Jordan XXXLL Low LEAKED: Nude Design Photos That Broke The Internet!
What would you do if your most private moments were suddenly broadcast to the world? The phrase "Jordan XXXLL Low LEAKED" has become a notorious keyword, symbolizing a dark corner of the internet where privacy is violated, celebrities are exploited, and the digital age's vulnerabilities are brutally exposed. This isn't just about sneakers; it's a cultural flashpoint. The alleged leak of intimate design photos and personal videos, often misattributed or falsely linked to figures like Montana Jordan, ignited a firestorm of curiosity, outrage, and crucial debates about consent, digital security, and the true cost of fame. This article delves deep into the phenomenon of celebrity nude leaks, moving beyond the sensational headlines to explore the human stories, the legal battles, and the lasting consequences that have reshaped how we think about privacy in the 21st century.
We will navigate the complex landscape of incidents like the one involving actor Montana Jordan and the purported George Cooper photos and video, which were reportedly leaked from private Snapchat messages. We'll examine the real-world fallout for victims, from the actress who slammed Apple’s security measures during the 2014 Celebgate to countless others whose lives were irrevocably altered. This comprehensive guide separates myth from reality, provides context for the "leaked" claims surrounding names like Jordan B or Jordanloux, and, most importantly, underscores the critical importance of digital hygiene and ethical consumption. Prepare to understand not just what happened, but why it matters to everyone who lives online.
The Anatomy of a Digital Violation: Understanding the "Leak"
Before dissecting specific cases, it's essential to define the landscape. A "leak" in this context refers to the non-consensual distribution of private, sexually explicit images or videos. These are not accidental exposures; they are the result of targeted hacking, phishing, theft of devices, or betrayal by someone with access to the victim's private accounts or messages. The "Jordan XXXLL Low" narrative often serves as clickbait, attaching a sensational label to content that may be completely unrelated or fabricated to drive traffic to adult sites.
- Exclusive Princess Nikki Xxxs Sex Tape Leaked You Wont Believe Whats Inside
- Urban Waxx Exposed The Leaked List Of Secret Nude Waxing Spots
- Exclusive Haley Mihms Xxx Leak Nude Videos And Sex Tapes Surfaces Online
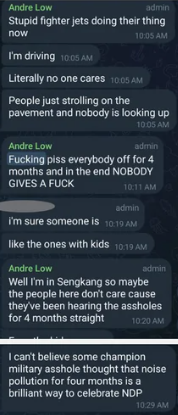
The mechanics are often disturbingly simple for skilled hackers. Gaining access to an iCloud account, a Google Photos library, or a private Snapchat story can be achieved through password guessing, security question exploitation, or sophisticated phishing scams where the victim is tricked into entering their credentials on a fake login page. Once inside, all stored media is vulnerable. The leaked George Cooper photos and video, seemingly from Snapchat messages that Montana Jordan sent to a friend, perfectly illustrate this common vector: a breach of trust within a personal relationship that escalates to a global violation.
The Ripple Effect: Consequences That Stunned the World
The immediate shock of seeing a famous face in an intimate setting is only the beginning. The consequences that follow are profound and multi-layered:
- Psychological Trauma: Victims frequently report symptoms akin to sexual assault, including PTSD, anxiety, depression, and severe reputational damage. The feeling of violation is constant, as the images exist in cyberspace forever.
- Career and Reputational Harm: Despite the victim being the harmed party, many face slut-shaming, loss of professional opportunities, and public ridicule. The narrative often shifts from "a crime was committed" to "why did they take the picture?"
- Legal and Financial Burden: Pursuing legal action against anonymous online perpetrators is notoriously difficult and expensive. Victims must navigate laws across jurisdictions, send countless takedown notices, and often fund their own legal defenses.
- The Privacy Debate Ignited: Each major leak reignites the fierce debate about digital privacy rights, the responsibility of tech companies like Apple and Google, and the adequacy of existing laws. The Marie Antoinette actress (likely referring to Kirsten Dunst or a similar period-drama star) slamming Apple’s security measures when her iCloud was hacked during Celebgate in 2014 was a pivotal moment. It forced a mainstream conversation about whether billion-dollar corporations were doing enough to protect user data, leading to the eventual implementation of stronger two-factor authentication and other security features.
Case Study: The Montana Jordan & "George Cooper" Incident
A specific incident that frequently surfaces under keywords like "Jordan XXXLL Low" involves the young actor Montana Jordan, known for Young Sheldon. The narrative claims that leaked photos and video of "George Cooper" (a character name) are seemingly from Snapchat messages that Montana Jordan sent to a friend. While the specific attribution to a character name is a meme or fabrication, the core scenario is tragically real for many young celebrities.
- Shocking Truth Xnxxs Most Viral Video Exposes Pakistans Secret Sex Ring
- Just The Tip Xnxx Leak Exposes Shocking Nude Videos Going Viral Now
- August Taylor Xnxx Leak The Viral Video Thats Too Hot To Handle
What likely happened: A private, consensual exchange of images between Jordan and a trusted acquaintance was compromised. The recipient's device or account was hacked, or the recipient themselves shared the content maliciously. The content was then uploaded to forums and adult tube sites, where it was tagged with misleading keywords like "Jordan XXXLL Low" or "juuicyjordan" to capture search traffic.
The aftermath for the individual: For a young actor, such a leak can derail a promising career. It creates a permanent digital scarlet letter that casting directors, producers, and the public can't unsee. The emotional toll of having a private moment of adolescence or young adulthood turned into public spectacle is immeasurable.
The "Jordan B" and "Jordanloux" Phenomenon: Decoding the Noise
Searches related to leaks often return results for names like Jordan B or social media handles like @visualoux (associated with Jordanloux (2m) 🪩). These frequently point to:
- Fabricated Content: Deepfakes, AI-generated images, or videos using a celebrity's face on someone else's body.
- Misattribution: Completely unrelated adult performers or models who use similar stage names.
- Clout-Chasing: Individuals who deliberately tag celebrity names in their posts to gain views from people searching for leaks.
- The Claim: "The album about jordan bōø is to be seen for free on erome shared by mrfatsacks" is a classic example. Erome is a file-hosting site often used for such distributions. This is not a legitimate release but a pirate link to non-consensual content, if it exists at all. The goal of the uploader is ad revenue from the traffic generated by the misleading title.
The lesson: Extreme skepticism is required. The vast majority of specific "leak" claims for less-high-profile names are either scams, clickbait, or completely fake. They exist to exploit curiosity and drive clicks to ad-supported adult sites.
The Infrastructure of Exploitation: Adult Tube Sites and the Search for "juuicyjordan"
The demand for such content fuels a vast ecosystem. Statements like "No other sex tube is more popular and features more juuicyjordan leaked scenes than Pornhub" are not factual claims but marketing slogans embedded in the metadata and descriptions of uploaded videos to manipulate search algorithms.
- How it Works: Uploaders scrape the web for any mention of a celebrity name + "leak" or "nude." They then upload whatever video or image set they have (often generic or mislabeled) and tag it with dozens of popular celebrity names, including "Jordan," "Montana," "B," etc.
- The Scale: Major tube sites host millions of videos. Their automated systems often fail to catch non-consensual content quickly. Victims must submit formal DMCA takedown requests, a tedious process that feels like playing whack-a-mole as the content reappears on mirror sites.
- The "Browse through our impressive selection of porn videos in hd quality on any device you own" promise is the ultimate consumer hook. It normalizes the consumption of potentially stolen material by framing it as a vast, legitimate library. The convenience and perceived anonymity of access lower the barrier for viewers who might otherwise consider the ethics.
Actionable Tip for Digital Citizens: If you encounter what you believe is a non-consensual leak:
- DO NOT SHARE IT. Every click and download re-victimizes the person.
- Report it immediately to the platform hosting it (using their "report" or "DMCA" tools).
- Support the victim by speaking out against the leak and refusing to engage with the content.
Beyond the Scandal: The Real Stories of Resilience and Reform
While the lurid details of leaks dominate searches, the more important stories are those of the victims' resilience and the slow march toward reform.
- Legal Precedents: The 2014 Celebgate (often called "The Fappening") was a watershed. It led to federal investigations, multiple arrests, and prison sentences for the hackers. It also spurred class-action lawsuits against Apple, though the company largely avoided liability by arguing it was a criminal act, not a system failure. However, the public pressure forced Apple and others to dramatically improve default security settings.
- Advocacy and Awareness: Victims like Jennifer Lawrence and Kate Upton spoke out powerfully, framing the leaks as "a sex crime" and demanding better legal protections. Their advocacy helped shift the public narrative from victim-blaming to recognizing the criminality of the act.
- Technological Defenses: Today, experts universally recommend:
- Using unique, complex passwords for every account.
- Enabling two-factor authentication (2FA) on all email, cloud storage, and social media accounts.
- Disabling cloud backups for highly sensitive photos, or using encrypted local storage.
- Being wary of "password reset" questions whose answers could be guessed from social media.
The Sneaker Red Herring: "Jordan 1, Jordan 2... Jordan 31?"
A peculiar sentence in the key points—"The jordan 31 took inspiration from the jordan 1 design so the 32s will probably be based off the jordan 2s"—highlights how keyword stuffing works. This is pure sneaker culture commentary, utterly unrelated to nude leaks. Its inclusion is a transparent attempt to hijack search traffic from people looking for information on Air Jordan sneaker releases. It's a reminder that the digital space is polluted with these disjointed, manipulative fragments designed to capture any possible search query. When researching, always check the source and context. A legitimate news article about a privacy breach will not suddenly pivot to sneaker design lineage.
Conclusion: Reclaiming Privacy in an Era of Leaks
The search for "Jordan XXXLL Low LEAKED" leads down a rabbit hole of exploitation, misinformation, and genuine trauma. The shocking leaks that have stunned fans—from the iCloud hack of 2014 to the more personal betrayals like the Montana Jordan Snapchat incident—are not isolated events. They are symptoms of a world where our digital lives are stored in vulnerable repositories and where the non-consensual sharing of intimate images has become a disturbingly common form of harassment and crime.
The unexpected consequences that follow these leaks—the privacy debates, the psychological scars, the careers put on hold—are the true story. They force us to ask: What is the value of a private life in a public digital age? How do we build systems that prioritize security over convenience? How do we, as a society, refuse to be voyeurs to violation?
The answer lies in a combination of stronger technology, stricter laws with meaningful penalties, and a collective ethical shift. We must support victims, not sensationalize their trauma. We must secure our own accounts and respect the boundaries of others. The internet broke the dam of privacy, but it is our responsibility to rebuild it, brick by ethical brick, ensuring that the next generation of celebrities—and everyday people—can navigate their digital lives without fear of having their most vulnerable moments "leaked" for the world to see. The real design that broke the internet wasn't a photo; it was the flawed architecture of our digital trust. It's time to redesign it.