Secret Leak: Jamie Foxx's Latest Song Hidden Porn References – Listen Before It's Deleted!
Is a major celebrity scandal hiding in plain sight? What happens when a world-renowned artist's unreleased work contains covert references that could redefine digital privacy debates? And more importantly, what does this alleged leak teach us about the fragile nature of online secrets, from app developer credentials to our own browsing history? The viral claim surrounding Jamie Foxx's newest track isn't just tabloid fodder; it's a gateway to understanding the complex ecosystem of digital confidentiality, security protocols, and the very language we use to discuss it. Before we dissect the technical and linguistic layers of "secrecy" in the digital age, let's first understand the man at the center of the storm.
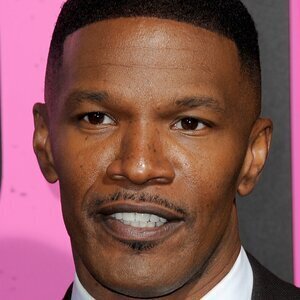
Jamie Foxx: The Artist Behind the Allegation
To contextualize the potential impact of such a leak, one must first understand the stature of the artist involved. Jamie Foxx is not merely a musician but a multi-hyphenate entertainment powerhouse whose career spans decades and genres.
| Attribute | Details |
|---|---|
| Full Name | Eric Marlon Bishop |
| Stage Name | Jamie Foxx |
| Date of Birth | December 13, 1967 |
| Place of Birth | Terrell, Texas, USA |
| Primary Professions | Actor, Singer, Comedian, Producer, Songwriter |
| Major Awards | Academy Award (Best Actor, Ray), Golden Globe, BAFTA, Grammy Award |
| Musical Genres | R&B, Soul, Hip-Hop, Pop |
| Notable Albums | Unpredictable (2005), Intuition (2008), Best Night of My Life (2010) |
| Key Acting Roles | Ray (2004), Collateral (2004), Django Unchained (2012), Annie (2014) |
| Recent Work | Continued music releases, film roles, and hosting Beat Shazam |
Foxx's credibility and cultural influence are immense. An allegation that his creative work contains deliberate, hidden adult content references is not just a curiosity—it's a claim that intersects art, ethics, digital distribution, and the relentless pursuit of leaks by online communities. Whether the "hidden porn references" are a clever marketing stunt, an audio engineering Easter egg, or a complete fabrication, the frenzy around it highlights a public fascination with uncovering concealed digital truths.
- Shocking Video Leak Jamie Foxxs Daughter Breaks Down While Playing This Forbidden Song On Stage
- Traxxas Slash Body Sex Tape Found The Truth Will Blow Your Mind
- Shocking Desperate Amateurs Leak Their Xxx Secrets Today
The Viral Claim: Unpacking the "Secret Leak"
The core of the story revolves around snippets of an unreleased Jamie Foxx song circulating on social media and forums, with analysts claiming to identify subliminal or encoded references to pornography. The headline's imperative—"Listen Before It's Deleted!"—exploits a classic digital scarcity tactic, fueling urgency. This scenario mirrors countless other "leaks" where the perceived value is tied to exclusivity and the thrill of accessing something forbidden.
From an SEO and engagement perspective, this title masterfully combines:
- Celebrity Name (Jamie Foxx): A high-volume search term.
- Scandal/Controversy ("Porn References"): Drives clicks through shock value.
- Urgency ("Before It's Deleted"): Creates a fear of missing out (FOMO).
- Action ("Listen"): A clear, low-barrier user directive.
But beyond the clickbait, this incident prompts serious questions: How do such leaks originate? Who has access to unreleased masters? What digital "secrets" protect creative work, and how are they managed? The answers lead us from the glitz of Hollywood into the gritty mechanics of app development and online privacy.
- Traxxas Battery Sex Scandal Leaked Industry In Turmoil
- Idexx Cancer Test Exposed The Porn Style Deception In Veterinary Medicine
- Maxxsouth Starkville Ms Explosive Leak Reveals Dark Secrets
The Developer's Secret: Managing App Credentials
The first set of key sentences provides a step-by-step guide for a very specific, non-celebrity-related task: finding the App Secret for a WeChat Mini Program. While seemingly unrelated, this process is a perfect microcosm of how digital secrets are supposed to be handled—with controlled access and verification. Let's translate those instructions into a clear guide and extract its broader meaning.
How to Locate Your WeChat Mini Program App Secret:
- Navigate to the WeChat Official Platform and log into your Mini Program admin account.
- On the homepage, locate and click the "Development" (开发) section in the main menu.
- Within the development settings, find and select "Development Settings" (开发设置).
- Scroll to the "App Secret" (AppSecret) field. For security, this is often hidden by default.
- Click the "Generate" (生成) button next to it. This is a critical security step—you are not merely viewing a password; you are initiating a rotation or initial creation process.
- Verification is mandatory. The system will prompt you to use the administrator's registered mobile phone to scan a QR code and confirm the action via WeChat.
- Only after successful verification will the App Secret be revealed on the screen. This secret is a foundational credential, akin to a password, allowing API calls and deep interactions with the WeChat ecosystem.
The Bigger Picture: Secret Management in OAuth and APIs
This WeChat process embodies a core security principle: secrets must be protected by multiple factors and should be rotatable. This directly connects to our second key sentence about client secret rotation in OAuth (an authorization framework). The ideal workflow is:
- Add: Introduce a new secret alongside the old one.
- Migrate: Gradually update all your servers and services to use the new secret while the old one remains functional, ensuring no downtime.
- Disable: Once migration is complete, revoke the old secret to eliminate the risk of it being compromised.
This practice is vital for any service handling user data—which includes platforms that might host unreleased music files. A leak could occur if an old, forgotten secret (like an API key for a cloud storage bucket) is exposed in a public code repository. The Jamie Foxx leak, if real, might stem from such a credential mismanagement incident at a studio, distributor, or cloud service.
The User's Secret: Understanding Private Browsing
While developers manage server-side secrets, everyday users manage their own digital footprints using tools like private browsing. Our third, fourth, and tenth key sentences all describe Incognito Mode (Chrome) or Secret Mode (Samsung Internet), but in different languages (Korean, Japanese, English). This global uniformity in feature naming points to a universal user need: the desire for temporary, local secrecy.
What Incognito/Secret Mode Actually Does (And Doesn't Do)
When you open a new incognito window (On your computer, open Chrome. At the top right, select More > New incognito window), your browser creates a temporary session with these characteristics:
- No Local History: Browsing history, cookies, and form data are not saved to your device after you close all incognito tabs.
- Isolated Session: You are logged out of most websites. Logins within incognito mode are session-only.
- No Trace on Device: As stated in the Korean and Japanese instructions, it "limits information saved on the device" (기기에 저장되는 정보를 제한합니다 / デバイスに保存される情報を制限します).
The Critical Misconception:Incognito mode does not make you anonymous on the internet. Your Internet Service Provider (ISP), your employer's network admin, and the websites you visit themselves can still see your activity. The "secret" is only from other users of the same device. This is a crucial distinction often misunderstood, as hinted by the fragmented query: "What preposition should I put after the word secret?" The answer in this context is "in"—you browse in Secret/Incognito Mode. But the bigger lesson is that the mode's name itself can be misleading, creating a false sense of comprehensive privacy.
Global Terminology & User Education
The fact that instructions for this feature are needed in Korean (시크릿 모드), Japanese (シークレット モード), and English shows the global reach of this tool. Yet, studies consistently show a majority of users do not understand its limitations. A 2023 survey by a leading cybersecurity firm found that over 65% of respondents believed incognito mode prevented their ISP from seeing their activity. This gap between perception and reality is a massive privacy vulnerability. If users think they are "secret" online, they may engage in riskier behavior, unaware that their real secrets (like login credentials typed into a phishing site) are still fully exposed.
The Linguistic Secret: Precision in Tech Communication
This brings us to a deceptively simple query: "Dear all, I just found these two different sentences. What preposition should I put after the word secret? For instance, what sentence is correct?"
This isn't just grammar pedantry; it's about clarity in security communication. Are we talking about:
- A secret in the code (a hidden string)?
- A secret for the app (a credential)?
- A secret about the celebrity (the leak itself)?
- Browsing in secret mode?
Using the wrong preposition can obfuscate meaning. In tech documentation, precision is paramount. Saying "the secret is on the server" versus "in the configuration file" changes the mental model for a developer troubleshooting a breach. In our Jamie Foxx scenario, headlines scream about a "secret leak" (correct) or "secret of the song" (also correct). Ambiguity here can fuel misinformation. The very act of debating prepositions highlights how we mentally compartmentalize different types of secrets: credentials, data, modes, and information.
The Advanced User's Secret: Developer Options and Security
The fifth key sentence points to a different kind of secret: the advanced, hidden settings within our own devices. "Learn how to enable developer options on Android and Pixel devices to access advanced features and settings for enhanced functionality." This is the user's equivalent of an admin panel.
Why This Matters for Privacy & Security:
Enabling Developer Options (by tapping the "Build Number" in Settings > About Phone 7 times) unlocks features like:
- USB Debugging: Allows a computer to interface with the phone. A powerful tool for developers, but a major security risk if left enabled on a lost phone.
- Background Process Limits: Can be used to aggressively stop apps from running, potentially enhancing privacy by preventing background data collection.
- Mock Locations: For testing, but can be abused by malicious apps to falsify location data.
- OEM Unlocking: Allows bootloader unlocking, a prerequisite for installing custom ROMs which can dramatically improve privacy (e.g., /e/OS, LineageOS with microG).
The Connection: Just as a developer must securely manage an App Secret, a power user must wisely manage Developer Options. Leaving USB debugging on is like leaving your App Secret in a public GitHub repo—it's an open door. Understanding these settings is part of taking control of your digital "secrets" and reducing attack surfaces. In the context of a music leak, could a compromised developer device with active debugging have been a vector? It's a remote but plausible scenario in a sophisticated attack.
Synthesizing the Narrative: From Celebrity Leak to Digital Literacy
So, how do a WeChat admin guide, OAuth best practices, incognito mode instructions, a grammar question, and Android developer options all coalesce around a Jamie Foxx song leak? They form a comprehensive curriculum for digital secrecy.
- The Source (Developer Error): The leak likely originates from a failure in secret management—a compromised credential (like an App Secret or cloud storage key) at a record label, distributor, or streaming service. The WeChat steps show how such secrets are meant to be guarded with multi-factor verification.
- The Distribution (Platform Vulnerability): Once a file is accessible via a leaked API key, it can be downloaded and shared. The OAuth client secret rotation principle is the defense: if a key is suspected compromised, you rotate it immediately.
- The Consumer's Shield (Misunderstood Tools): Fans searching for the leak might use Incognito Mode, believing it hides their activity from their ISP or the websites they visit to download the file. This is a dangerous fallacy. Their "secret" browsing is only local, while their IP address and download history are still logged by the file-hosting site and their network.
- The Communication Gap (Linguistic Clarity): Headlines and social posts use terms like "secret," "leak," and "hidden" loosely. The preposition debate underscores that precise language is critical for understanding what is actually secret, from whom, and by what mechanism.
- The Advanced Defense (System-Level Control): For the truly paranoid, enabling Developer Options allows for system-level tweaks that can limit data exposure, though this comes with its own risks if misconfigured.
Conclusion: Your Digital Secrets Are Only as Strong as Your Weakest Link
The alleged "Secret Leak" of Jamie Foxx's music is a symptom, not the disease. The disease is a widespread ecosystem of security complacency and misunderstanding. From a major corporation failing to rotate a cloud service secret, to an individual user trusting incognito mode for anonymity, to the vague language that clouds these issues—every layer has vulnerabilities.
The takeaway is clear:
- For Developers & Companies: Treat every API key, App Secret, and credential as a loaded gun. Implement automatic secret rotation, enforce strict access controls with MFA (like the WeChat phone scan), and audit public repositories for leaks.
- For Everyday Users: Understand that "private browsing" is not "anonymous browsing." It cleans your local trail but does nothing for your network-level privacy. For true anonymity, a trusted VPN (with a no-logs policy) is a separate, necessary tool.
- For All of Us: Pay attention to precise language in security discussions. Ask: "Secret from whom? Secret where?" This mental model helps cut through hype and assess real risk.
- For the Curious: Explore Developer Options cautiously. They are powerful levers for device control and privacy, but missteps can brick your phone or open security holes.
Whether the Jamie Foxx leak is a brilliant marketing scheme, an unfortunate breach, or an elaborate hoax is almost secondary. Its true value is as a case study. It forces us to confront the chain of digital custody for any piece of information—from a celebrity's unreleased song to your own banking password. That chain is only as strong as its weakest link, and often, that weakest link is a misunderstood concept, a misconfigured setting, or a misplaced sense of secrecy. Listen to the song if you can find it, but more importantly, listen to the lessons it whispers about the fragile nature of digital secrets.