The Secret Sex Tapes Of Shawty Bae On OnlyFans Just Leaked! Understanding The Digital Privacy Nightmare
In the hyper-connected world of social media and subscription platforms, a single click can unravel a life. When private, intimate content is shared without consent, it’s not just a scandal—it’s a profound violation with real-world consequences. The recent buzz surrounding "Shawty Bae" and alleged leaked content from platforms like OnlyFans throws a harsh spotlight on a pervasive issue: the non-consensual distribution of private media. But what does this really mean, and what can we learn from it? This isn't just about one viral moment; it's about the fragile state of digital privacy for millions.
The internet is flooded with claims of "leaked" videos and exclusive content from countless creators. From vague references to "fishingwithluiza files" to searches for specific "lil tay leaked olf onlyfans accounts," the ecosystem of unauthorized distribution is vast and damaging. It operates on a simple, cruel premise: private moments become public commodities. This article dives deep into the reality behind the headlines, exploring the human cost of leaks, the legal battlefield, and the essential strategies for digital self-defense in an age where nothing feels truly secure.
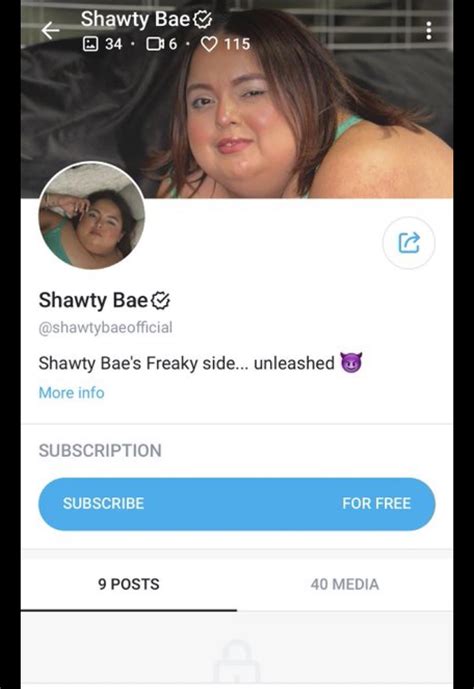
The Shawty Bae Phenomenon: A Case Study in Digital Exposure
The phrase "Shawty Bae leak has lengthy been a subject of concern within the digital age" points to a recurring narrative. "Shawty Bae" represents not necessarily one individual, but a archetype—a creator whose private content was allegedly shared beyond the bounds of their consent. The search queries themselves ("Search the best lil tay leaked olf onlyfans accounts," "Filter lil tay leaked olf onlyfans accounts") reveal a predatory demand for such material, treating human intimacy as a product to be filtered and consumed.
- Urgent What Leaked About Acc Basketball Today Is Absolutely Unbelievable
- Exposed How West Coast Candle Co And Tj Maxx Hid This Nasty Truth From You Its Disgusting
- West Coast Candle Cos Shocking Secret With Tj Maxx Just Leaked Youll Be Furious
Who is "Shawty Bae"? A Look at the Person Behind the Persona
While specific real-world identities are often obscured in these discussions, understanding the type of person targeted is crucial. Many affected creators are young women who built audiences on charisma, lifestyle content, or music, later expanding into more adult-oriented subscription services like OnlyFans for financial independence or creative control. The leak strips away their agency, reducing a multifaceted person to a single, exploited moment.
Bio Data: The "Shawty Bae" Archetype (Representative Profile)
| Attribute | Detail |
|---|---|
| Online Alias | Shawty Bae / Variants (e.g., associated with music or social media trends) |
| Primary Platform(s) | Instagram, TikTok, potentially Twitter/X, and subscription platforms (OnlyFans/Fansly) |
| Content Niche | Lifestyle, music promotion, fashion; later, adult content for subscribers |
| Audience | Primarily young adults, fans of hip-hop/rap culture, social media followers |
| The Violation | Alleged non-consensual sharing of private, explicit videos originally intended for a paying, consenting audience. |
| Impact | Severe reputational damage, emotional distress, harassment, potential doxxing, and loss of control over personal narrative. |
This table isn't about one verified person but illustrates the common profile of those targeted. The leak transforms a curated, consent-based business model into a chaotic, non-consensual free-for-all.
- Ai Terminator Robot Syntaxx Leaked The Code That Could Trigger Skynet
- Shocking Video Leak Jamie Foxxs Daughter Breaks Down While Playing This Forbidden Song On Stage
- Shocking Leak Exposed At Ramada By Wyndham San Diego Airport Nude Guests Secretly Filmed
The Anatomy of a Leak: How "Secret" Content Goes Public
The key sentences hint at a vast, underground network. Phrases like "Watch all the free free full length leaked exclusive members only extremely rare hardcore... videos" and "Hd free full length leaked exclusive members" are the siren calls of pirate websites and forums. These leaks rarely happen in isolation.
The Pipeline of Exploitation
- The Source: A leak can originate from a subscriber violating terms of service, a hacked account, a betrayed partner, or even a malicious insider. The sense of betrayal is compounded by the fact that subscribers often pay for access, creating a false sense of trust.
- The Aggregators: This is where sentences like "Watch the best hd porn videos, xxx pics, gifs, sex movies and photos on hq porner" become relevant. Dedicated piracy sites and Telegram channels specialize in scraping, re-uploading, and cataloging this stolen content. They use SEO-optimized titles and tags to attract traffic, profiting from ads on pages featuring non-consensual material.
- The Consumers: The searches—"justalissahere leaked onlyfans video," "madison bailey sex tape outerbanks video"—show the demand. Consumers, often driven by curiosity, a sense of getting something for "free," or malicious intent, fuel the market. Each click and view perpetuates the harm.
- The Permanent Record: As seen in "13:37 100% 1 year ago 1.3k hd she leaked her sex tape," the content never truly disappears. It is downloaded, re-uploaded, and archived across countless servers, making eradication nearly impossible.
Beyond the Shock Value: The Real Human and Legal Cost
It’s easy to get lost in the sensationalist language of the key sentences. The reality is far graver. The fallout from a leak is a cascade of trauma.
The Emotional and Social Aftermath
- Psychological Trauma: Victims commonly report symptoms of PTSD, severe anxiety, depression, and suicidal ideation. The violation is intimate and public simultaneously.
- Harassment and Stalking: Leaks invite relentless harassment, from cruel comments to targeted doxxing (revealing private addresses and information), as alluded to in posts like "Posted on 9/4/25 at 6:18 pm rico manning nola’s secret uncle member since sep 2025."
- Professional Ruin: For those with public careers or aspirations, a leak can mean immediate job loss, expulsion from school, or the end of future opportunities. The digital scarlet letter is hard to remove.
- Financial Loss: While some use platforms for income, a leak destroys the value of that paid content, directly attacking their livelihood.
The Legal Landscape: A Battle on Multiple Fronts
The law is struggling to keep pace. Victims can pursue several avenues:
- Copyright Infringement: The creator owns the copyright to their images/videos. DMCA takedown notices can be sent to websites, but the "whack-a-mole" nature of the internet makes this a relentless, costly process.
- Invasion of Privacy & Intentional Infliction of Emotional Distress: Civil lawsuits can be filed against the initial leaker and, in some jurisdictions, against websites that knowingly host non-consensual content.
- Criminal Revenge Porn Laws: Most U.S. states and many countries now have specific laws criminalizing the distribution of intimate images without consent. Penalties can include fines and imprisonment.
- Platform Violations: Reporting to the platforms hosting the content (social media sites, porn tubes) for violating their terms of service can lead to removals, but again, it’s a persistent fight.
The Unrelated Noise: Decoding the Signal in the Chaos
A strange element of the provided key sentences is their apparent randomness—references to Indiana basketball ("Indianas entire starting lineup nearly ag"), NCAA football transfers ("10,965 ncaa football players entered the portal"), and future football schedules ("9/19/2026 florida state at alabama"). This isn't an error; it mirrors the actual experience of searching for information on leaks.
How Misinformation and Distraction Spread
The digital ecosystem around leaks is polluted with:
- Clickbait and Misdirection: Titles like "I wonder if grubb is the secret sauce that made deboer" or lists of sports recruits ("Herzog | secrant.com not that this is secret, but here is the list of seniors...") are algorithmically placed to capture search traffic, burying legitimate information under irrelevant sports news.
- Fake Content & Deepfakes: The mention of "leaked pakistani leaked video leaked mms indian leaked..." highlights how the label "leaked" is applied to all manner of content, including potentially non-consensual material from different regions and contexts, and even fabricated deepfake pornography.
- Spam and Malware: Promises of "free full length leaked" videos are classic lures for malware, phishing scams, and subscription traps. The sentence "Hd fishingwithluiza files leaked porn vids at my porn here" is a textbook example of a spammy, malicious link description.
This noise is a tactic. It overwhelms the victim and the public, making it harder to find accurate information, support resources, or legal help. It also desensitizes people to the severity of the core issue.
Building Your Digital Fortress: Proactive Privacy Strategies
If you create content online, especially of an intimate nature, proactive defense is non-negotiable. Waiting until after a leak is a losing strategy.
Essential Security Protocols
- Watermark Everything: Discreet, unique watermarks (username, date) on every image and video make it easier to prove ownership and track leaks back to their source.
- Metadata is Your Friend: Ensure your camera or app adds copyright and ownership metadata to files. While not foolproof, it adds another layer of evidence.
- Strong, Unique Passwords & 2FA: Use a password manager. Every account, especially email and subscription platforms, must have a unique password and Two-Factor Authentication (2FA). Avoid SMS-based 2FA where possible; use an authenticator app.
- Vet Subscribers Carefully: While not always possible on large platforms, be mindful of who you grant access to. Be wary of new subscribers with blank profiles who ask for "special" content outside the platform.
- Secure Your Primary Email: Your email is the key to all your accounts. Secure it with the strongest possible password and 2FA.
- Regular Audits: Periodically Google yourself and your known aliases. Set up Google Alerts for your name and stage name to be notified of new appearances.
If a Leak Happens: The Immediate Action Plan
- Document Everything: Take screenshots of the URLs, dates, and any identifying information of the posters. Use archive.today to save pages.
- Report Aggressively: File DMCA takedowns with every hosting site, search engine (Google, Bing), and social media platform. Use their official reporting channels for "non-consensual intimate imagery" or "copyright infringement."
- Contact Authorities: File a report with your local police. Provide all documentation. Also, report to the FBI's Internet Crime Complaint Center (IC3) if the content is being hosted internationally.
- Seek Legal Counsel: Consult with a lawyer experienced in cyber law, privacy, or revenge porn statutes. They can send cease-and-desist letters and advise on civil suits.
- Secure Your Mental Health: Immediately contact a crisis helpline (like the National Suicide Prevention Lifeline: 988) or a therapist specializing in trauma. You are not alone, and the violation is not your fault.
The Societal Shift: Why This Everyone's Problem
The "Shawty Bae leak" narrative, and others like it, are symptoms of a larger cultural sickness. The ease of sharing, the anonymity of the internet, and the monetization of clicks have created an environment where privacy is constantly under siege.
Changing the Conversation
We must move beyond victim-blaming ("she shouldn't have taken the pictures") and focus on the perpetrator's choice to steal and share. The conversation must center on:
- Consent Education: Understanding that consent to one person (a subscriber) is not consent to the world.
- Digital Literacy: Teaching everyone, especially young people, about the permanent and replicable nature of digital data.
- Platform Accountability: Demanding that tech companies invest in proactive detection of non-consensual content, streamline reporting processes, and work with law enforcement swiftly.
- Legal Harmonization: Advocating for stronger, uniform federal laws (like the proposed Intimate Images Non-Consensual Distribution Act in the U.S.) to close jurisdictional gaps.
Conclusion: Reclaiming Agency in a Leaked World
The scattered key sentences—from the shocking to the bizarre—paint a picture of a digital Wild West. The alleged leak of "Shawty Bae" is not an isolated incident. It is one data point in a epidemic of non-consensual image sharing that destroys lives under the guise of "free content" or "secret tapes."
The path forward is twofold: defense and demand. On an individual level, we must treat our digital presence like our physical home—with robust locks, alarms, and caution about who we let inside. On a societal level, we must demand better from our platforms, our legal systems, and our own cultural attitudes toward privacy and consent.
The true "secret sauce" isn't in avoiding being targeted—it’s in building a world where such violations are met with swift justice, unwavering support for survivors, and a collective understanding that a person's body and intimacy are not public domain. The goal is not to live in fear of the next leak, but to build a digital ecosystem where privacy is respected as a fundamental right, not a precarious privilege. The conversation starts with recognizing the human being behind the headline and committing to the hard work of change.