SHOCKING: How Doxxing Exposes Your Nude Photos And Personal Info In Seconds!
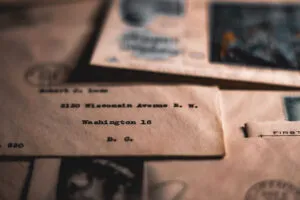
Have you ever felt a cold sweat, realizing that a private photo or a sensitive piece of personal information might be floating in the digital ether, accessible to anyone with malicious intent? The term doxxing—the act of researching and broadcasting someone's private, personally identifiable information without consent—has evolved from a niche internet threat into a devastatingly common weapon. In mere seconds, a hacker can weaponize your own digital footprint, exposing your home address, phone number, financial details, or intimate images to the world. But what if the first clues of this invasion aren't a public shaming post, but something far more mundane and easily overlooked in your own inbox? What if the silent signs are missing sent emails, bizarre timestamps, or photos you sent that vanish without a trace? This guide isn't just about email troubleshooting; it's a critical frontline defense. We'll use common Gmail frustrations as a detective's toolkit to uncover potential security breaches and, most importantly, arm you with the knowledge to lock down your digital life before the unthinkable happens.
Understanding the Gateway: Your Email as a Doxxing Target
Your email account is the master key to your digital identity. It’s the username for countless services, the repository for password resets, and the archive of your private communications. For a doxxer, compromising this single account is a goldmine. Once inside, they can:
- Scrape your contact list for further targets.
- Search your sent folder for sensitive documents or photos you've shared.
- Use your account to send phishing emails to your contacts, expanding their reach.
- Gather personal details from old correspondence (addresses, birthdays, employer names).
The unsettling reality is that many people only discover their account has been compromised after their information has been leaked. However, subtle anomalies in your email behavior can be the early warning system. Let's decode these signals, starting with the most common complaint: the mysterious case of the missing Sent Mail.
- Nude Burger Buns Exposed How Xxl Buns Are Causing A Global Craze
- Leaked Sexyy Reds Concert Nude Scandal That Broke The Internet
- Exposed How West Coast Candle Co And Tj Maxx Hid This Nasty Truth From You Its Disgusting
The Vanishing Act: Why Your "Sent" Folder Might Be Empty
Learn how to view sent and received emails in your google account with this helpful guide. This fundamental skill is your first step in forensic self-audit. Normally, every email you send is automatically saved in the "Sent" folder. But if you open Gmail and that folder is empty or missing, it’s a major red flag. Before assuming a technical glitch, consider the security implications.
Step 1: Confirm the Folder's Existence
If you don't see sent in the left column, scroll down and click on more to see if it shows up. Gmail's interface can hide less-used labels. Click "More" to expand the full list. If "Sent" or "Sent Mail" is there but not visible in the main sidebar, that's a configuration issue, not necessarily a security breach. However, if the folder itself is missing from the "More" list, that's highly unusual.
Step 2: Restore a Missing Label
If so, you can make it visible by dragging it up or through the label settings. To make a hidden label permanently visible:
- My Mom Sent Porn On Xnxx Family Secret Exposed
- Sasha Foxx Tickle Feet Leak The Secret Video That Broke The Internet
- Channing Tatums Magic Mike Xxl Leak What They Never Showed You
- Hover over the label name in the "More" section.
- Click the three vertical dots that appear.
- Select "Label settings."
- Ensure the checkbox for "Show in label list" is ticked.
You can also simply drag the label from the "More" section up into the main navigation pane.
But what if the folder is truly gone, or its contents are mysteriously empty? This could indicate that a malicious actor, after gaining access to your account, deliberately deleted your sent emails to cover their tracks. They don't want you to see the phishing emails they sent from your account or the sensitive data they harvested from your outbox.
The Time Traveler Emails: A Chilling Symptom
Sent emails from years ago reappearing as recently sent i have loads of emails in my sent folder that i sent years ago showing as sent last week. This is one of the most bizarre and telling signs of account compromise. Gmail's timestamp is reliable. If you see an email you know you sent in 2018 suddenly showing a "Sent" date of last week, it means someone (or something) is accessing your account and triggering a re-send or a sync event that updates the metadata.
People are not actually receiving them again. This is crucial. The emails aren't being delivered to the recipients anew; the record in your Sent folder is being altered or a new copy is being created with a forged timestamp. This is a hacker's fingerprint. They might be using your account to send spam or phishing emails and are inadvertently (or deliberately) messing with your email history as they access your account from different devices or locations.
I sent an important business email this afternoon (~5pm, 2/28). While checking for a reply this evening at 11pm, i noticed that it says it was sent tomorrow at 12:35am. This specific scenario points to a severe timezone or server manipulation issue, often caused by malware on your device or a compromised account being accessed through a proxy server in a different part of the world. Your local time is being overridden by the attacker's server time. This is not a Gmail bug; this is a breach.
The Global Perspective: It's Not Just Gmail
The methods to access your sent emails may alter slightly if you are using a different email provider, but in most situations, you should be able to locate a sent or sent items folder that contains all the. Whether you use Outlook, Yahoo, or Apple Mail, the "Sent Items" or "Outbox" is a standard feature. Its absence or manipulation is a universal red flag. The core principle remains: your sent folder is a log of your digital activity. If that log is tampered with, someone is walking in your digital footsteps.
The Panic and the Puzzle: Common User Questions
The confusion and fear following these discoveries lead to a chorus of urgent questions that paint a clear picture of vulnerability:
- Why have all of my sent emails disappeared? As discussed, potential causes range from accidental deletion and filter misconfiguration to malicious deletion by an intruder.
- The latest is 2019, so i am unsure if my emails are actually sending. If your Sent folder hasn't recorded anything since 2019, it strongly suggests your account has been inaccessible to you for that long, likely due to a password change you didn't authorize or a session being hijacked.
- I don't see my sent emails in my sent emails. Where could they be going? They could be in a custom label you never created (hackers sometimes move emails), permanently deleted (by you or an attacker), or the attacker is using a different interface (like POP/IMAP) that doesn't sync labels correctly to your web view.
- Someone sent photos in one of my emails i seen the pictures but i can't get back to them. This is critical. If you received an email with attachments, viewed it, and now the email or the attachments are gone, it could mean the sender deleted the email from their side (which can sometimes remove it from your view if using certain protocols) or, more worryingly, your account was accessed and that specific email was targeted for deletion because it contained the very evidence—the photos—that a doxxer wants to hide or steal for their own use.
The Data Harvest: How Your Photos and Info Become Public
We would like to show you a description here but the site won’t allow us. This frustrating, generic message you might see on some sites is a small echo of the larger problem: control. When your email is compromised, the attacker has control. They can:
- Download your entire archive, including every photo you've ever sent or received.
- Use your account to send those photos to others, or post them on forums, as a form of blackmail or revenge.
- Extract personal information from email bodies (full names, addresses, phone numbers, SSNs if shared) and compile it into a "dossier."
- Sell this data on dark web marketplaces to other criminals.
As long as you’re the subject of the content, you or your representative can start a request. This refers to legal takedown processes (like under the DMCA for copyright, or GDPR/CCPA for personal data). By the time you're filing these requests, your data may already be cached, copied, and spread across dozens of sites. Prevention is infinitely more effective than cleanup.
The Takedown Nightmare: Fighting Back After the Leak
When you fill out the request form, you’re asked to provide urls for the pages that include your personal. This is the grueling, re-victimizing process of damage control. You must prove ownership of the content and that it was posted without consent. For each instance—and there could be hundreds—you must file a separate request. It's a paperwork nightmare that can take weeks or months, while your intimate life is exposed for the world to see.
Your Action Plan: From Detection to Fortification
Don't just diagnose the problem; solve it. Here is your immediate, step-by-step protocol.
Phase 1: Emergency Account Audit (Do This Now)
- Check Sent Folder & Labels: Follow the steps above. Note any anomalies in dates, missing emails, or unfamiliar labels.
- Review Account Activity: In Gmail, scroll to the bottom right and click "Details" next to "Last account activity." Look for sessions from unfamiliar locations, devices, or browsers. If you see something like "Moscow, Russia" or a city you've never visited, your account is compromised.
- Inspect Forwarding & Filters: Go to Settings > See all settings > Forwarding and POP/IMAP and Filters and Blocked Addresses. Ensure no unknown forwarding address is active and no filters are set to automatically delete or forward your emails.
- Check Connected Apps: Go to Settings > See all settings > Accounts and Import > Grant access to your account and Google Account > Security > Third-party apps with account access. Revoke access to any app you don't recognize.
Phase 2: The Great Purge and Secure Reset
- Change Your Password IMMEDIATELY to a long, unique, and complex one you've never used before. Use a password manager.
- Enable Two-Factor Authentication (2FA). This is non-negotiable. Use an authenticator app (Google Authenticator, Authy) or a physical security key. Do not use SMS-based 2FA if possible, as it can be hijacked.
- Run a Security Checkup: Google provides a dedicated tool (search "Google Account Security Checkup"). Follow every step.
- Scan for Malware: Run a full scan with reputable antivirus/anti-malware software on all your devices. Keyloggers or spyware can steal your new password.
- Recover Missing Emails: Check the "All Mail" label. Also, look in the "Trash" and "Spam" folders. If emails were deleted within the last 30 days, you may be able to restore them. If they are permanently gone, they are likely gone for good—a sign they were deliberately removed.
Phase 3: Long-Term Vigilance and Data Hygiene
- Use Unique Emails for Different Services: Consider a separate email for financial accounts and another for social media/forums. This contains breaches.
- Never Send Highly Sensitive Info via Email: For documents containing SSNs, financial data, or nude photos, use encrypted file-sharing services with password protection and expiration dates. Assume no email is 100% secure.
- Regularly Audit Your Digital Footprint: Google yourself. Set up Google Alerts for your name and key personal details.
- Educate Your Circle: Ensure friends and family know not to click suspicious links in emails from you, as your compromised account will be used to attack them.
Conclusion: Your Inbox is the Canary in the Coal Mine
The strange behavior of your Sent folder—whether it's mysteriously empty, filled with anachronistic emails, or simply not where it should be—is rarely just a "glitch." In the context of today's threat landscape, it is the digital equivalent of a broken window or a pry mark on your door. It's the first, subtle sign that your private space has been violated. Doxxing doesn't always begin with a dramatic hack; it often begins with the quiet theft of your email credentials, followed by a period of silent reconnaissance where an attacker sifts through your sent messages, your contacts, and your attachments.
Don't wait for your nude photos to appear on a public website to take action. The power to protect yourself is in your hands today. By understanding what a healthy email account looks like, you can instantly recognize the symptoms of compromise. Take the audit steps now. Implement the security upgrades—especially two-factor authentication—without delay. Your digital dignity, your personal safety, and your peace of mind depend on treating your email not as a passive tool, but as the critical security perimeter it truly is. The shock of doxxing is real, but the defense starts with a single, empowered click into your account settings. Secure it now, before the next sent email you see is one you never wrote.