Jenna Dewan's "Private" OnlyFans Videos LEAKED, This Is Worse Than Anyone Imagined
Have you ever typed a celebrity's name into a search engine, followed by words like "leaked" or "private," and felt a knot of uneasy curiosity in your stomach? You're not alone. This phenomenon has become a dark corner of the internet, a digital ghost town where privacy goes to die. But what if the reality of these leaks is far more complex, invasive, and dangerous than the sensational headlines suggest? The case of rumored private content from figures like Jenna Dewan isn't just about scandal; it's a stark lesson in digital vulnerability, the futility of online erasure, and the hidden traps waiting for the curious.
This guide dives deep into the unsettling world of private content leaks. We move beyond the gossip to explain how to realistically check if a private video was compromised, why most attempts to find it fail spectacularly, and why the search itself can be a perilous journey. We'll unpack the massive OnlyFans data breach that exposed terabytes of intimate material, analyze the celebrity allure driving fans to these platforms, and confront the grim reality of the clickbait ecosystem that profits from violation. This isn't a tutorial for finding leaks; it's a crucial warning about what lies beneath the surface.
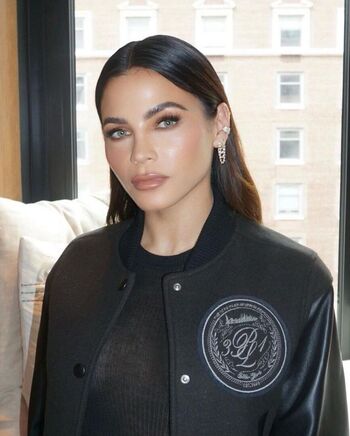
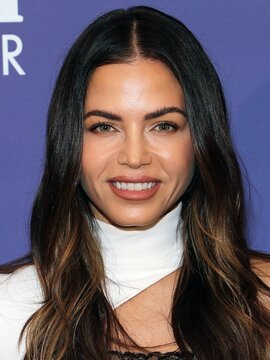
Jenna Dewan: From Dance Floor to Digital Spotlight
Before we dissect the leak narrative, it's essential to understand the person at the center of the speculation. Jenna Dewan is a multi-talented American actress, dancer, and producer whose career has spanned over two decades. She first gained widespread recognition as a dancer in music videos for artists like Justin Timberlake and Christina Aguilera before transitioning to acting. Her breakout role came in the 2006 dance film Step Up, where she starred alongside Channing Tatum, whom she later married. Her filmography includes titles like The Lincoln Lawyer, 10 Years, and Supergirl (where she played the villainous Reign). Beyond film, she has hosted television shows and produced projects, establishing herself as a versatile entertainer.
- Heidi Klum Nude Photos Leaked This Is Absolutely Shocking
- Viral Alert Xxl Mag Xxls Massive Leak What Theyre Hiding From You
- Maxxine Dupris Nude Leak What Youre Not Supposed To See Full Reveal
Her personal life, including her high-profile marriage and subsequent divorce from Tatum and her role as a mother, has been subject to intense media scrutiny. In recent years, like many celebrities and influencers, she has navigated the complex landscape of social media and direct-to-fan platforms. This visibility inevitably draws public curiosity, sometimes crossing into invasive territory when private content is rumored to be exposed.
Personal Details & Bio Data
| Attribute | Details |
|---|---|
| Full Name | Jenna Dewan Wold (née Dewan) |
| Date of Birth | December 3, 1980 |
| Place of Birth | Hartford, Connecticut, U.S. |
| Profession | Actress, Dancer, Producer |
| Years Active | 2002–Present |
| Notable Works | Step Up (2006), The Lincoln Lawyer (2011), Supergirl (TV, 2017-2018) |
| Marital Status | Divorced (from Channing Tatum, 2009-2019) |
| Children | 2 |
The Core Problem: Leaked Videos Defy Logic and Expectation
The problem is that leaked videos don’t behave the way people expect them to. There's a common fantasy: a private video is "leaked," it explodes across the web overnight, and anyone with an internet connection can find it with a simple search. This is a dangerous myth. The digital ecosystem is not a library; it's a fragmented, volatile, and heavily policed landscape.
When a leak occurs, the initial upload might happen on a obscure forum, a cloud storage link, or a torrent site. Within hours, platform moderators, copyright bots, and legal teams from the victim's representation begin a frantic game of whack-a-mole. Links are taken down, accounts are banned, and search engines de-index pages. The content doesn't become widely available; it becomes widely scattered and ephemeral. What remains are dead links, password-protected archives, and communities hoarding fragments. The expectation of instant, easy access is the first barrier that trips up most amateur investigators.
- One Piece Shocking Leak Nude Scenes From Unaired Episodes Exposed
- This Traxxas Slash 2wd Is So Sexy Its Banned In Every Country The Truth Behind The Legend
- Shocking Leak Nikki Sixxs Secret Quotes On Nude Encounters And Wild Sex Must Read
The Realistic Check: Why Most People Fail to Find Leaked Content
This guide explains how to realistically check whether a private video was leaked, why most people fail to find it. The failure isn't due to a lack of effort; it's due to a fundamental misunderstanding of the process.
- Search Engines Are Not Your Friend: Google and Bing aggressively filter explicit, non-consensual content. Using standard search terms will yield nothing but sanitized news articles about the alleged leak, not the content itself. You need to use specialized, often shady, search techniques for "deep web" forums, which carry their own risks.
- The "Digital Graveyard" Effect: Most initial uploads are removed within 48 hours. The content you might stumble upon weeks later is often reposted by third parties with poor video quality, watermarks, or corrupted files. You're not finding the "original"; you're finding degraded echoes.
- Access is Gated: Genuine, complete leaks are rarely free. They are traded in private Telegram groups, sold on crypto-marketplaces, or shared via invite-only Discord servers. Gaining entry requires trust, vouching, and often a fee. The casual searcher hits a wall immediately.
- The Misdirection of Clickbait: This is where sentences like "Hardcore porn of jenna jameson" or "Enjoy watching this nude beauty having fun" come into play. These are not leads; they are traps. They are generic, SEO-stuffed phrases designed to capture search traffic from people looking for any celebrity explicit content. Clicking them leads to:
- Malware-infested sites.
- Endless pop-up ads and scam offers.
- "Verification" pages that harvest personal data.
- Completely unrelated content, just using famous names as bait.
So you can still find it—but not in the way you imagine. If a leak persists, it's because it exists in these guarded, illicit ecosystems, far from the mainstream web.
The OnlyFans Catastrophe: A Breach of Biblical Proportions
The scale of the problem was made terrifyingly clear with a specific incident. Up to four terabytes of private images and videos linked to OnlyFans user accounts have been posted to the cloud sharing site Mega, the biggest privacy breach in the site's history. This wasn't a targeted hack of a few celebrities; it was a massive, indiscriminate data dump.
- What Happened? In 2020, a collective known as "DataNose" (and later others) began compiling and distributing a dataset reportedly containing content from thousands of OnlyFans creators. The data was scraped, likely through a combination of compromised creator accounts, subscriber leaks, and platform vulnerabilities. It was then uploaded to Mega.nz, a cloud storage service.
- The Scale: Four terabytes is an almost incomprehensible amount of data. It represents millions of images and videos from ordinary users and high-profile creators alike. The breach exposed the fundamental risk of any cloud-based content platform: if the data exists on a server, it can be copied and stolen.
- The Aftermath: While Mega has removed links when presented with legal takedown notices, the data had already proliferated across other file-sharing sites, torrent trackers, and private forums. For anyone whose content was included, the breach is permanent. "I remember her saying she'd private it soon after it was released" is a poignant, heartbreakingly common refrain from victims. They may have deleted content from their own account, but they cannot delete it from a stolen database circulating forever in the dark web.
The Hidden Dangers of the Leak Hunt
While it may appear straightforward to bump into leaked content material through forums or social media, most of those sources come with hidden dangers. The pursuit is fraught with peril far beyond the ethical violation.
- Malware and Ransomware: "Download" links are the number one vector for infecting your device. Keyloggers can steal passwords, ransomware can lock your files, and spyware can turn your webcam against you.
- Financial Scams: You'll encounter "premium" sites requiring a "small fee" for access, which then enroll you in recurring charges. Or "verification" sites that take your payment info and vanish.
- Data Harvesting: Many "leak" sites are run by data brokers. Simply visiting can install tracking cookies, harvest your email if you enter it to "comment," and sell your profile to spammers.
- Legal Exposure: In many jurisdictions, downloading or possessing non-consensual intimate imagery is a crime, regardless of how you obtained it. You could be charged with invasion of privacy or computer fraud laws.
- Psychological Harm: Confronting non-consensual content of a person you admire can be jarring and distressing. It objectifies and violates the subject, and can negatively impact the viewer's own perceptions of intimacy and consent.
The Celebrity OnlyFans Phenomenon & Its Dark Pull
Because OnlyFans is growing in popularity with memes and pop song references, more celebrities are heading over to make an account. What was once a niche platform is now a mainstream cultural touchstone. This normalization has a powerful, and often problematic, ripple effect.
In fact, celebrities and influencers often lure teens to OnlyFans by:
- Glamorization: Posting about their lavish earnings and "financial independence."
- Blurring Lines: Sharing suggestive but non-explicit content on Instagram/TikTok, then directing followers to a "more private" platform for the "real" content.
- Peer Pressure & FOMO: Creating a sense that subscribing is a rite of passage or a way to feel closer to an idol.
This creates a dangerous pipeline. Young, impressionable fans—"When jenna made her last video i was devastated, so i took some time going through her main account..."—develop parasocial relationships that can twist into a sense of entitlement to private content. The rumored "leak" of a celebrity's private videos becomes a twisted fulfillment of that perceived entitlement, a way to "get what they deserve" for not sharing enough publicly. "Honestly, can’t speak for the guys, but i found the “how girls do x” videos extremely relatable" might be a harmless comment on public content, but that same relatability can morph into a toxic justification for seeking out private, non-consensual material: "If she's so normal, why shouldn't I see this?"
The Apology Industrial Complex and Reaction Culture
There are some reaction channels and body language experts who gave their 2 cents and critiqued her apology. When a leak happens, the victim is often forced into a public apology—for being hacked, for trusting a partner, for existing in a digital space. This spawns a secondary economy of content.
- Reaction Videos: Creators will play "reaction" to the news of a leak, or worse, to the leaked content itself under the guise of "analysis." This capitalizes on the scandal while often re-victimizing the subject.
- "Body Language Experts": These figures will dissect the victim's apology video, claiming their eye movements or posture "prove" they are lying or not sorry enough. This adds a layer of pseudo-scientific shaming.
- The Critique Cycle:"Not sure if this means i’m very stereotypical or what, but while i respect her decision to take them down, i’d be..." This incomplete thought captures the conflicted, often hypocritical public sentiment. There's a performative respect for privacy paired with a personal disappointment at its enforcement. This cognitive dissonance fuels the continued search for the very content being condemned.
This culture turns a profound violation into a spectator sport, extending the harm for the victim and desensitizing the audience.
How to Realistically & Ethically Check for a Personal Leak (A Practical Guide)
Given the risks, why would anyone check? For victims, it's a grim necessity. For the curious, it should be a lesson in why not to. If you are a potential victim (e.g., you had private photos on a compromised platform), here is the realistic, safe approach:
- Use Dedicated, Reputable Tools: Do not use random Google searches. Use services like Google's "Remove Outdated Content" tool (for content already de-indexed but still showing in cached results) or HaveIBeenPwned (to check if your email was in a known breach like the OnlyFans one).
- Set Up Alerts: Create Google Alerts for your full name combined with terms like "leak," "OnlyFans," "video," "private." This notifies you of news articles or discussions about a leak, not the content itself.
- Reverse Image Search: If you have a specific photo you're concerned about, use TinEye or Google Images' reverse search function. This can find exact matches of that image anywhere on the web, including on shady sites.
- Monitor Deep Web Forums (Extreme Caution): This is where actual leaks are traded. Accessing these requires Tor browser and carries significant malware risk. This step is not recommended for the average person. If you must, do so on a isolated, secured virtual machine with no personal data.
- Legal Counsel is Non-Negotiable: If you discover a leak, your first call is to a lawyer specializing in cybercrime or privacy law. They can issue takedown notices (DMCA, GDPR, CCPA) more effectively than you can and advise on criminal reporting.
Remember: Finding a leak is not a victory. It's the first step in a long, expensive, and emotionally draining removal process that may never be 100% successful.
The Inescapable Truth: Once Digital, Forever Potential
The central, brutal truth is this: any digital content you create and share—even with a trusted platform, even with "private" settings—can be copied, stolen, and disseminated without your consent. The OnlyFans breach proved that the "private" vault is only as strong as its weakest security link and the trust of every person with access.
The promise of "privacy" on these platforms is a feature, not a guarantee. When you upload, you are trusting a corporation with your most intimate material. History shows that trust is frequently misplaced.
Conclusion: Respect Over Curiosity
The saga of rumored leaked videos, from Jenna Dewan to countless others, is not a mystery to be solved by the online masses. It is a symptom of a digital culture that prioritizes sensationalism over sanctity, curiosity over consent, and clicks over compassion.
The next time you feel that knot of curiosity, remember the hidden dangers: the malware waiting to infect your computer, the scams ready to empty your bank account, and the very real human being whose violation you are entertaining. The "leak" isn't just a video; it's a permanent scar on someone's sense of safety and autonomy.
The most powerful action you can take is to redirect your search. Search for information about digital privacy rights. Search for resources supporting victims of image-based abuse. Search for stories about the real consequences of these breaches. Turn the innate human curiosity that fuels the leak economy into a force for education and empathy. Because in the end, the search for private content says far more about the searcher than the subject. Choose to be better.