YOU WON'T BELIEVE THE LYNARITAA ONLYFANS LEAKED CONTENT!
What happens when private content meant for a paying audience suddenly becomes public knowledge? The recent alleged leak of content from the creator known as LYNARITAA has sent shockwaves through online communities, sparking intense debates about digital privacy, platform security, and the very real consequences of content distribution in the modern age. This incident serves as a stark, modern-day cautionary tale for every content creator, subscriber, and everyday internet user. It’s not just about one person's private material; it’s a critical case study in managing your digital footprint, securing your accounts, and understanding the tools at your disposal to protect your online identity. We will dive deep into the situation, explore who LYNARITAA is, and, most importantly, translate the scattered technical advice from various platforms into a actionable blueprint for digital self-defense.
The Story Behind the Name: Who is LYNARITAA?
Before dissecting the leak, it’s crucial to understand the individual at the center of the storm. The persona "LYNARITAA" is primarily associated with Kalani Rodgers, a content creator who has leveraged platforms like OnlyFans to share exclusive material with a dedicated subscriber base. Her journey highlights the dual-edged sword of creator economies: direct audience connection paired with significant personal and security risks.
Personal Details & Bio Data
| Attribute | Details |
|---|---|
| Primary Online Alias | LYNARITAA |
| Real Name | Kalani Rodgers |
| Primary Platform | OnlyFans |
| Content Niche | Exclusive lifestyle and personal content for subscribers |
| Public Persona | Maintains a distinct boundary between her public social media and private subscriber content. |
| Key Incident | Alleged large-scale leak of private OnlyFans content to public domains. |
Rodgers' decision to join OnlyFans, as hinted in the key sentences, was a strategic move to monetize her personal brand and connect with fans on her own terms. The platform’s promise of controlled, subscription-based access is a major draw for creators. However, as this incident brutally demonstrates, that control can be shattered in an instant, turning private galleries into public archives without consent.
- Exxonmobils Leaked Sex Parties How The Oil Corps Top Brass Are Exposed
- Viral Thailand Xnxx Semi Leak Watch The Shocking Content Before Its Deleted
- Whats Hidden In Jamie Foxxs Kingdom Nude Photos Leak Online
The Anatomy of the LYNARITAA Leak: What We Know
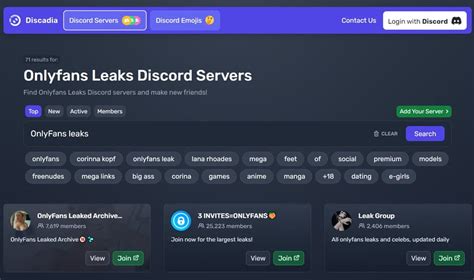
The core of the viral phrase "LYNARITAA OnlyFans leaked" refers to the unauthorized distribution of content originally posted behind a paywall. While the exact mechanics of such leaks are often complex, they typically involve a subscriber using screen recording software, exploiting platform vulnerabilities, or, in some cases, a security breach within the creator's own account. The fallout is immediate and devastating:
- Loss of Revenue: The fundamental business model of subscription platforms collapses when the exclusive product is available for free.
- Violation of Trust: The intimate contract between creator and subscriber is broken, leading to profound feelings of betrayal and exploitation.
- Psychological Toll: For the creator, it’s a severe invasion of privacy, leading to anxiety, harassment, and a constant feeling of being watched.
- Permanent Digital Footprint: Once leaked, content is nearly impossible to fully erase from the internet, proliferating across forums, file-sharing sites, and social media.
This event underscores a brutal truth: no platform is 100% immune to leaks. Your security is a layered practice, not a single setting.
Your Digital Command Center: Managing Your Watch History & Presence
In the wake of such a leak, both creators and general users must become experts in managing their own digital histories. The key sentences provide a scattered map to various control panels. Let's assemble that map into a coherent guide.
- Taylor Hilton Xxx Leak Shocking Video Exposed
- Shocking Xnxx Leak Older Womens Wildest Fun Exposed
- Shocking Tim Team Xxx Sex Tape Leaked The Full Story Inside
Finding Your Activity: The "You" Tab and Channel Name
A critical first step in auditing your digital life is knowing where your activity is stored. On platforms like YouTube, you can find this option under your channel name. Clicking your profile picture in the top-right corner opens a menu that is your gateway to privacy and history settings. This is your digital command center.
From there, navigating to the "You" tab (often found by clicking "Guide" or the hamburger menu, then selecting "You") consolidates your personal activity. This includes your watch history, liked videos, and subscriptions. Understanding this layout is non-negotiable for anyone serious about online privacy.
The Power and Peril of Watch History
History videos you've recently watched can be found under history. This simple statement holds immense power—and risk. Your watch history is a detailed log of your interests, curiosities, and even your private moments. For a creator like LYNARITAA, a compromised account could expose not just her uploads, but her own viewing habits, revealing research, personal interests, or private videos she watched.
YouTube watch history makes it easy to find videos you recently watched, and, when it’s turned on, allows us to give relevant video recommendations. This convenience comes at a cost: it creates a rich data profile. You can control your watch history by deleting or turning it off. This is a primary defense. Regularly clearing your history or pausing it entirely prevents the accumulation of a detailed log that could be exploited if your account is ever breached. Make it a monthly habit.
Fortifying Your Core: Gmail and Account Security
Your email is the master key to your entire digital kingdom. If an attacker gains access to your Gmail, they can reset passwords for every other account, including your OnlyFans, YouTube, and social media.
Before you set up a new gmail account, make sure to sign out of your current gmail account. This is crucial on shared or public computers. But more importantly, for your existing, primary account:
- From your device, go to the google account sign in page.
- Ensure you are signed out on all devices you no longer use.
- Learn how to sign out of gmail properly on every browser and app.
- Enable Two-Factor Authentication (2FA) immediately. This is your single most important security step.
- Review "Your devices" under your Google Account security settings and remove any unfamiliar ones.
The Multi-Account Lifestyle: Switching with Intention
Many creators and power users separate their personal, professional, and creator accounts. Switch accounts to switch the account that you’re using, click switch accounts. This feature is a privacy essential. Always double-check which account you are logged into before posting, liking, or commenting. A stray comment from your personal account on a sensitive post can have real-world consequences. Develop the muscle memory to verify your active account.
The Last Line of Defense: Official Help Centers
When in doubt, go to the source. The Official youtube help center where you can find tips and tutorials on using youtube and other answers to frequently asked questions is an invaluable resource. The same applies to Official youtube for families help help center where you can find tips and tutorials on using youtube for families help and other answers to frequently asked questions, which covers stricter content controls and supervised experiences.
These centers are maintained by the platforms themselves and provide the most accurate, up-to-date information on privacy settings, reporting leaks, and account recovery. Bookmark them. For broader Microsoft ecosystem issues, Get help and support for microsoft edge through its official channels to secure your browsing data and passwords.
The Workplace Variable: When Your Admin Holds the Keys
If you're using a work or school account and couldn't install classic outlook following the steps above, contact the it admin in your organization for assistance. This sentence is a powerful reminder that not all accounts are under your sole control. If you use a managed device or account for any part of your content creation or personal business, your organization's IT department controls many security settings. You must communicate with them about your privacy needs. They may have policies that conflict with the use of certain platforms or the installation of security tools. Transparency with your IT admin is part of your security strategy.
The Broader Ecosystem: YouTube Music and Beyond
The mention of the youtube music app, you can watch music videos, stay connected to artists you love, and discover music and podcasts to enjoy on all your devices is a reminder of our interconnected digital lives. Your activity on YouTube Music is also part of your Google Account history. The same principles apply: review your listening history, manage your data, and understand that your tastes and habits are being logged across all Google services. This holistic view of your data is essential for true digital hygiene.
Building Your Personal Security Protocol: An Action Plan
Based on the foundational advice scattered through our key sentences, here is a consolidated, actionable protocol:
- Audit Your History: Go to your main platform settings (found under your channel name or in the "You" tab). Review and delete your watch/search history on YouTube, Google, and any other service. Consider pausing history where possible.
- Master Account Switching: Make a ritual of checking your active profile. Use the switch accounts feature deliberately. Never assume you're on the right account.
- Secure Your Email: This is your #1 priority. Sign out everywhere, enable 2FA, and review connected apps and devices. Learn how to sign out of gmail properly and do it on old machines.
- Leverage Official Help: Don't rely on random forums. Bookmark the Official YouTube Help Center and equivalent centers for every major platform you use. They have the correct steps for reporting leaked content and tightening privacy.
- Know Your Boundaries: If you use a work or school account, understand its limitations. Contact the IT admin for your organization to clarify what you can and cannot do regarding personal platform access and security software.
- Educate Yourself Continuously: The digital landscape changes fast. Regularly visit help centers for updates on new privacy features or threats.
Conclusion: The Leak is the Message
The alleged LYNARITAA OnlyFans leaked content scandal is more than tabloid fodder. It is a stark, high-profile lesson in the fragility of digital privacy. The technical steps—finding settings under your channel name, managing your history, switching accounts carefully—are not mundane chores. They are the fundamental practices of digital self-defense.
Whether you are a creator like Kalani Rodgers or a private individual, your data is valuable and vulnerable. The tools to protect it are available, but they require proactive, informed use. Don't wait for a leak to happen to you. Start today: open that settings menu, clear that history, and enable two-factor authentication. Your future, private self will thank you. The internet's memory is permanent; your control over your own story must be deliberate and constant. Take back your digital narrative, one setting at a time.