue box.”
This is classic social engineering. The filename AacAmbientlighting.exe sounds technical and specific—perhaps related to audio drivers or screen calibration. It’s designed to sound legitimate to a non-technical user. The “green box” and “blue box” reference suggests a tutorial video where the narrator points to on-screen elements, creating a false sense of authority and step-by-step guidance.
Here is the actionable protocol this scenario teaches you:
- Pause and Research: Before running any downloaded
.exefile, search its exact filename online. Add “virus” or “scam” to your search. Legitimate software will have clear, reputable download sources and community discussions. - Verify the Source: Was the download link from the official website of the software vendor, or from a link in a YouTube video description or comment? The latter is a massive red flag.
- Check Digital Signatures: Right-click the file on your computer, go to “Properties,” and check the “Digital Signatures” tab. Does it come from a known company like Microsoft, Adobe, or a reputable developer? A missing or unknown signature is dangerous.
- Use a Sandbox or Scanner: If you must test unknown software, do so in a virtual machine or upload the file to a multi-scanner service like VirusTotal.com first.
The Nxxxxs scandal distributed hundreds of such files, each with a convincing name and story. If a “free tool” requires you to disable your antivirus to install it, you are being hacked. Period.
Fortifying Your Financial Front: Trials, Authorizations, and Charges
The scam often extended to financial theft through unauthorized charges. The key sentences about YouTube TV trials illustrate a common legitimate process that scammers mimic.
“When you start your trial, YouTube TV will authorize your credit card with a small fee. Your financial institution will get an authorization request from us, and the fee will be reflected in your account.”
This is a standard pre-authorization hold to verify the card is valid and has funds. The small fee (often $1) is temporary and drops off within a few days. Scammers exploit this knowledge. They might set up a fake “free trial” for a non-existent service, run the same authorization, and then either:
- Convert the hold into a full, large monthly charge.
- Use the verified card details to run up charges elsewhere.
- Make the cancellation process impossible, locking you into a recurring payment.
Your Action Plan:
- Use Dedicated Cards: For free trials, consider using a prepaid debit card with a limited balance or a virtual card number from your bank (if offered).
- Monitor Closely: Check your bank statements daily during any trial period. Look for unfamiliar merchants and small, unexplained holds.
- Cancel Proactively: Don’t wait for the trial to end. Cancel the subscription immediately after signing up if you decide you don’t want it, while the process is fresh in your mind.
The Critical First Step: Mastering Gmail Sign-Out
One of the simplest yet most overlooked security practices is properly signing out of your Google accounts, especially on shared or public devices. The Nxxxxs operation sometimes relied on users leaving accounts logged in on compromised machines.
The process is straightforward but varies slightly by device:
- From your device, go to the Google Account sign-in page (
accounts.google.com/signin). - If you’re already signed in, you’ll see your profile picture. Click it.
- Select “Sign out” from the dropdown menu.
On mobile apps, the sign-out option is typically found in the app’s settings menu under your profile. Make it a habit to sign out completely, not just close the tab or app. For shared family computers, consider using separate browser profiles or, even better, a dedicated browser for sensitive accounts that you always sign out of.
Building a Habit of Security: A Proactive Checklist
Turning this knowledge into instinct requires a routine. Integrate these checks into your monthly digital hygiene:
- Weekly: Scan your YouTube and Google account security settings. Review connected apps and recent logins.
- Monthly: Check bank and credit card statements for unfamiliar subscriptions or small holds. Review your YouTube watch history for unknown videos.
- Always: Before downloading any file or clicking a link promising “free” features:
- Hover over links to see the true URL.
- Search the software name + “scam” or “review.”
- Ask yourself: “Is this too good to be true?”
- Download Wisely: Only get the YouTube app and YouTube Music app from the official Google Play Store or Apple App Store. These official apps provide a richer, safer viewing experience and receive automatic security updates. Avoid third-party app stores or direct
.apk/.ipafiles.
Conclusion: Your Awareness is the Ultimate Antivirus
The Nxxxxs short-term agreement scandal is not a unique anomaly; it is a symptom of a vast ecosystem of digital predation that preys on convenience, curiosity, and complacency. The techniques used—deceptive agreements, malware disguised as utilities, and the exploitation of legitimate platform features like free trials—are constantly evolving. However, the defense remains rooted in fundamental principles: vigilance, verification, and mastery of your own digital tools.
You now hold the keys. You know where your account settings are, how to interpret authorization fees, how to scrutinize a downloaded file, and where to find the official help center. The next time you see a video promising a “secret hack” or a “free premium upgrade,” you will see the red flags for what they are: potential traps. The most powerful tool in your cybersecurity arsenal is not an expensive antivirus suite, but an informed and skeptical mind. Don’t just click “I Agree.” Read. Question. Verify. Your digital life—and your financial security—depends on it.