Explosive Terre Haute OnlyFans Leak: Hidden Nude Photos And Explicit Videos EXPOSED!
Have you ever wondered what happens when private content meant for a select audience suddenly becomes public property for the entire internet to see? The recent buzz surrounding an "Explosive Terre Haute OnlyFans Leak" throws this terrifying scenario into sharp focus, highlighting the precarious reality for modern content creators. This isn't just a localized scandal; it's a symptom of a widespread digital vulnerability that affects thousands of creators on platforms like OnlyFans and Fansly every single day. When hidden nude photos and explicit videos are exposed without consent, the fallout extends far beyond initial embarrassment, spiraling into identity theft, relentless harassment, and profound reputational damage. Understanding this ecosystem—from the leak itself to the tools that track it and the legal shields available—is no longer optional for creators; it's a critical component of digital self-defense.
Understanding the OnlyFans Ecosystem: More Than Just a Platform
The OnlyFans Revolution: Empowering Creators
OnlyFans has fundamentally reshaped the relationship between creators and their audiences. Launched as a subscription-based platform, it allows artists, musicians, fitness trainers, and yes, adult content creators to monetize their work directly from their most dedicated fans. Its core appeal lies in inclusivity and creator autonomy. Unlike traditional social media algorithms that dictate reach, OnlyFans puts control firmly in the hands of the creator. They set their own subscription prices, decide what content to share, and engage with their community on their terms. This model has been particularly revolutionary for amateur porn creators, enabling many to build substantial, independent incomes by cultivating direct relationships with their audience. The platform's success is built on a promise of a more personal, secure, and profitable connection.
The Dark Side of Direct Monetization: The Leak Problem
This very directness and financial incentive, however, create a high-stakes target. Content that is paid for and shared within a "private" ecosystem is constantly at risk of being captured, copied, and redistributed without permission. This is where the problem of OnlyFans leaks originates. A "leak" can occur through a subscriber's deliberate action, a hacker compromising an account, a breach in the platform's security, or even through malicious software on a creator's own device. The content then proliferates across a murky network of dedicated leak sites, forums, and aggregation pages, often within minutes of its original posting. The initial "Terre Haute" reference in our keyword likely points to a specific, geographically-tagged leak event, but it represents a universal pattern: private content from any location can be stripped of its privacy and broadcast globally.
- Shocking Desperate Amateurs Leak Their Xxx Secrets Today
- Shocking Leak Exposes Brixx Wood Fired Pizzas Secret Ingredient Sending Mason Oh Into A Frenzy
- Traxxas Slash Body Sex Tape Found The Truth Will Blow Your Mind
The Leak Tracking Arsenal: Tools Like Chiliradar
For a creator, discovering their private content on the public web is a moment of panic. How do you even begin to find all the copies? This is where specialized tools become essential. Chiliradar is one such example of a free tool for content creators to find and track leaked content. Its primary function is to scan the vast expanse of the internet—particularly notorious leak sites and forums—for specific images or videos. By using image recognition technology or hash matching (a unique digital fingerprint of a file), creators can set up alerts. When their content is detected on a new site, they are notified. This allows for rapid detection before leaks spiral out of control. While tools like Chiliradar are crucial for monitoring, they are part of a broader strategy. Creators must also regularly perform manual searches using their stage names, real names, and unique identifiers on search engines and platforms known for hosting leaked material.
The Aggregation Problem: Sites Like Erome and Scrolller
Leaked content doesn't just sit on one site; it gets scraped and reposted across hundreds. Erome markets itself as "the best place to share your erotic pics and porn videos," but its open-upload nature makes it a major repository for leaked OnlyFans and Fansly material. The platform's tagline, "Every day, thousands of people use erome to enjoy free photos and videos," underscores its massive traffic, which in turn drives the demand for and visibility of non-consensually shared content. Similarly, sites like Scrolller.com operate as massive aggregators. The claim to "View 4 834 nsfw pictures and videos and enjoy onlyfansx with the endless random gallery on scrolller.com" and "Go on to discover millions of awesome videos and pictures in thousands of other" categories highlights their scale. These sites often operate in legal gray areas, protected by safe harbor laws that place the burden of copyright enforcement on the rights holder—the creator themselves.
The Real-World Consequences: Beyond a Simple Privacy Breach
The Domino Effect of a Data Leak
The consequences of an OnlyFans data leak are severe and multi-faceted. As outlined, they can include:
- Channing Tatums Magic Mike Xxl Leak What They Never Showed You
- Tj Maxx Gold Jewelry Leak Fake Gold Exposed Save Your Money Now
- Traxxas Battery Sex Scandal Leaked Industry In Turmoil
- Identity Theft & Account Hijacking: Leaked content is often accompanied by personal information (usernames, email fragments, location data). This can be used to attempt password resets on other accounts, commit financial fraud, or create fake profiles.
- Reputational Damage: For many creators, their OnlyFans work is separate from their personal or professional lives. A leak can erase that boundary, leading to loss of current employment, damage to future career prospects, and ostracization from family and community.
- Harassment & Blackmail: Once content is public, it invites targeted harassment, doxxing (publishing private address/contact info), and extortion. Perpetrators may demand money or more content under threat of further distribution.
- Psychological Trauma: The violation of having one's most intimate moments stolen and shared publicly leads to significant anxiety, depression, and PTSD.
Case Study: The Bella Thorne OnlyFans Incident
A high-profile example that brought mainstream attention to this issue involved actress and influencer Bella Thorne. In 2020, after joining OnlyFans and reportedly earning millions in a short time, explicit photos of hundreds of onlyfans performers, including bella thorne, have reportedly been leaked online by hackers. The alleged hack targeted a cloud storage service linked to her account. While the story dominated headlines, it's critical to note that Onlyfans has not confirmed the hack to dailymail.com, illustrating how rumors can spread and how platforms may be cautious in their public statements. Regardless of the specific technical details, the incident served as a stark warning: even celebrities with resources are not immune, and the "hacker" narrative often oversimplifies a problem that also includes malicious subscribers and insecure personal practices.
Proactive Protection: Document, Report, and Take Action
The Immediate Response Protocol
If a creator discovers a leak, time is of the essence. The first step is meticulous documentation. This means:
- Screenshot everything: Capture the URL, the date and time (visible in browser or via screenshot tool), the full page showing the infringing content, and any associated user comments or contact information.
- Record the URL: Use a URL shortener that tracks clicks if possible, or simply save the full link in a secure document.
- Note the platform: Identify the website, forum, or social media account hosting the content.
Legal and Platform-Based Reporting
With evidence in hand, the next phase is reporting.
- DMCA Takedown Notices: This is the primary legal tool for copyright infringement. A properly drafted DMCA notice sent to the website's hosting provider, the site administrator, and search engines like Google can force the removal of infringing content from search results and the site itself. Many platforms have dedicated copyright infringement report forms.
- Report to the Platform: If the leak is on a major social platform (Twitter, Reddit, Instagram), use their specific reporting tools for "Non-Consensual Intimate Imagery" or "Copyright Infringement."
- Law Enforcement: For cases involving extortion, threats, or clear criminal hacking, file a report with local police and potentially the FBI's Internet Crime Complaint Center (IC3). While they may not prioritize individual copyright cases, criminal threats are taken seriously.
The Legal Path: Protecting Your Rights
Learn how to document, report, and take legal action to protect your copyright, privacy, and digital rights. Beyond DMCA, creators have other avenues:
- Cease & Desist Letters: A formal letter from an attorney to the individual poster can often stop further distribution.
- Civil Lawsuits: For significant damages, a lawsuit for copyright infringement, invasion of privacy, or intentional infliction of emotional distress may be viable. The "Bella Thorne" scenario, where hundreds were affected, could potentially lead to a class-action suit.
- Injunctions: A court order can compel a website to take down content and prohibit future posting.
Navigating the "Caught" Culture and Accidental Exposure
The "Caught a YouTuber Being Revealing" Phenomenon
The phrase "Caught a youtuber being revealing" points to a common source of leaks: accidental or unsecured broadcasts. This can happen when a creator:
- Forgets to blur backgrounds or personal identifiers in videos.
- Accidentally posts to a public account instead of a private one.
- Has their screen shared or recorded without consent during a video call.
- Uses insecure cloud storage that gets hacked. This underscores that operational security (OpSec) is as important as platform security. Using strong, unique passwords, enabling two-factor authentication (2FA) on all accounts (email, cloud storage, social media), and being acutely aware of one's filming environment are non-negotiable habits.
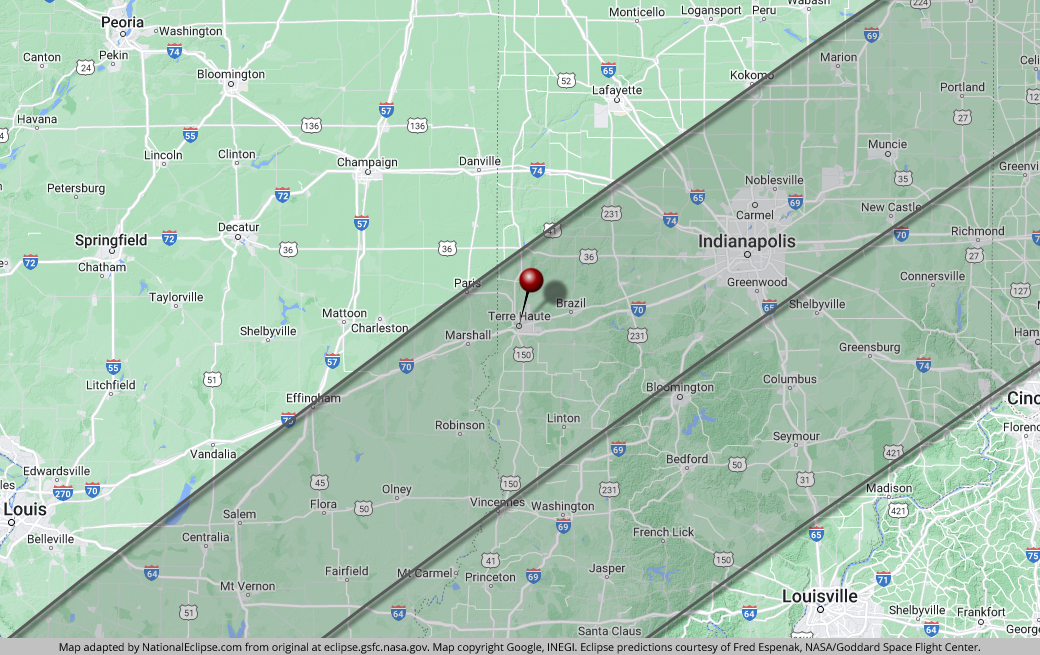
The "Terre Haute" Context: Location-Based Risks
While "Terre Haute" is a specific city, it symbolizes how leaks can have a local impact. A leak tagged with a location can lead to:
- Local Harassment: Community members may recognize the individual, leading to real-world stalking, shaming, or confrontation.
- Employment Consequences: If the creator lives and works in the same area, local employers or colleagues may discover the content.
- Family and Social Rupture: The hyper-local nature of the leak makes it nearly impossible to escape within one's immediate social circle. This amplifies the reputational and psychological damage exponentially.
Building a Resilient Digital Presence
Strategic Content Management
Prevention is the best cure. Creators should:
- Watermark Content: Subtle, persistent watermarks (username, logo) across all media make it easier to prove ownership and track leaks.
- Control Distribution: Never share original, high-resolution files. Use lower-resolution versions for previews and consider platform-specific tools that disable screenshots (where available, though not foolproof).
- Audit Your Digital Footprint: Regularly search for your stage name, real name, and aliases on Google and on known leak aggregators. Use tools like Chiliradar to automate this.
Mental Health and Support Systems
The emotional toll of a leak cannot be overstated. Creators should:
- Seek Support: Connect with other creators who have experienced leaks through online communities or support groups. Shared experience reduces isolation.
- Professional Help: Therapists specializing in digital trauma or sexual privacy violations can provide crucial coping strategies.
- Separate Self-Worth from Content: Remind yourself that a leak is a crime and a violation, not a reflection of your character or value.
Conclusion: Vigilance in the Age of Leaks
The "Explosive Terre Haute OnlyFans Leak" is not an isolated event but a chapter in the ongoing saga of digital privacy warfare. It exposes the harsh reality that content meant for a private, paying audience can become public property in an instant, with devastating consequences ranging from identity theft to psychological trauma. Platforms like OnlyFans empower creators economically, but they also place intimate assets directly in the crosshairs of a parasitic ecosystem of leak sites like Erome and Scrolller, which thrive on the aggregation of non-consensual content.
The path forward is one of proactive vigilance and empowered defense. Creators must arm themselves with knowledge: understand how leaks spread, utilize tracking tools like Chiliradar, and implement ironclad operational security. They must be prepared to act swiftly—documenting infringement, wielding the power of DMCA takedowns, and knowing when to escalate to legal authorities. The stories of high-profile figures like Bella Thorne remind us that no one is untouchable, but they also highlight the need for robust, creator-focused protections that go beyond platform policies.
Ultimately, protecting your digital rights is an ongoing process. It requires treating your content and your personal data with the same rigor as a financial portfolio. By combining technological tools, legal knowledge, and a strong support network, creators can navigate this treacherous landscape, mitigate damage when breaches occur, and continue to build their careers with greater resilience and control. The exposure of private content is a violation, but the response—informed, strategic, and united—can reclaim power and privacy.